In this episode of the podcast (#235) Justine Bone, the CEO of Medsec, joins Paul to talk about cyber threats to healthcare organizations in the age of COVID. Justine’s firm works with hospitals and healthcare organizations to understand their cyber risk and defend against attacks, including ransomware.
Internet of Things
Spotlight: Your IoT Risk Is Bigger Than You Think. (And What To Do About It.)
In this Spotlight edition of the podcast, we’re joined by Curtis Simpson, the Chief Information Security Officer at Armis. Curtis and I discuss the growing cyber risks posed by Internet of Things devices within enterprise networks. IoT and OT (operation technology) deployments are growing and pose challenges to organizations that are still focused on conventional IT systems and threats, and that struggle to detect such devices in their environments.
Spotlight: Automation Beckons as DevOps, IoT Drive PKI Explosion
Brian Trzupek of DigiCert joins Paul to talk about the findings of a recent State of PKI Automation survey and the challenges of managing fast-growing population of tens of thousands of PKI certificates.
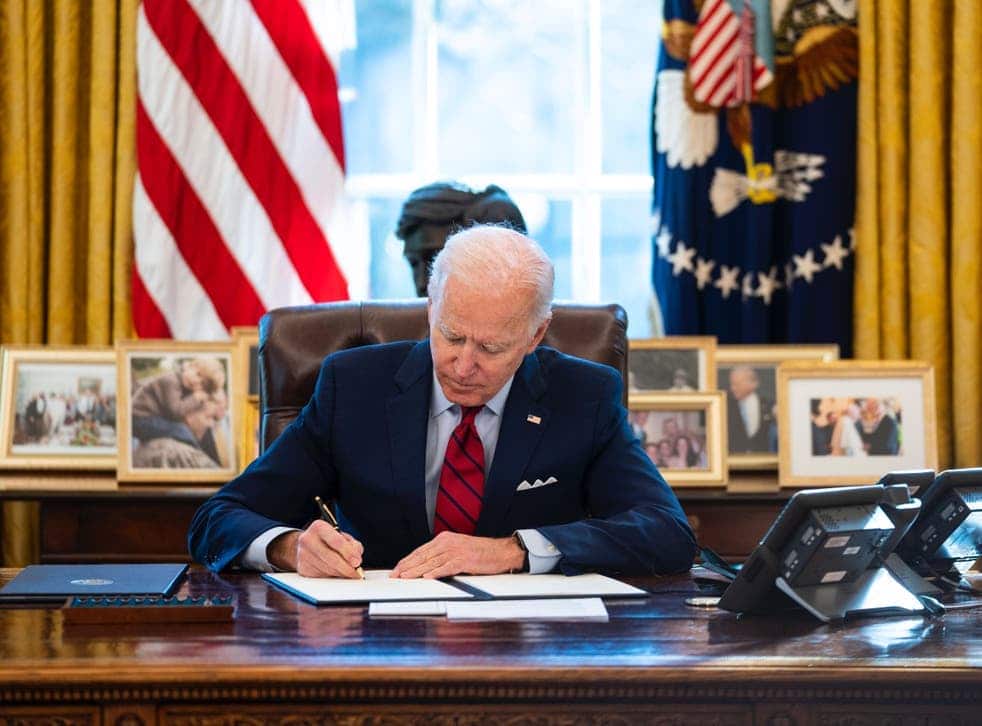
Episode 224: Engineering Trust In The Cyber Executive Order
In this spotlight edition of the podcast, sponsored by Trusted Computing Group* Thomas Hardjono and Henk Birkholz join us to talk about President Biden’s Cyber Executive Order and how the EO’s call for increasing trust in federal IT systems is creating demand for TCG technologies
DEF CON: Security Holes in Deere, Case IH Shine Spotlight on Agriculture Cyber Risk
A demonstration at DEF CON of glaring flaws in software by agricultural equipment giants John Deere and Case IH raise the specter of remote, software-based attacks that could cripple farms and impact US food production.