Human rights organization Amnesty International reports it’s been the target of a spyware campaign traced to a secretive Israel cyber-surveillance company and distributed through the chat application WhatsApp.
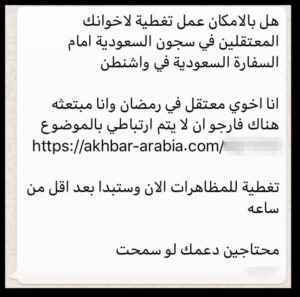
An Amnesty International staff member in June received a WhatsApp message that contained clickbait regarding a Saudi Arabian protest, as well as links the organization believe are used to distribute and deploy mobile spyware from the Israeli surveillance vendor NSO Group, the organization said in a blog post.
After analyzing the messages, Amnesty International discovered connections with a network of more than 600 domain names that overlap with infrastructure previously identified as part of Pegasus, a commercial exploitation and spyware platform sold by NSO.

Pegasus can be used to record conversations and gain access to photos and text messages on a smartphone, as well as websites viewed by the device. A Saudi activist based abroad had also received similar malicious messages connected to Pegasus, according to Amnesty International.
“This malware would allow an attacker complete access to the target’s phone or computer, essentially turning the device into a sophisticated eavesdropping and tracking tool to be used against them,” the organization said in the post.
The WhatsApp message, in Arabic, asked the staff member to cover a protest “for your brothers detained in Saudia Arabia in front of the Saudi embassy in Washington,” with a link supposedly containing information about the protest aimed at baiting the receiver into clicking to install malware.
“Cover the protest now it will start in less than an hour,” the message read. “We need your support please.”
“The message was clearly an attempt to trick our colleague into clicking on the link, which pointed to a domain name akhbar-arabia[.]com,” according to Amnesty Interational. “We discovered this domain to belong to a large network infrastructure that has been previously documented to be connected to the Israeli surveillance vendor, NSO Group.”
Spyware turned malware
NSO Group is a highly secretive surveillance technology manufacturer that sells its platforms to government agencies for counter-terrorism activities. It’s previously been linked to some sketchy cyber activity–namely, a 2016 incident in which the company used Pegasus to exploit flaws in iPhones and expose sensitive data and files with a single text message, forcing Apple to issue a quick fix.
Still, the company itself does a legitimate mobile surveillance technology business, something NSO Group officials reminded Amnesty International in a message when contacted about the suspicious activity, according to the organization.
“Our product is intended to be used exclusively for the investigation and prevention of crime and terrorism,” the company said in the message. “Any use of our technology that is counter to that purpose is a violation of our policies, legal contracts and the values that we stand for as a company.” NSO said it would investigate Amnesty’s claims that its platform is being used to spread malware and “take appropriate action” if necessary.
Amnesty International said its analysis of the incidents uncovered sound evidence that the malicious messages are connected to Pegasus, based on three connections they uncovered to the platform. For one, the behavior of the servers linked to the messages match NSO Group’s description of Pegasus found in a document describing the product leaked in 2015 by Italian spyware vendor, Hacking Team. There also is evidence that connects the malicious links Amnesty International and other activists received with NSO Group network infrastructure previously discovered and publicly reported on by Canadian research group, Citizen Lab.
The third piece of evidence connecting NSO to the spyware campaign is a domain registration pattern that shows most of the domains in the attack infrastructure were registered during Israeli working days and hours, where the company is based, according to Amnesty International. While even the group acknowledges that this piece of evidence is “speculative,” they were able to devise a way of fingerprinting servers related to the malicious messages.
Using the fingerprint, the investigation team conducted a probe of Internet-facing servers and identified more than 600 servers that demonstrate behavior similar to the servers in the malicious messages, akhbar-arabia[.]com and social-life[.]info, according to the blog post. The servers also appear to be region-specific, with links to countries such as Zambia, Russia and Latvia, the organization said.
“Among these we found servers that hosted domain names that have been previously identified as connected to NSO Group by Citizen Lab and others, specifically banca-movil[.]com, pine-sales[.]com, and ecommerce-ads[.]org,” the group said.
History of cyberattacks
Amnesty International is no stranger to being a target of malicious cyber actors. The agency long has been in the crosshairs of attackers mainly from countries where the organization defends citizens’ human rights.
Earlier this year in May, Amnesty International reported a different spyware attack on its human rights activists in Pakistan that uncovered a network of attackers using fake online identities and social media profiles to bait activists and mark them out for surveillance and cyber crime, the group said.
In 2012 it was pro-Syria attackers targeting the organization, this time by hacking the Amnesty International website and posting items that falsely accused the rebels of a string of atrocities.
The company used the latest attack not only to decry the use of spyware against its mission, but again defend its human rights efforts around the world, especially in places where its actions are unwelcome.
It also warned of the long-term, negative social and political effect that the misappropriated use of surveillance technologies in spyware attacks against civil rights watchdogs could have.
“We all have the right to associate, communicate and share information about human rights threats, issues and violations related to ourselves or to others,” the organization wrote. “The unchecked use of surveillance technologies such as those produced by NSO Group can have a serious silencing effect on civil society.”

