Recently, the Akamai Threat Research Team unveiled a unique distributed brute force attack campaign targeting nearly five hundred WordPress applications. What’s interesting about this campaign? It clearly demonstrates how Web attackers are becoming more sophisticated, attempting to evade security controls – specifically Web Application Firewalls (WAFs) and rate control protections. A Short Primer to Brute-Force Attacks Brute force Web attackers attempt to gain privileged access to a Web application by sending a very large set of login attempts, within a short period of time. Using volumetric single source of attack is easily mitigated by blacklisting. Today’s brute force attacks are typically characterized by volumetric attacks coming from distributed IPs. In this way, if the attacker’s source IP is detected, they can still continue with the attack campaign by switching a source IP. As part of this cat-and-mouse evolution, WAFs are enhanced with several rate control measures that detect and block […]
brute force attack
Wireless Infusion Pump is Test Case for Securing Medical Devices
A National Institute of Standards and Technology (NIST) reference document is providing some of the clearest guidance from the U.S. government for securing connected medical devices, but may be setting too low a bar for securing wireless communications, according to a security expert. NIST, working with the University of Minnesota’s Technological Leadership Institute, released a draft Use Case document (PDF) on December 18 to help health care providers “secure their medical devices on an enterprise networks.” However, in the area of communications security, the document suggests the use of WEP (Wired Equivalent Privacy), a legacy wireless security technology that can easily be cracked. NIST released the draft security use case document and is seeking feedback from the public. The drug infusion pump case study is described as the “first of a series” of similar use cases that will focus on medical device security, NIST wrote. The draft document presents a technical description of the security challenges […]
BitDefender Finds Phone to Smart Watch Communications easy to Snoop
Researchers from the security firm BitDefender have found that it is possible to snoop on wireless communications sent between smart watches and Android devices to which they are paired. The researchers, led by Liviu Arsene, captured and analyzed raw traffic between the Nexus 4 Android device running Android L Developer Preview and the Samsung Gear Live smart watch. The traffic was captured on the Android device before it was transmitted to the associated smart watch using a baseband co-processor that it standard on most Android devices. According to BitDefender, the wireless traffic is secured using a six digit PIN code. That leaves the device vulnerable to computer-enabled “brute force” attacks that can try the million possible six digit codes in short order. BitDefender noted that the problem exposed wasn’t limited to smart watches. Using baseband co-processors on Android devices to handle encryption is “not a fool-proof security mechanism,” Arsene wrote. Attackers might also be […]
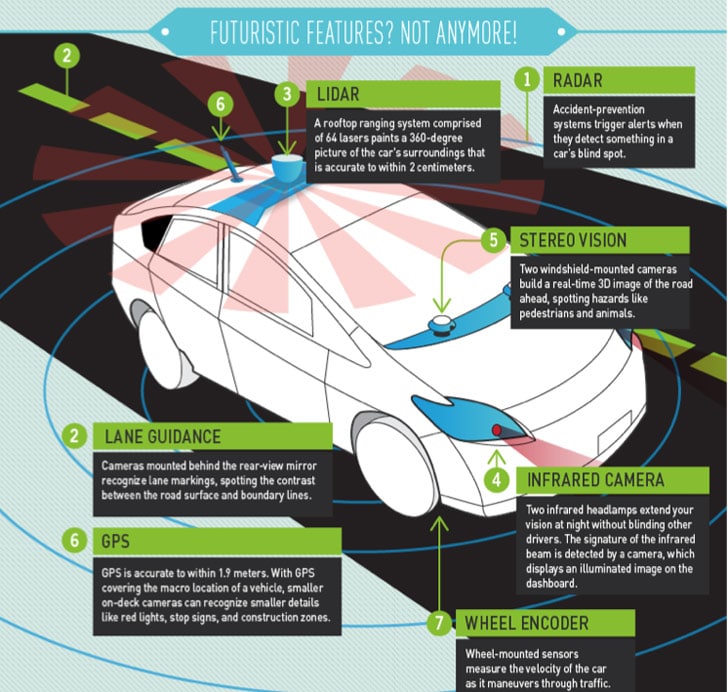
Security Ledger Talks Car Hacking on NPR’s AirTalk
Just a note to our readers that you can listen to a great conversation on hacking automobiles on Airtalk, a National Public Radio call-in talk show that airs on WPCC, Pasadena, California. Interestingly: the other expert guest on the show was none other than Chris Valasek of IOActive, one of the most recognized researchers on security vulnerabilities in modern automobiles. [Read more Security Ledger coverage of Chris Valasek’s research here.] Chris and I spoke with host Larry Mantle about the current state of affairs with regard to car hacking: what is possible (theoretically), what is practical and what are car makers doing about it. Check out our conversation via KPCC’s web site: The next frontier for computer hackers: Your car | AirTalk | 89.3 KPCC.
Supply Chain Risk: Raspberry Pi Device Used for War Shipping
An interesting post on supply chain security over at Security Affairs. The post looks at a new approach to supply chain surveillance (and, presumably, attacks): ‘war shipping.’ War shipping is, of course, a play on the ‘war driving’ scene from the early days of consumer wifi, in which cars outfitted with antennae would canvas whole cities, documenting open wi-fi hotspots that could be used to grab some free Internet. In this case, Security Affairs notes a shippable board-sized package designed by security expert Larry Pesce of Paul’s Security Weekly (fka Pauldotcom). The device can be contained in a standard UPS shipping box and delivered to a target network to passively surveil or even attack it. The kit is built on a Raspberry Pi b_ with an AWUS051NH wireless card, a cheap battery charger, kismet and custom software. Pesce demonstrated the device at Derbycon, a Louisville, Kentucky based event last month. The device includes both […]