In-brief: will the development of the Internet of Things stall because of a lack of investment in supporting wireless infrastructure? A panel at a recent conference warned that it is possible.
API
Opinion: Gaping Holes in Security of APIs
In-brief: In this, the first in a three-part series on REST API, Neeraj Khandelwal of Barracuda Networks discusses the growing importance of application program interfaces to business success, and how API insecurity poses a significant and under-appreciated risk to businesses.
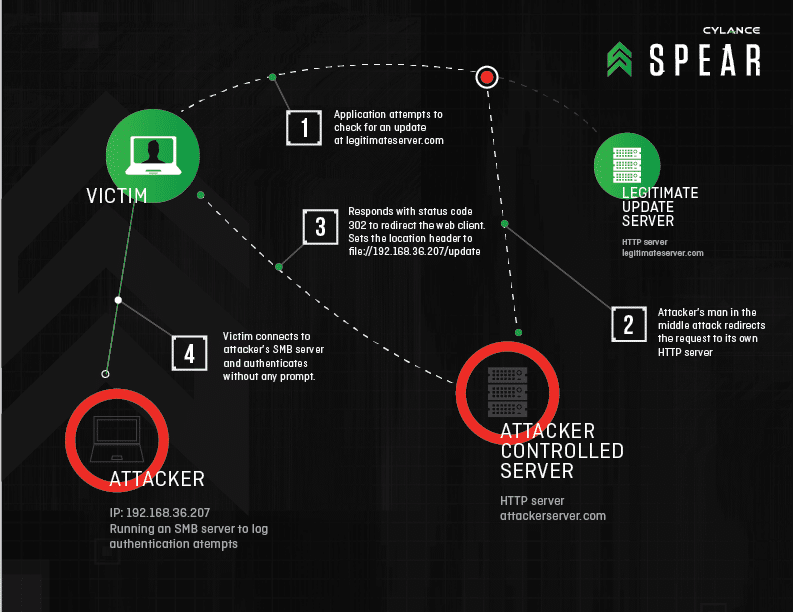
Windows Bug From 1997 Enables Credential Theft
In-brief: Researchers from the firm Cylance warned that an unpatched security flaw first discovered in 1997 could be used to attack a wide range of popular applications and steal user credentials.
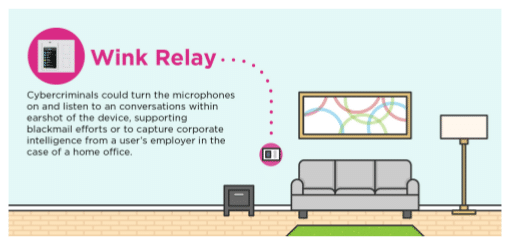
Research: IoT Hubs Expose Connected Homes to Hackers
In-brief: A study of common connected home gateways finds lax security that could expose consumers to snooping or even malicious attacks, according to the application security firm Veracode.
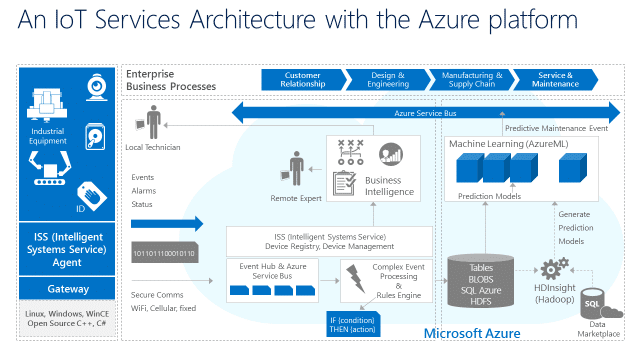
Microsoft Goes Big, Announcing Azure IoT Suite
In-brief: Microsoft Corp. made a major play for the Internet of Things platform space, announcing Azure IoT Suite – a cloud based platform for accelerating and managing Internet of Things products.