In-brief: A new Special Publication from NIST offers a model for understanding networks of “things” and the security and reliability issues they might encounter.
There’s plenty of talking and writing about the burgeoning Internet of Things (or IoT). But when it comes to defining what, exactly, is “The Internet of Things,” its tempting to recall the famous saying by Supreme Court Justice Potter Stewart in regards to pornography that “I know it when I see it.”
Indeed, as NIST notes “there is not one universally accepted definition” of what the Internet of Things is, even though everyone agrees that it’s a Really Big Thing.
More important, from the standpoint of technology, Jeffrey Voas concludes in his recent NIST Special Publication “Network of Things,” to date “there is no formal, analytic or even descriptive set of building blocks that govern the operation, trustworthiness and lifecycle of IoT components.” (PDF)
Voas set out to fix that, creating a new model for understanding the Internet of Things that is based on existing models of distributed computing – the foundation of the Internet itself.
In distributed computing, computer components are networked and share messages about tasks to operate efficiently. On The Network of Things (NoT), things are based around four fundamental activities: sensing, computing, communication and actuation (basically: moving stuff). Further, the model identifies five building blocks, called “primitives,” that are core components of distributed systems. They are: a sensor, an aggregator, a communication channel, an external
utility (eUtility) and, finally, a decision trigger, Voas writes.

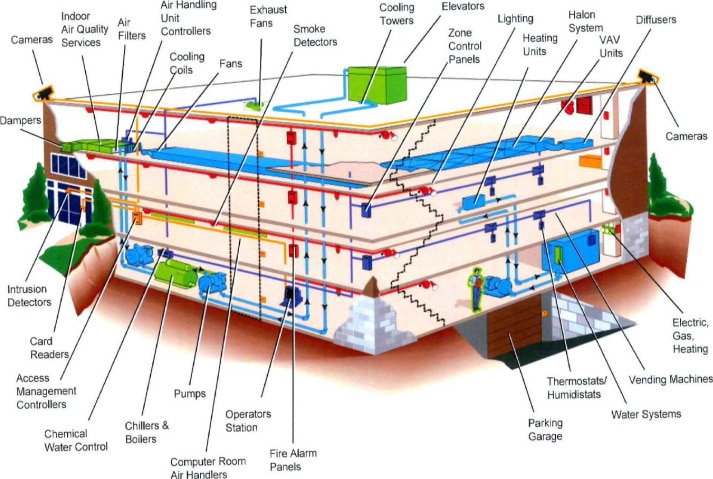
Voas’s paper uses a data-flow model to show how primitives, when composed in a certain manner, could impact a confidence in trustworthiness of NoTs – specifically: their security and reliability. He cites simple examples to underscore his thinking: an automobile speed sensor that starts providing inconsistent readings after years of exposure to heat, water, and dust. Alternatively, there is physical tampering – a malicious actor with physical access to a smart building’s temperature sensors could upload malicious firmware, enrolling them in a botnet and can contribute to distributed denial-of-service (DDoS) attacks. Other examples include a malicious actor introducing a “rogue sensor into a network that produces fake readings,” which are passed on to an aggregator without any validation of data, and the wearer of a smart health monitor having her movements tracked via the device.
NIST said that the Network of Things model was developed to assist researchers as they try to model simple problems, leveraging techniques and approaches that have been useful in securing larger non-IoT networks.
“The vocabulary and science of the Network of Things will help researchers understand how the components of IoT interoperate, and compare the security risks and reliability tradeoffs,” Voas said.
Source: NIST’s Network-of-Things Model Builds Foundation to Help Define the Internet of Things

