At an exercise in Boston that imagined a cyber attack designed to disrupt an important election in a “swing state,” voting machines were not an issue.
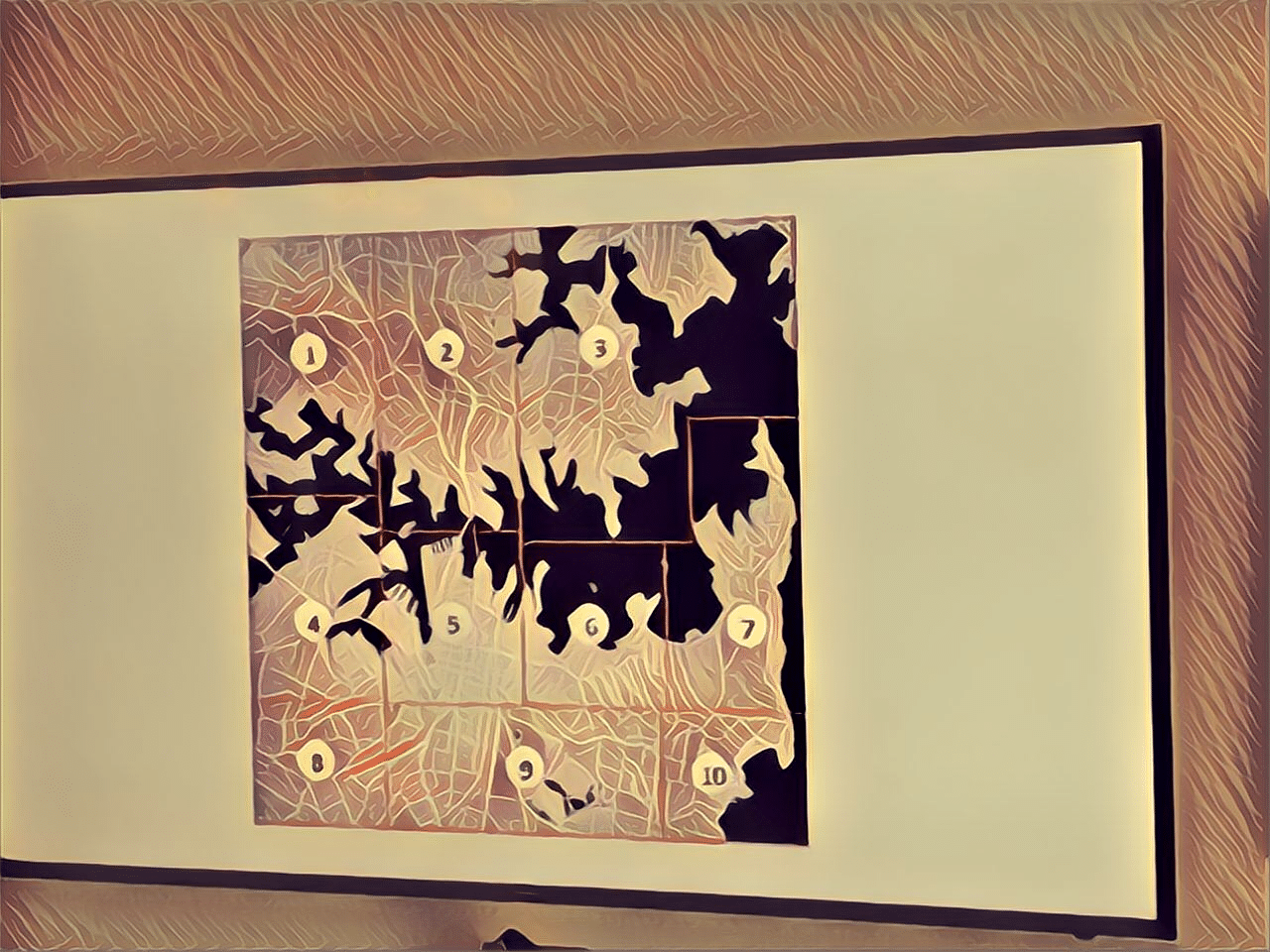
It’s election day in Nolandia, an imaginary, mid-sized U.S. city in a key “swing” state, and things are not going as planned – at least for government officials.
The day started with snarled traffic and a suspicious outage of the 9-1-1 emergency call center that has put the public and first responders on edge. Already, the city’s police force was taxed keeping tabs on protests tied to a meeting of the International Monetary Fund.
By afternoon, the federal Emergency Alert System (EAS) was warning Nolandia residents of massive natural gas leaks in neighborhoods in the north and west part of the city, prompting officials to order evacuations of the affected areas.
