In-brief: Cisco Systems new CEO Chuck Robbins talked up the disruptive potential of IoT, while also announcing new Cisco products geared at key verticals and a new security portfolio for IoT.
Cisco Systems announced a new Internet of Things security solution for industry yesterday that it says will “mitigate the risk of system disruption” in IoT deployments.
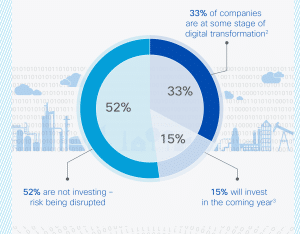
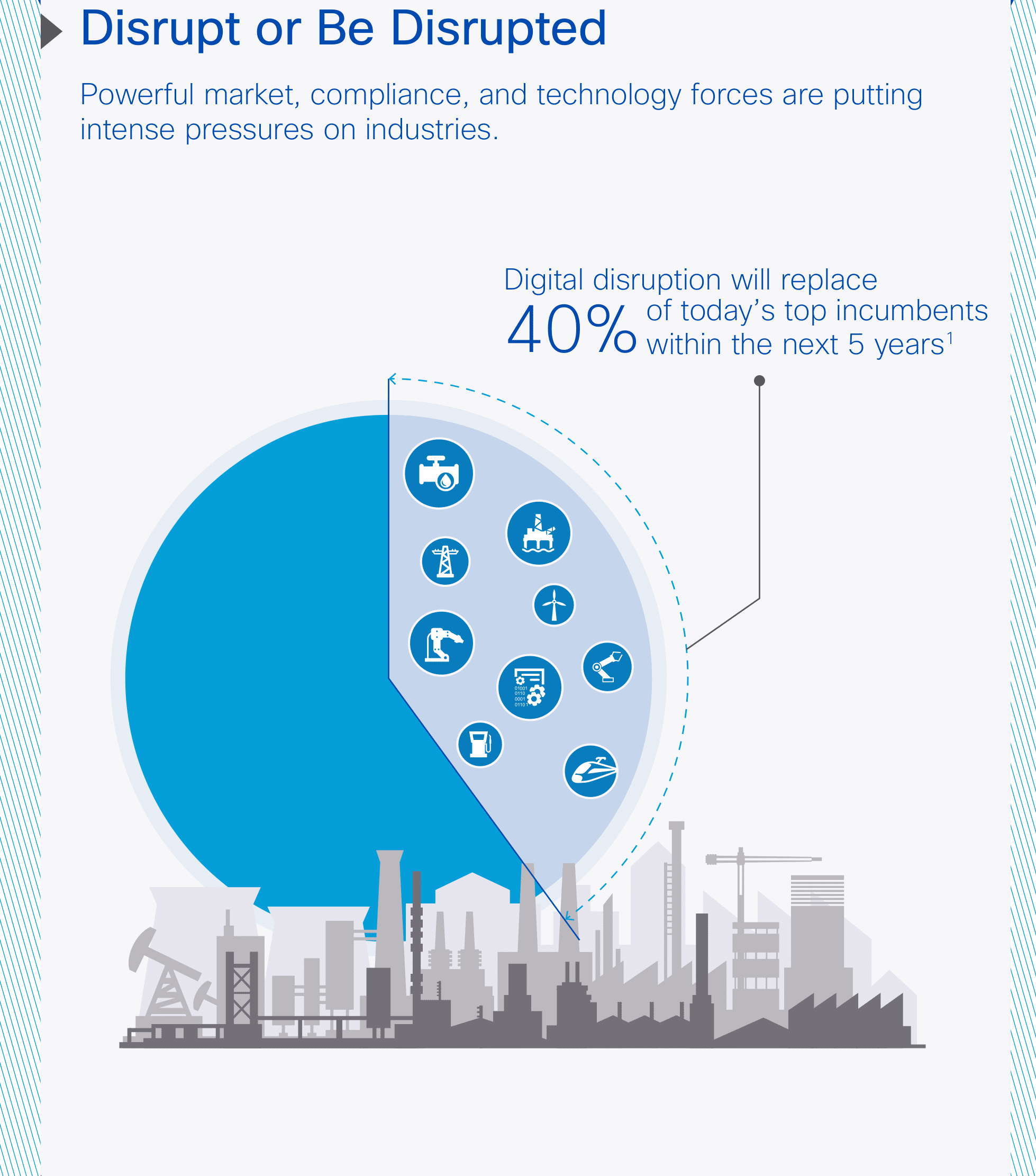
The announcement (read the company’s statement here) was part of a larger company announcement of vertical-specific solutions for manufacturing, oil and gas, utilities and transportation, with Cisco presenting the IoT System Security product as a way to enforce security policies and detect anomalous behavior on IoT deployments.
Cisco is combining a new appliance, the ISA-3000, for “application visibility, policy enforcement and threat defense” and what it calls a “Fog Data Services” security offering. “The IoT network can now act as a sensor and enforcer to provide security policy enforcement within router and switches.”
Cisco sees the product deployed across IoT verticals and with already common applications like video surveillance, physical access control and so on. The company will be partnering with firms like Rockwell Automation to continue developing features for it.
As for how Cisco plans to address the myriad of problems inherent in IoT deployments, the Register has an interesting piece that provides more color on the announcement, including comment from Cisco’s new CEO Chuck Robbins. According to him, traffic analysis and anomaly detection features built into Cisco’s gear will play a big role in Cisco’s IoT security push.
Cisco plans to use its appliance and cloud based threat intelligence services to spot patterns of anomalous activity in real time and to isolate that activity.
‘”Allow the network to take advantage of machine-learning to build intelligence from its traffic, and act on threats if suspicious traffic is detected. There is no longer a central castle. We can’t put a moat around it. We have to do security differently,” Robbins said.
Of course, traffic analysis is just one technique for spotting threats – and maybe not even the best approach. For one thing: by the time there’s anomalous activity to spot, attackers have already gained a foothold on your network – one that may be difficult to reclaim.
You can read more over at The Register: If the Internet of Things scares you now: Cisco’s CEO is bent on hooking up robots, EVERYTHING • The Register