Dragos Security on Wednesday unveiled a “Community Defense Program” to provide free cybersecurity software for small utilities providing water, electric, and natural gas in the United States.
SCADA – ICS
FBI: Iranian APT Targets Israeli-Made PLCs Used In Critical Industries
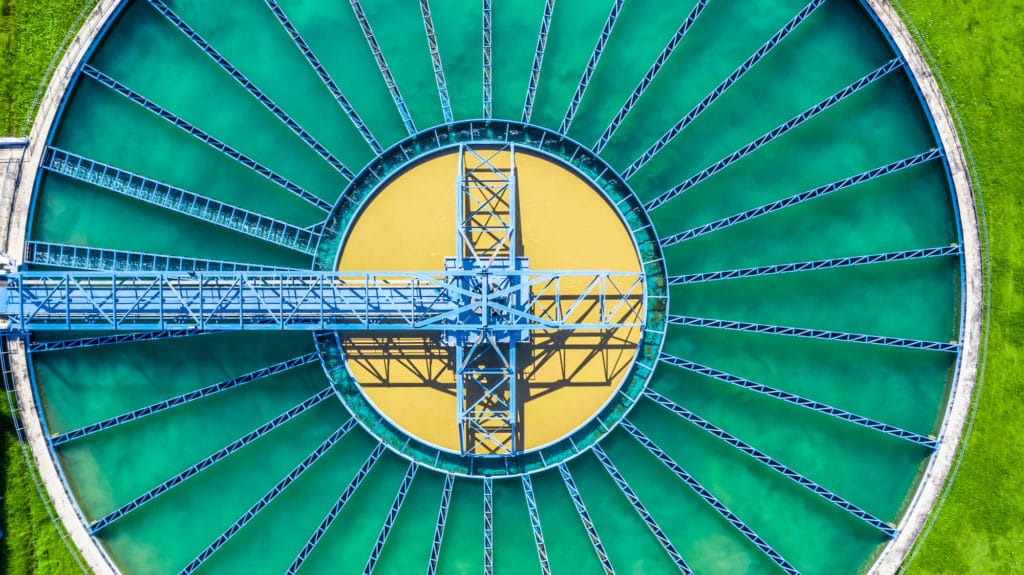
The hack of a Pennsylvania water treatment facility in November is part of a larger campaign by an Iranian APT group against users of Israel-made operational technology.
Cyberattacks on Industrial Control Systems Jumped in 2022
Cyberattacks on industrial control systems (ICS) jumped in 2022, with an 87% jump in ransomware attacks and a 35% increase in the number of ransomware groups targeting industrial control and operational technology (OT) systems, according to a report by Dragos Security.
Episode 203: Don’t Hack The Water and Black Girls Hack Founder Tennisha Martin
In this episode of the Security Ledger Podcast (#203) we talk about the apparent hack of a water treatment plant in Oldsmar Florida with Frank Downs of the firm BlueVoyant. In our second segment: is infosec’s lack of diversity a bug or a feature? Tennisha Martin of Black Girls Hack joins us to talk about the many obstacles that black women face as they try to enter the information security field.
Sensor-y Overload: Cyber Risk and the Merrimack Valley Gas Explosions
Let’s be clear: the natural gas explosions that rocked the Merrimack Valley north of Boston in September weren’t the result of a cyber attack. Unfortunately: well known vulnerabilities affecting the security of remote sensors and industrial control system software mean they easily could have been.