In-brief: Cisco Vice President Scott Harrell says that small and mid-sized organizations are in the crosshairs of sophisticated cyber criminals. Unfortunately, such firms often lack the tools and skills to identify and contain such threats.
Spam
With Multi-Vector Attacks, Quality Threat Intelligence Matters
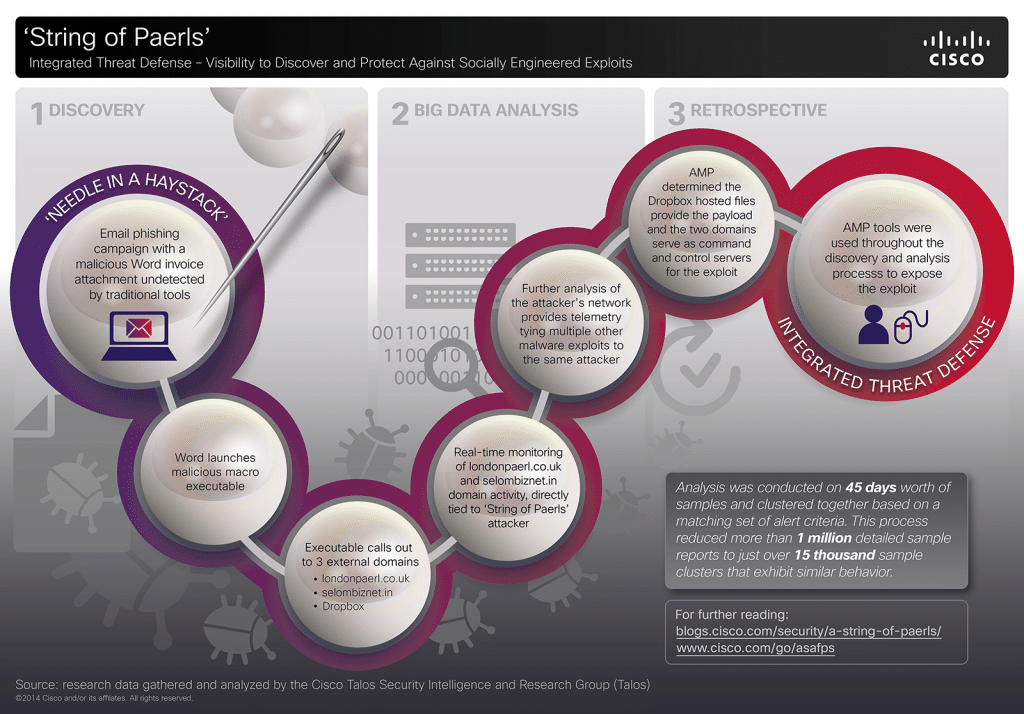
In the last year, the world’s attention has been riveted by a series of high-profile hacks of major corporations in retail, finance and the entertainment industry, among others. Each of these incidents is unique, involving different threat actors and motives. However, each of these attacks is also a sterling example of what we, at Cisco, term “multi-vector attack” that employs a range of technologies, deployed in numerous stages, to penetrate the defenses of the target organization. Here at Cisco, we have studied these attacks in-depth and have identified some commonalities among these multi-vector attack, and useful approaches to combat them. This blog post will discuss some of our findings. About Multi-Vector Attacks Any cyber attack, large or small is born from a weak link in the security chain. These weak links take many forms: poorly configured Web servers, gullible employees or vulnerable-but-common applications like Microsoft Office, Adobe Reader and Java are common examples. Multi-vector attacks […]
Europol Warns of Internet of Things Risk
In a newly released report, Europol’s European Cybercrime Center (EC3) warns that the growth of the Internet of Things (IoT) threatens to strengthen the hand of organized cyber criminal groups and make life much more difficult for police and governments that wish to pursue them. EC3’s latest Internet Organized Crime Threat Assessment (iOCTA) says the “Internet of Everything” will greatly complicate the work of law enforcement creating “new opportunities for everything from cyber criminals to state actors to child abusers. The growing numbers of connected devices will greatly expand the “attack surface” available for cyber criminal activity, the EC3 warns. Cyber criminals may co-opt connected devices for use in common criminal activity (like denial of service attacks and spam campaigns). However, advancements like connected (“smart”) vehicles and infrastructure create openings for large scale and disruptive attacks. The report, which was published late last months, is a high level position paper and pulls data mostly […]
Report: CIA Fears the Internet of Things | Nextgov.com
A story by Patrick Tucker over at Nextgov.com picks up on some comments from Dawn Meyerriecks, the deputy director of the Central Intelligence Agency’s directorate of science and technology regarding the agency’s thinking about the Internet of Things. Meyerriecks was speaking at The Aspen Institute’s Security Forum on Thursday of last week in a panel on “The Future of Warfare.” Speaking about the topic of cyber warfare, she said that current debates about the shape of cyber war don’t address the “looming geo-security threats posed by the Internet of Things.” Meyerriecks cited the now-debunked Proofpoint report about smart refrigerators being used in spam and distributed denial of service attacks.” She also mentioned “smart fluorescent LEDs [that are] are communicating that they need to be replaced but are also being hijacked for other things.” Those might be some sensational (and dubious) examples, but Meyerriecks main point was more pedestrian: that we’re on the cusp of disruptive […]
TRUST: Threat Reduction via Understanding Subjective Treatment
It has become obvious (to me, anyway) that spam, phishing, and malicious software are not going away. Rather, their evolution (e.g. phishing-to-spear phishing) has made it easier to penetrate business networks and increase the precision of such attacks. Yet we still apply the same basic technology such as bayesian spam filters and blacklists to keep the human at the keyboard from unintentionally letting these miscreants onto our networks. Ten years ago, as spam and phishing were exploding, the information security industry offered multiple solutions to this hard problem. A decade later, the solutions remain: SPF (Sender Policy Framework), DKIM (Domain Keys Identified Mail) and DMARC (Domain-based Message Authentication, Reporting & Conformance). Still: we find ourselves still behind the threat, rather than ahead of it. Do we have the right perspective on this? I wonder. The question commonly today is: “How do we identify the lie?” But as machine learning and data science become the new norm, I’m […]