A school that never sleeps? Cameras that go dark? A dead company hacked back to life? Welcome to the growing Internet of Zombie devices that threatens the security of the Internet.
Internet of Things
2023 Technologies to Secure Your Hybrid Workspace
For businesses looking to invest in the creation of a safer and more productive modern office environment, here’s a rundown of the top 2023 technologies to secure your hybrid workspace.
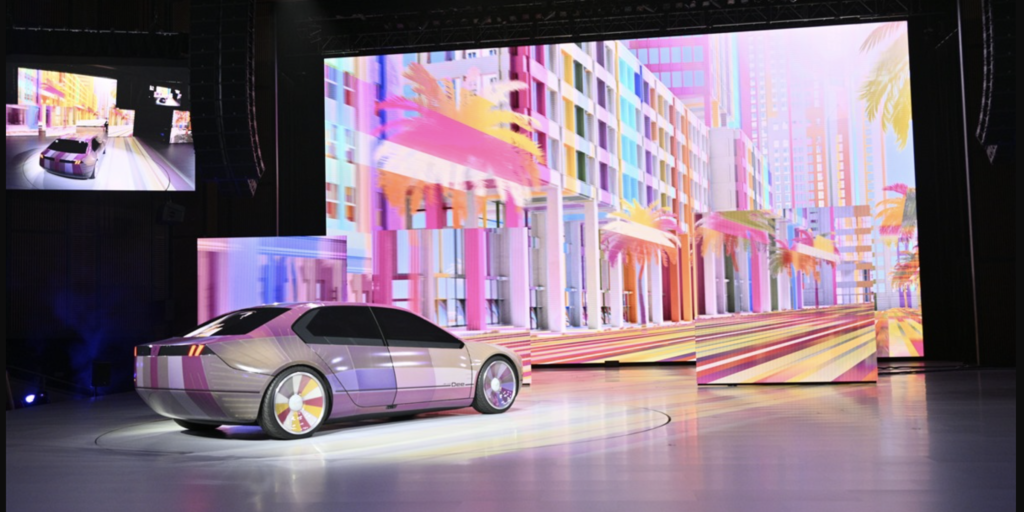
New Report Finds Auto Cyber Is A Dumpster Fire
Automakers swear that the security of their connected vehicles is their top priority. So how come researchers just found dozens of software flaws that could give hackers access to millions of cars?
The Future of IoT Security Standards
When it comes to measuring the security level of a device, a checklist of security ‘low hanging fruit’ is a good place to start. But more is needed, says Mike Sheward of Particle.io
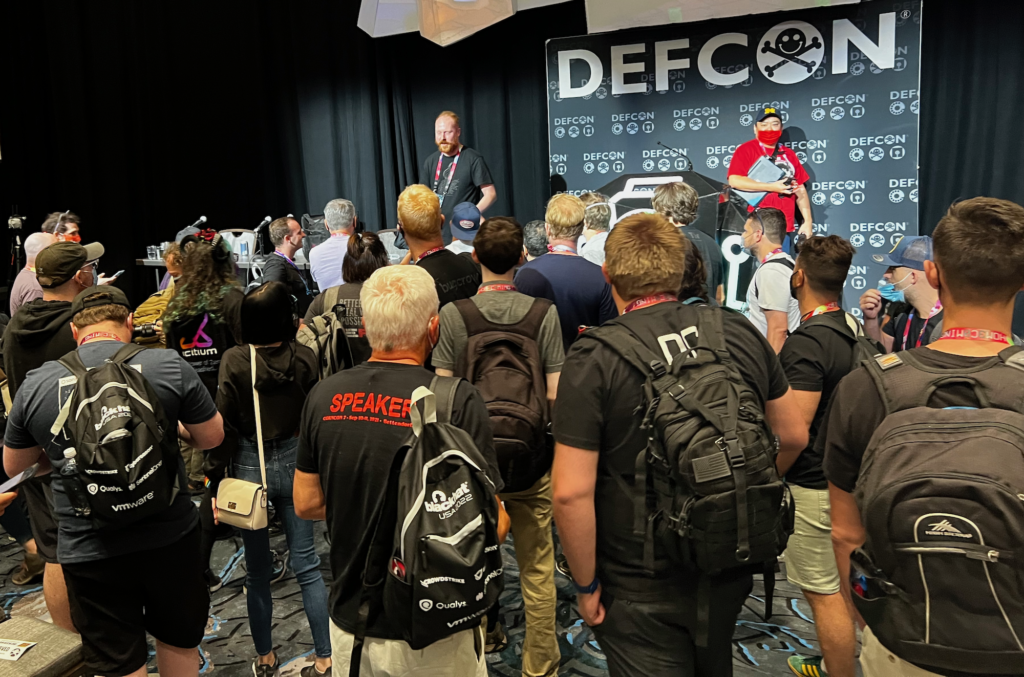
Episode 242: Hacking the Farm (and John Deere) with Sick Codes
In our latest podcast, Paul caught up with Sick Codes (@sickcodes) to talk about his now-legendary presentation at the DEF CON Conference in Las Vegas, in which he demonstrated a hack that ran the Doom first person shooter on a John Deere 4240 touch-screen monitor.