MikroTik is part of a bigger problem: the failure of infrastructure owners to take appropriate action to address serious security holes in products.
Tag: hacks
Report: Financial industry in crosshairs of credential-stuffing botnets
Botnets mounting credential-stuffing attacks against the financial industry are on the rise, with a more than 20-percent uptick in a two-month period, a new report from Akamai has found.
Special Black Hat Coverage: Google’s Parisa Tabriz Says Don’t Be A Jerk
In this special Black Hat edition of the Podcast, sponsored by UL: Parisa Tabriz, Google’s Director of Engineering for the Chrome Web browser, brought some strong medicine to Las Vegas for her Black Hat keynote speech. We talk about why her simple message was so groundbreaking. Also: Ken Modeste of UL joins us from the Black Hat briefings to talk about UL’s efforts to make cyber security as important to consumers in the 21st century as product safety was in the 20th.
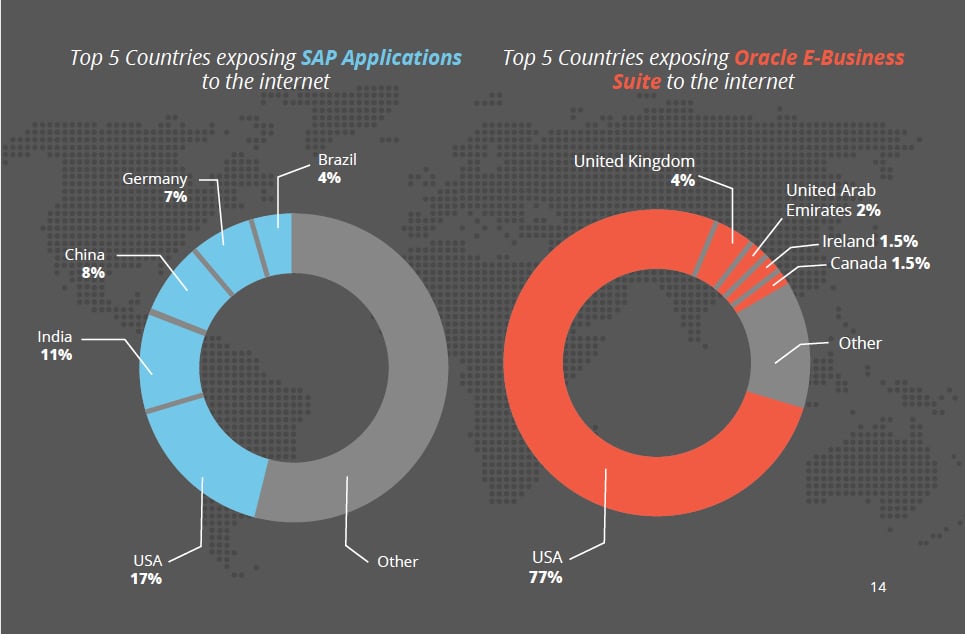
Report: Cybercriminals target difficult-to-secure ERP systems with new attacks
Cybercriminals are targeting enterprise resource planning (ERP) apps–some of the oldest and most difficult-to-secure business software systems–with new attacks in an effort to exploit vulnerabilities and gain access to valuable, sensitive enterprise data, according to a new report.
Expert says: Hack your Smart Home to Secure It
Smart home security starts at home, according to researcher Michael Sverdlin who says that consumers should explore the security of their smart home technology and consider simple modifications or hacks to remove insecure or promiscuous features.