October has arrived. And while that means colorful foliage and Halloween for many of us, it is also a special time in the information security industry: cyber security awareness month – or NCSAM. Security Ledger will be supporting NCSAM this month with banner ads and other content that highlight NCSAM events. Cyber Security Awareness Month – in its 11th year- is a public-private effort to raise public awareness about online security and safety. It’s best known for the “Stop. Think. Connect.” meme, but also is an occasion for elected officials and private sector firms to highlight cyber security issues. In a Presidential Proclamation released on Tuesday, President Obama called cyber threats “one of the gravest national security dangers the United States faces.” “They jeopardize our country’s critical infrastructure, endanger our individual liberties, and threaten every American’s way of life. When our Nation’s intellectual property is stolen, it harms our economy, […]
brute force attack
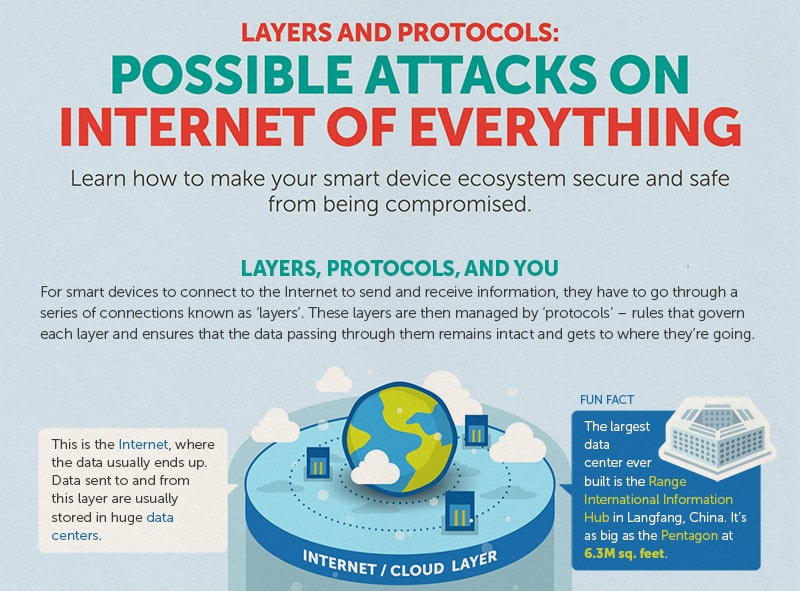
Infographic: Possible Attacks on The Internet of Things
The folks over at Trend Micro have put together a nice infographic that reminds us that all those smart devices connected to the Internet communicate through some well worn channels, namely: standard communications protocols like Wi-Fi, Ethernet and Bluetooth that connect devices to each other and the global Internet, as well as HTTP that are used to transmit data to and from cloud based resources like management interfaces. Of course those standard protocols also leave IoT devices vulnerable to a wide range of commodity attacks: from brute force password cracking on web based management consoles to Man in the Middle attacks that can sniff out authentication credentials and hijack sessions. Trend’s infographic does a good job of depicting the various layers in the IoT stack and some of the likely attack vectors for each layer. It also gives advice on how to protect yourself (use encryption, patch software vulnerabilities, disable unused ports). Nothing ground breaking […]
What Hollywood Can Teach Us: Passwords Matter More Than Ever
Andrey Belenko had what you might call a ‘brush with infamy’ earlier this week after a presentation he took part in on the security of Apple’s iCloud became a set piece in the news media scramble to identify the source of a huge trove of leaked celebrity photos – many depicting Hollywood A-List stars in various states of undress. “It’s not the kind of attention you want to receive,” said Belenko, a security researcher with the firm ViaForensics. “It’s all really creepy stuff.” Belenko’s link to the celebrity hacking scandal was a matter of happenstance. He was scheduled to give a presentation at a small, St. Petersburg multi-media conference, Chaos Constructions, over the weekend. Belenko was presenting research he had conducted a year earlier on the security of Apple’s KeyChain technology and iCloud – a talk he had given twice before in the last year. Prior to his talk, Belenko […]
Hack Tool Authors Deny Link To Celeb Photo Leaks
With some of Hollywood’s biggest stars issuing statements on Monday condemning the leak of personal photographs online, attention has turned to identifying the source of the leaks. But more than 24 hours after the photos appeared, there are more questions than answers about its source. Early attention has focused on an automated tool that exploited an apparent vulnerability in Apple’s FindMyiPhone feature. But by Monday, there were denials from the makers of that tool that it played any role in the massive privacy breach that saw photos of A-list celebrities like Jennifer Lawrence, Kate Upton and others leaked online. Within hours of the photos’ appearance on the image sharing site 4chan, attention shifted to the cause of the leak and the coincidence of the leaked photos with the publication of iBrute, a simple tool available on GitHub in recent days. According to this published report by Owen Williams over at TheNextWeb, the […]
PasswordsCon Preview: Passwords Are Dead. Long Live Passwords.
I had an opportunity to sit with Per Thorsheim, co-founder of PasswordsCon about next week’s Passwords14 Conference in Las Vegas, Nevada. If you haven’t checked it out before, PasswordsCon is the world’s premiere technical conference that is just focused on the security of passwords and pin codes. PasswordsCon is a one-of-a-kind event: bringing together folks whose specialty is cracking and defeating password security with security experts whose interest is in shoring up protections for sensitive data. This year’s conference, which is sharing space with the B-Sides Las Vegas Conference on August 5 and 6. PasswordsCon has earned a reputation for being the launching pad for some eye-popping new tools for password cracking. Back in 2012, we reported on a 25 GPU device that radically lowered the bar to cracking even the strongest passwords protected with weaker encryption algorithms, like Microsoft’s LM and NTLM, obsolete. Among other things, the Conference will feature […]