Hackers working on behalf of the government of Iran are using alluring social media profiles featuring a young, English photographer to entice and then compromise the systems of high value targets in the oil and gas industry, according to a report by Dell Secureworks.
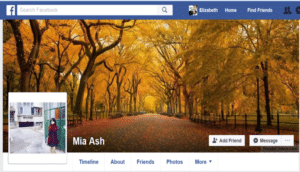
In a report released on Thursday, Secureworks’ Counter Threat Unit (CTU) said that it observed an extensive phishing campaign beginning in January and February 2017 that used a polished social media profile of a young, English woman using the name “Mia Ash” to conduct highly targeted spear-phishing and social engineering attacks against employees of Middle Eastern and North Africa firms in industries like telecommunications, government, defense, oil and financial services. The attacks are the work of an advanced persistent threat group dubbed COBALT GYPSY or “Oil Rig” that has been linked to other sophisticated attacks.
The attacks, which spread across platforms including LinkedIn and Facebook, as well as email, were highly successful. In some cases, the attacks lasted months – and long after the compromise of the employee – with the targets engaged in a flirtation with a woman they believed was a young, attractive female photographer.
The Mia Ash persona is a fake identity based loosely on a real person -a Romanian photographer and student who has posted her work prolifically online. According to CTU researchers, the persona was created specifically with the goal of perform reconnaissance on and establishing relationships with employees of targeted organizations. Victims were targeted with the PupyRAT Trojan, an open source, cross-platform remote access trojan (RAT) used to take control of a victim’s system and harvest credentials like log ins and passwords from victims.
The malicious software was delivered as shortened URLs that, when clicked, caused a Word document to download and attempt to run a macro. The macro ran a PowerShell command that attempted to download additional PowerShell loader scripts for PupyRAT.
Secureworks got wind of the campaign after noticing a spike in PupyRAT detections on their monitoring systems and began investigating in January, according to Allison Wikoff, a security analyst at Secureworks. When most of those efforts failed, the COBALT GYPSY group commenced the phishing campaigns.
“We saw this ‘Mia Ash’ persona reach out to targets about two weeks after the first campaign happened,” Wikoff said. “They used this persona as another way to get into the organization.”
The targets Secureworks involved were all male, and between 20 and 40 years old. “This is an age-old trick. You have an attractive and young woman reach out and strike up a conversation,” Wikoff said.
After the back and forth on LinkedIn, the Mia Ash persona would quickly move conversation over to Facebook, Wikoff said. That decision may reflect concern about LinkedIn’s monitoring of suspicious profiles, or it could simply reflect the desire of the COBALT GYPSY group to foster intimacy and trust with its targets, Secureworks believes.
While the initial contact with targets presented Mia Ash as a wedding and portrait photographer who was “reaching out to people around the world,” the interactions quickly turned personal and intimate, Secureworks said, though there is no evidence that attempts were made to contact targets in person.
The attacks played out over a number of weeks, with an individual identified as “Victim B” befriended by the Mia Ash profile weeks after the initial spear phishing run failed. Within weeks of befriending Victim B, the Mia Ash profile sent him a “photography survey” that contained the PupyRAT malware. This malware would have given the cyber hackers complete control of his computer and ultimately his network credentials. (Also: ‘photography survey’? Really?)
This isn’t the first time that the COBALT GYPSY group has used fake profiles to lure victims into opening malicious attachments. CTU researchers have observed campaigns by the same group during the past two years that have used extensive networks of fake social media profiles. A 2015 campaign used 25 fake LinkedIn profiles for employees of prominent companies in the Middle East and the world, many of them with 500 or more connections.
CTU researchers say they have “high confidence” that the group is associated with Iranian government-directed cyber operations. Specifically, this group has been observed launching espionage campaigns against organizations that are of strategic, political or economic importance to Iranian interests.
Wikoff said that there is also research by Palo Alto Networks and others that suggests the PupyRAT trojan used in the latest attacks may have played a role in seeding the Shamoon wiper malware in an earlier attack. That suggests that the Mia Ash activity may have been the early stages of a similar, destructive campaign and that similar social “honey pot” attacks may have played a role there, as well.

