In-brief: The discovery of a malicious link buried in software for a common IP camera sold on Amazon and other online retail outlets is just the latest example of supply chain based threats to connected products.
iframe attack
IBM: Dyre Banking Malware Behind Sophisticated Crime Spree
In-brief: IBM researchers say they have seen a spike in malicious activity linked to the Dyre family of malware. Sophisticated attacks on business banking accounts have led to the theft of millions of dollars, IBM says.
Discrete Malware Lures Execs At High-End Hotels
Kaspersky Lab has a fascinating write-up of malware it is calling “DarkHotel.” The information-stealing software is believed to target traveling executives. Curiously, Kaspersky says the malware may be almost a decade old and is found only on the wireless networks and business centers of select, high-end hotels. Reports about targeted attacks on traveling executives are nothing new. However, the Kaspersky report (PDF version here) may be the most detailed yet on a specific malicious software family that is devoted to hacking senior corporate executives. According to Kaspersky, the DarkHotel malicious software maintained a presence on hotel networks for years, with evidence of its operation going back as far as 2007. The malware used that persistent access to target select hotel guests, leveraging check-in/check-out and identity information on guests to limit attacks to high value targets. Targeted guests were presented with iFrame based attacks that were launched from the hotel’s website, […]
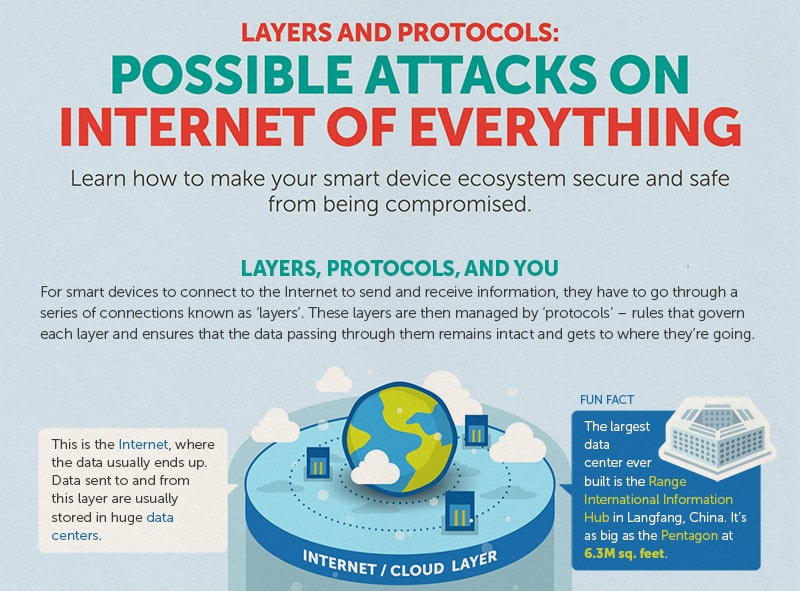
Infographic: Possible Attacks on The Internet of Things
The folks over at Trend Micro have put together a nice infographic that reminds us that all those smart devices connected to the Internet communicate through some well worn channels, namely: standard communications protocols like Wi-Fi, Ethernet and Bluetooth that connect devices to each other and the global Internet, as well as HTTP that are used to transmit data to and from cloud based resources like management interfaces. Of course those standard protocols also leave IoT devices vulnerable to a wide range of commodity attacks: from brute force password cracking on web based management consoles to Man in the Middle attacks that can sniff out authentication credentials and hijack sessions. Trend’s infographic does a good job of depicting the various layers in the IoT stack and some of the likely attack vectors for each layer. It also gives advice on how to protect yourself (use encryption, patch software vulnerabilities, disable unused ports). Nothing ground breaking […]
Compromised Website Used In Attack On SoHo Routers
The folks over at the web security shop Sucuri have an interesting post today that warns of a web-based attack launched from the site of a popular Brazilian newspaper that is targeting home broadband routers. According to Sucuri, researchers investigating a breach at the web site politica . estadao . com . br uncovered evidence that the hackers were using iframe attacks to try to change the DNS configuration on the victim’s DSL router, first by trying a brute force attack on the router’s default credentials. According to Sucuri, the payload was trying to crack default accounts like admin, root, gvt and other common usernames and a variety of known-default router passwords. Small office and home office (or SoHo) broadband routers are an increasingly common target for cyber criminals because many (most?) are loosely managed and often deployed with default administrator credentials. [Read Security Ledger coverage of home router hacks here.] In March, the firm Team Cymru published a report describing a widespread compromise of […]