A newly discovered campaign pushing malicious open source software packages is designed to steal mnemonic phrases used to recover lost or destroyed crypto wallets, according to a report by ReversingLabs.
open source
The surveys speak: supply chain threats are freaking people out
A bunch of recent surveys of IT and security pros send a clear message: threats and risks from vulnerable software supply chains are real, and they’re starting to freak people out.
Supply Chain Hackers LofyGang Behind Hundreds of Malicious Packages
Researchers at Checkmarx say that a cybercriminal group, LofyGang, has targeted the open-source supply chain with hundreds of malicious packages to steal credit card information, stream accounts, and promote hacking tools.
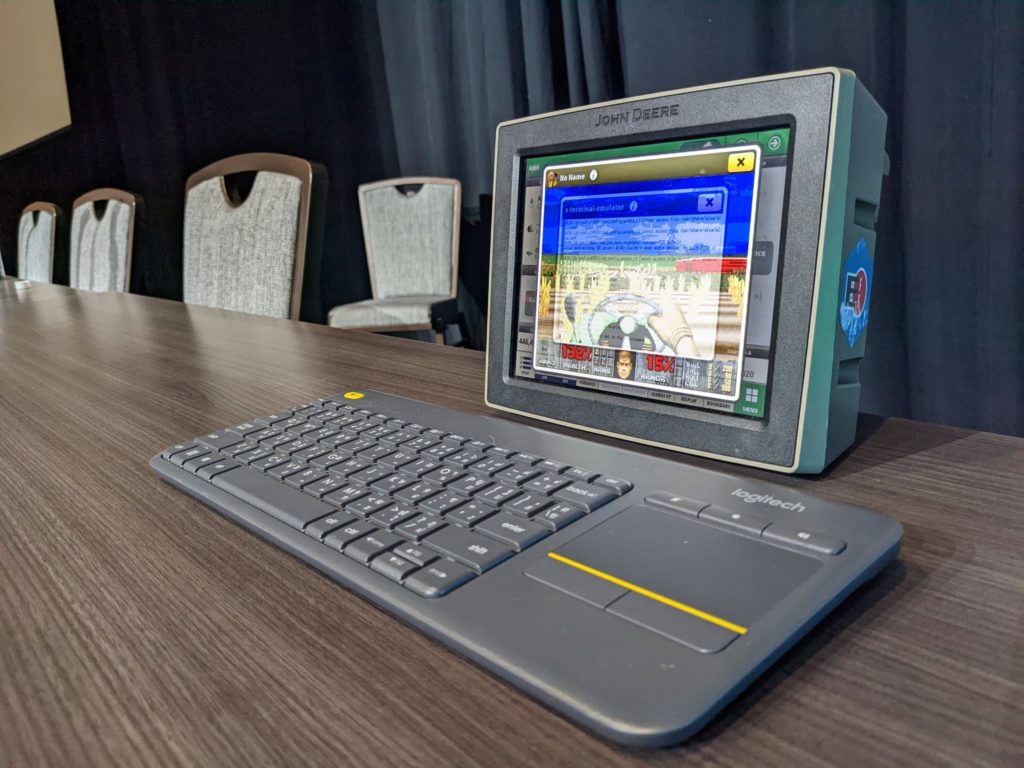
UPDATE DEF CON DOOM Patrol: Deere Jailbreak Raises Questions on Security, Competition
A researcher presented the results of a year-long effort to reverse engineer John Deere hardware to run a version of the DOOM first person shooter. He also discovered a number of security flaws along the way.
Spotlight: How Secrets Sprawl Undermines Software Supply Chain Security
Mackenzie Jackson, the Developer Advocate at GitGuardian joins Paul to discuss how “secrets sprawl” on sites like GitHub threatens software supply chains.