Researchers at the security firm CheckPoint are warning that code to attack a vulnerability in Huawei HG532 home routers has been leaked online and is linked to attacks by the Satori botnet.
In a blog post, the Check Point Research Team said that hundreds of thousands of attempts to exploit a previously unknown (or “zero-day”) vulnerability in the Huawei home router HG532 have been detected. The attacks are linked to a new Internet of Things botnet, dubbed Satori, which is an updated variant of Mirai.
CheckPoint said that an amateur threat actor under the nickname ‘Nexus Zeta’, seemed to be behind this new botnet creation attempt. Described as a “script kiddie” (or unskilled hacker) he has been active in hacker forums seeking advice on basic tasks such as how to build such an attack tool.
Huawei has patched the vulnerability and update their customers.
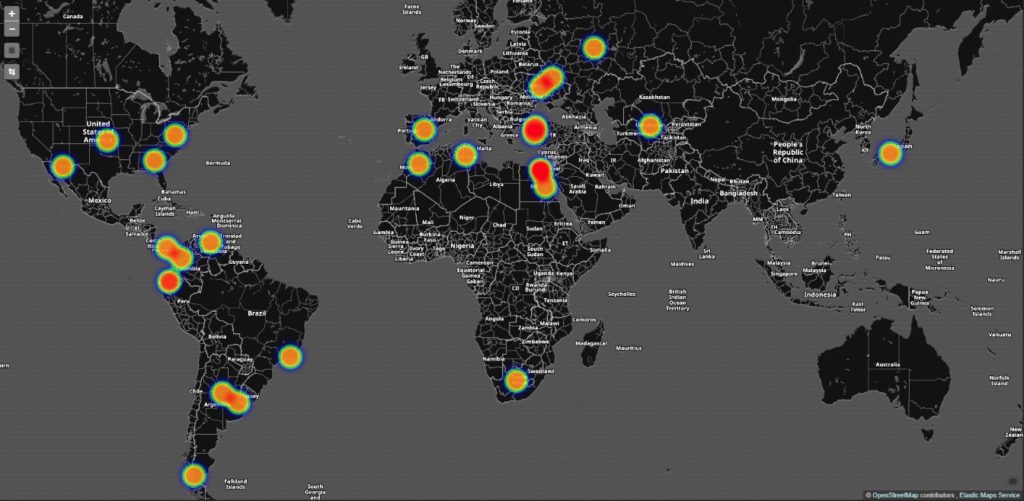
First identified in August, Satori updates the Mirai botnet code and targets IoT devices, the Satori version targets port 37215 on Huawei HG532 devices. The attacks exploit CVE-2017-17215, a vulnerability in the Huawei home router that exposes a local network configuration to the public Internet via WAN port 37215 (UPnP – Universal Plug and Play). Attacks were spotted in the USA, Italy, Germany and Egypt.
[Read more Security Ledger coverage of botnets.]
Working code to exploit the flaw was discovered on Pastebin in the last week and has been used in botnet attacks by Satori and Brickerbot in recent weeks, according to a blog post published by Ankit Anubhav a researcher at the firm NewSky Security.