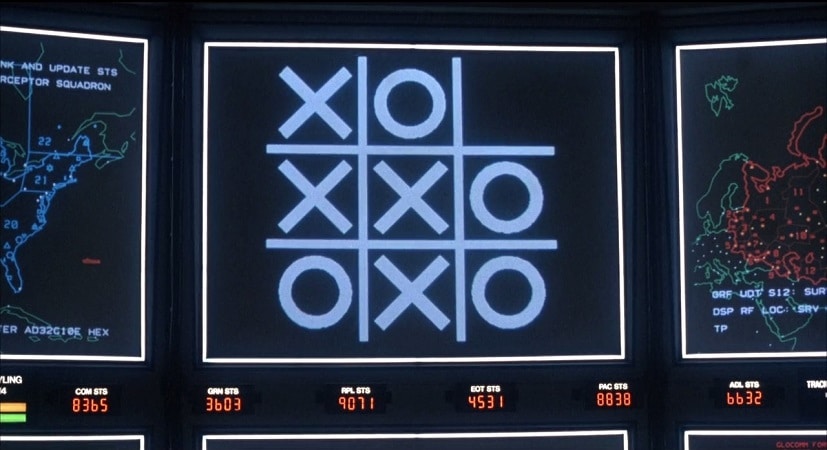
In this week’s podcast (episode #111), sponsored by CyberSN: what happens when the Internet gets physical? Noted author and IBM security guru Bruce Schneier joins us to talk about his new book on Internet of Things risk: Click Here to Kill Everybody. Also: everyone knows that cyber security talent is hard to come by, and even harder to keep. But why does precious cyber talent walk? In our second segment, we’re joined by Deidre Diamond of cyber security placement firm CyberSN, who has all the answers.
Tag: privacy
Video: How Automation and Machine Learning Power Future of SIEM
In this interview with The Security Ledger, Amy Blackshaw of RSA talks about how the company’s RSA Netwitness SIEM product is evolving to keep pace with a fast -evolving security market. Job 1: use machine learning and automation to allow customers to make the best use of their human resources.
Three Decades On: RSA Labs Sets Course for Future
RSA Chief Technology Officer and head of RSA Labs Dr. Zulfikar Ramzan says his company, which pioneered commercial applications of public key cryptography, is setting its sites on the future as it looks to embrace the disruptive security solutions of the future.
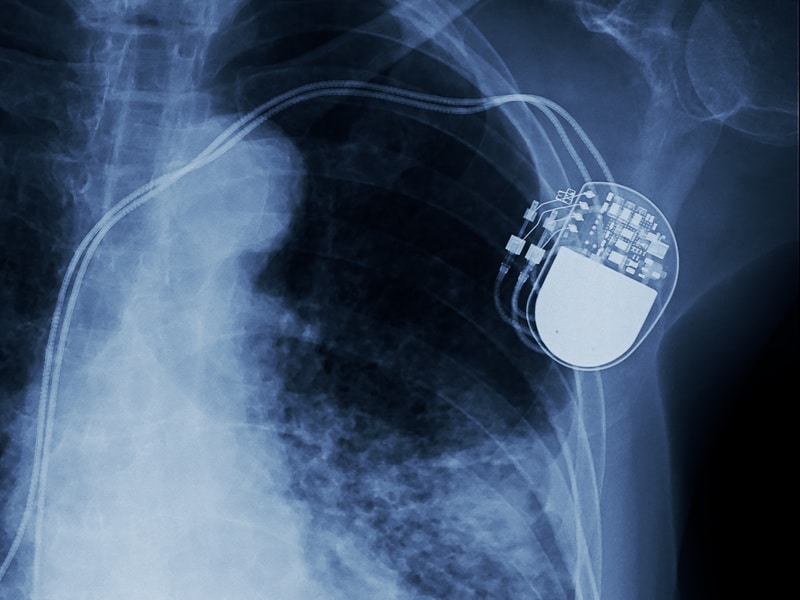
Spotlight Podcast: Synopsys’ Dan Lyon on the Challenge of Securing Connected Medical Devices
In this Spotlight Podcast, sponsored by Synopsys: In the wake of a presentation at Black Hat about security flaws in implantable pace maker devices, Synopsys Principal Consultant Dan Lyon joins us to talk about why medical device makers struggle to make their connected medical devices more secure. Dan and I discuss some of the flaws in the approach that medical device makers take to security, and how manufacturers can take a page out of their own book: applying the same standards to cyber security as they do to – say- device safety.
Breaking the Ice on DICE: scaling secure Internet of Things Identities
In this Spotlight Podcast, sponsored by Trusted Computing Group*, Dennis Mattoon of Microsoft Research gives us the low-down on DICE: the Device Identifier Composition Engine Architectures, which provides a means of solving a range of security and identity problems on low cost, low power IoT endpoints. Among them: establishing strong device identity, doing device attestation and safe deployment at scale and verifying software updates.