In-brief: Researchers from the firm Cylance warned that an unpatched security flaw first discovered in 1997 could be used to attack a wide range of popular applications and steal user credentials.
Carnegie Mellon’s CERT (Computer Emergency Response Team) has issued a warning about an exploitable vulnerability in all supported versions of Windows, as well as software by dozens of other vendors that could be used to steal user credentials and compromise vulnerable systems.
The Vulnerability Note (#VU672268) follows a report by the security firm Cylance (PDF), which warns that software from at least 31 companies including Adobe, Apple, Box, Microsoft, Oracle and Symantec can be exploited using this vulnerability, which Cylance has branded “Redirect to SMB.”
The root of the problem identified by Cylance actually dates back to a problem that was first discovered in 1997 by a researcher named Aaron Spangler. Spangler identified an insecure behavior in the way that Windows 95 and Windows NT handled requests for so-called “file URLs,” or URLs that began with the word “file” (for example: file://1.1.1.1/). Sending such a request to Internet Explorer would cause those operating system to attempt to authenticate with a Service Message Block (SMB) server at the IP address 1.1.1.1. That would allow an attacker to harvest the credentials of the vulnerable user. File URLs could be buried in an image, an iframe, or any other web resource resolved by the browser.
The Server Message Block (SMB) protocol is a network file sharing protocol that is used to allow an application on a network to access (that is: read and write to) files or other resources from a remote server.
That issue was never patched by Microsoft. And Cylance researcher Brian Wallace was researching its use as part of research on ways to abuse a chat client that provided an image preview feature. Lo and behold: when an image containing a file URL pointing to a malicious SMB server was sent to the client, it tried to load the image and the Windows user who was the target of the attack attempted to authenticate with our SMB server, Wallace wrote in a blog post Monday.
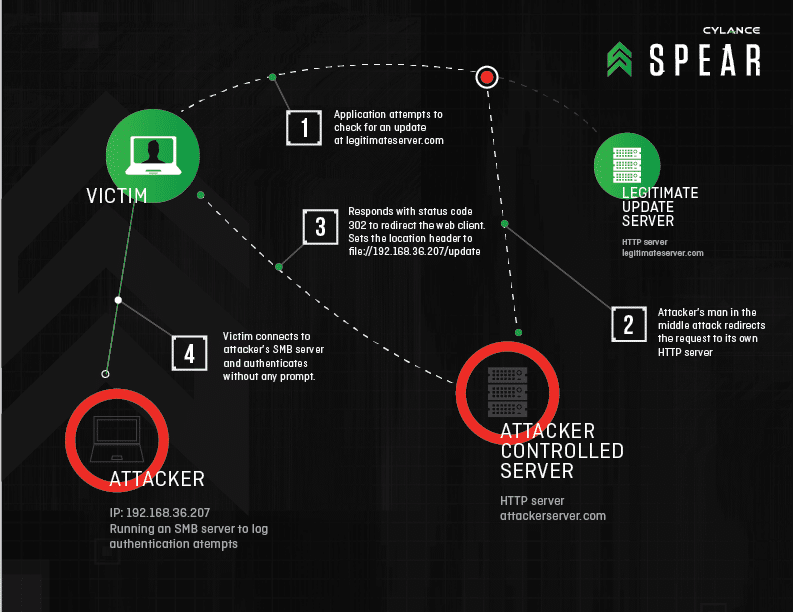
Cylance identified commonly used Windows APIs (Application Program Interfaces) that support redirection from HTTP or HTTPS to SMB. A large population of Windows applications make use of those vulnerable APIs – many of them used for application updates and reporting, Wallace wrote.
“This discovery opened up a wide range of new attack methods. When combined with a man-in-the-middle attack, an attacker can force authentication attempts with an SMB server using susceptible applications and services that transmit data over HTTP or HTTPS,” Wallace said.
Some of the most commonly used applications on the Internet are affected, including: Adobe Reader, Apple QuickTime and Apple Software Update, Internet Explorer, Windows Media Player, Excel 2010, and even in Microsoft Baseline Security Analyzer
Security programs including Symantec’s Norton Security Scan, AVG Free, BitDefender Free, and Comodo Antivirus are also vulnerable to the Redirect to SMB attack.
Cylance warns that the Redirect to SMB vulnerability could be used in a variety of ways. Malicious ads could be used to try to force authentication attempts from Internet Explorer users. A sophisticated actor could use it given they already had control over some component of a victim’s network traffic.
Malicious ads could also be crafted that would force authentication attempts from IE users while hiding malicious behavior from those displaying the advertising. Less sophisticated attackers could launch Redirect to SMB attacks on shared WiFi access points at locations such as coffee shops from any computer, including mobile devices, Wallace wrote.
Cylance first reported the issue in February and has been working with vendors to address it since then. However, Microsoft has not yet issued a patch for the flaw. The company recommends blocking outbound traffic from TCP 139 and TCP 445 using either a desktop or gateway firewall – though doing so would almost certainly interfere with the operation of other applications.

I run several LAN-only networks for my own business, and those of clients. My question is this: If I can block ports 139 and 445 (both inbound and outbound) at the Gateway router, would that prevent this hack from working, but still allow SMB/NETBIOS and other Windows-related services to work within the LAN? I understand this would prohibit remote access to Shares, Printers, etc…but that would be intentional.