In this industry perspective, Dan Larson of the firm CrowdStrike argues that antivirus software is becoming less effective at stopping damaging cyber attacks, but that companies need to look before they leap when replacing it.
![]() Headlines this summer were buzzing with coverage of cyber attacks and reports of organizations that fell victim to them – often despite having traditional antivirus (AV) technology in place. The success of many recent attacks makes two things clear – hackers have adapted their techniques and tactics to outpace traditional AV, and their attack methods have become more evasive.
Headlines this summer were buzzing with coverage of cyber attacks and reports of organizations that fell victim to them – often despite having traditional antivirus (AV) technology in place. The success of many recent attacks makes two things clear – hackers have adapted their techniques and tactics to outpace traditional AV, and their attack methods have become more evasive.
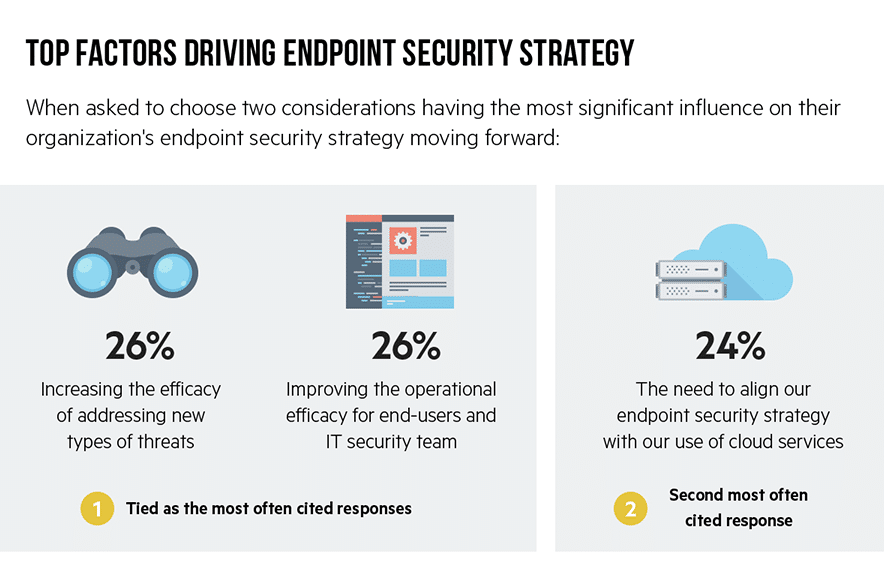
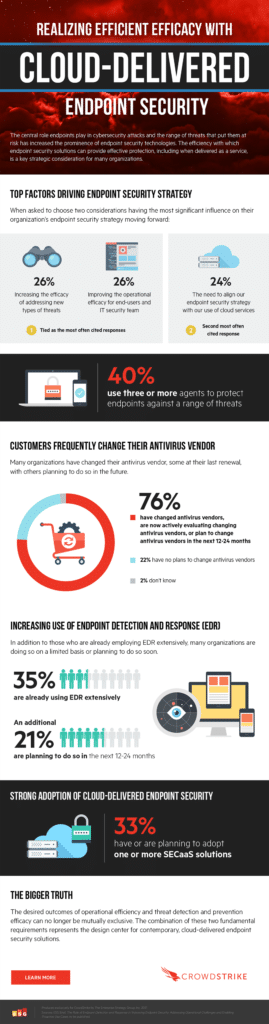
As we approach Q4 and move closer to 2018, many organizations want to know that their threat prevention is effective against quickly evolving threats, If not, they want to know what they should consider when replacing their current solution. In fact, according to a recent ESG survey, 45% of respondents agreed that they will need to switch vendors to improve their endpoint security posture.
Antivirus is falling short. Why?
First, let’s look at why traditional AV is falling short against the cyber-attacks organizations face today. Traditional AV technologies still rely on a signature-based approach that can only identify known threats. Attackers can run circles around this approach by making small tweaks to their malware in between signature updates; this allows them to operate with impunity while organizations scramble to deploy new updates. In short, traditional AV leaves organizations one step behind the attacker. Making matters worse, a signature-based approach cannot detect modern attacks that do not write files to disk (so called file-less attacks) or techniques that use trusted system tools like PowerShell to perform malicious actions. In order to combat the shortcomings of traditional AV, organizations must ensure that they have AV technology that takes a proactive approach to cybersecurity.

These next-generation AV technologies apply new techniques such as machine learning and behavioral analytics that go far beyond identifying known threats. Instead of constantly trying to update lists of known-good and known-bad things, they take a more fundamental approach. Machine learning models determine a file’s maliciousness with no previous knowledge of the file, relying instead upon analysis of the file’s innate properties. Behavioral analytics abstract the analysis to a level that is indifferent to a file or application’s reputation or intent, and instead observes the actions taken and stops them in their tracks if they resemble actions known to be used by attackers. Adding behavioral analytics to a prevention strategy built on machine learning is the key to raising the bar in endpoint protection. Together they represent the new standard in endpoint security, one where more attacks are stopped and all attacks are identified and remediated before they can do damage.
What to consider when replacing antivirus
With the shortcomings of traditional AV in mind, there are a few things organizations must consider when evaluating their current security infrastructure and AV solution:
- First, an organization must assess the maturity of their cybersecurity efforts and determine if they have any “pre-existing conditions.” The fastest way to check for any current network vulnerabilities or suspicious activity within the network (or pre-existing conditions) is by conducting a compromise assessment. We always advise organizations to assume that they have been compromised.
- Following the initial assessment, an organization can determine the shortcomings of their current security and what exactly needs to be done to reduce its cyber risk. Conducting this risk assessment also goes hand-in-hand with an organization defining its security goals. Changing any technology in your infrastructure should only take place if there are clear benefits to be gained compared to what is already in place. If you are going to replace your current AV, the next-generation solution should provide better protection, better performance and be easier to implement. It should also create opportunities to eliminate complexity in your security architecture and consolidate endpoint agents.
- If replacing current AV or other security technology is necessary to accomplish an organization’s cybersecurity goals, the next thing to consider is time-to-value and the ease of replacement. Many large organizations are reluctant to bog down their systems and risk negative impact on performance. They are also concerned about the complexity of the management infrastructure and its ability to scale to meet their needs. When considering which technology to replace your AV with, consider how long it takes to deploy and what it will require from internal IT resources. If it will take months to deploy new endpoint protection and significant resources, the benefits and cost may not be worth it for that particular solution.
Other areas an organization should consider when deciding on the best solution to replace their AV is whether the new solution has been tested for efficacy and compliance. Also consider whether it can seamlessly integrate with other security technology like security monitoring, analytics and orchestration solutions. This is a critical consideration. According to the same ESG study, lack of integration and automation between tools is one of the top three endpoint security challenges for organizations.
With attackers adapting their techniques to take advantage of ineffective AV solutions, now is the time for organizations to evaluate whether their current technology is sufficient. By conducting a risk assessment, establishing endpoint security goals and then assessing what next-gen AV solution might be the right fit, organizations can enhance their protection and take meaningful steps to prevent a breach and keep their name out of the headlines.