Later, bomb threats called in to local television stations shut down a bridge linking the northern and southern halves of the city – a major artery for vehicles. The EAS warning turns out to have been false – no gas leaks are detected, nor is any bomb found on the bridge. Later in the day, cyber attacks on a smart traffic light deployment in Nolandia snarl traffic further and sow chaos during the evening commute. In the meantime, the “Broken Eagle Task Force” (or BETF), a shadowy hacking collective protesting the ‘global order,’ has taken to social media to take credit for the mayhem.
This is election hacking 2018 style: a highly successful operation in which no voting machines or voting infrastructure were compromised, attacked or even targeted.
“A lot of press and scrutiny have been given to the voter rolls and the voting machines since 2016 as a result of what the Russians did,” said Ross Rustici of Cybereason, who was the mastermind of the tabletop exercise. “We wanted to expand that scope and demonstrate that the threat landscape is actually much broader than those very specific vulnerabilities.”
The ranks of the BETF were filled by Cybereason employees as well as employees of the City of Boston and representatives from Boston College’s Cyber Security program. Opposite them, the Blue Team included members of the local office of the FBI, the Massachusetts State Police and police from the City of Lowell, north of Boston.
Political goals not a priority for defenders
The outcome of the exercise was at once predictable and surprising – both worrying and reassuring, participants said. On the one hand: the imaginary BETF hacking crew was successful in sowing chaos in the environs of Nolandia: clogging streets, prompting hurried evacuations of residential neighborhoods and sending first responders scampering to address phantom threats.
“I would say at the end of the day (the Red team) had the lead,” Rustici said.
The Blue Team, representing city officials and public safety officers, remained cool headed throughout the exercise: focused resolutely on ensuring public safety and communicating accurately with the public – even if the political dimension and ramifications of the days events escaped notice.
“Blue focused solely on the things that they had the power to effect. They made assumptions that DHS, FBI the broader organizations of the state would do their jobs as well,” said Rustici. “They were purely responding to the real world effects of them and trying to control the message…trying to respond to the gas leaks that were reported. And trying to handle the things that came at them using the powers they had.”
“Red team is winning, until the handcuffs come out,” joked Tom Mahon of the Massachusetts State Police.
Faced with a fast moving cyber threat with political motives and ends, a-political public servants behaved…apolitically: doing their jobs, irrespective of the political motives of attackers or the political consequences of the attacks.
Still, the attackers use of social media to spread misinformation challenged the public officials. Craig Withycombe of the Lowell Police Department said that the “its very tough for a local municipality to deal with something that is worldwide.” His team, for example, had to contend with misleading social media posts that were circulated by compromised local media outlets.
Weaponizing disinformation
“That’s very hard to combat. In a situation where there’s a real emergency, people will turn the television on,” he said.
See also: As Election Threats Mount, Voting Machine Hacks are a Distraction
“Information was far more effective in many cases than what we able to do with the physical infrastructure. There wasn’t that much that was uniquely cyber,” said Cybereason Chief Product Officer Sam Curry, part of the Red Team representing the BETF hacking group.
That was all part of the plan to underscore the different methods that might be used to influence the outcome of an election, said Rustici of Cybereason. “We wanted to explore the second order effects. So if a hacking group wanted to effect the outcome of an election and undermine the voters confidence in the process itself, what other levers did they have available to do that?”
Blue team member Ed Davis, a consultant who works on public safety planning with public sector organizations, said that the exercise revealed that there was “room for improvement” in public sector planning for cyber incidents.
Cities like Boston need to prepare as carefully for cyber attacks as for physical attacks and natural disasters, Davis said.
See also: Voting Machine Maker Defends Refusal of White-Hat Hacker Testing at DEF-CON
“These are low cost, high impact threats…that could have a significant impact on something as vital to our society as a vote,” he said.
One unavoidable conclusion is that public officials and first responders need to be more attuned to the possible political dimensions of cyber incidents and to tap resources that are available to them at the state and federal level, Curry said.
“The way in which this election was manipulated is more a matter of ‘when’ than ‘if,'” Rustici said.

Pingback: In Boston: Election-Hacking War Game Bypasses Election Systems - Doers Nest
Pingback: In Boston: Election-Hacking War Game Bypasses Election Systems - R- Pakistan Daily Roznama
Pingback: In Boston: Election-Hacking War Game Bypasses Election Systems - f1tym1
Pingback: In Boston: Election-Hacking War Game Bypasses Election Systems - Wiki Blog
Pingback: In Boston: Election-Hacking War Game Bypasses Election Systems » @FinTechLog