In this Spotlight Edition of the Security Ledger Podcast: identity is at the root of many of the security problems facing the Internet of Things, from vulnerable and “chatty” endpoints to a lack of robust update and lifecycle management features. To figure out how we might start to build a more secure IoT ecosystem, we invited Judah Aspler, the Vice President of IoT Strategy at Certified Security Solutions, or CSS Security in to talk about how more agile PKI infrastructure is one element in scaling the Internet of Things without creating a giant security mess.
connected devices
Exploits in Samsung Hub Put Smart Homes at Risk
There is more alarming security news for consumers with smart devices at home: hackers can take remote control of video cameras, thermostats, smart locks or other IoT devices by exploiting vulnerabilities discovered in Samsung’s SmartThings Hub, according to a report by Cisco Systems’ Talos research group.
Expert says: Hack your Smart Home to Secure It
Smart home security starts at home, according to researcher Michael Sverdlin who says that consumers should explore the security of their smart home technology and consider simple modifications or hacks to remove insecure or promiscuous features.
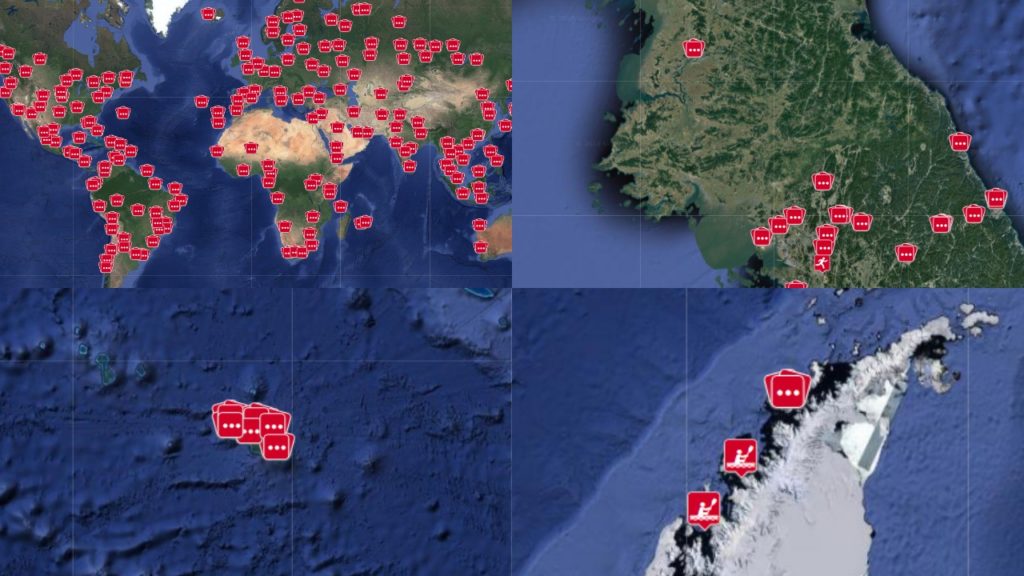
Fitness apps: Good for your health, not so much for military security
Fitness apps are proving to be a lot less beneficial to military security than they are for military fitness. That after researchers in the Netherlands discovered that data from the Polar fitness app revealed the homes and habits of those exercising in clandestine locations around the world, including intelligence agencies, military bases, nuclear weapons storage sites and embassies.
Opinion: With Internet of Things, Devices become Insider Threat
Connected devices aren’t just fodder for botnets. They increasingly act as malicious “insiders” capable of spying on their surroundings and providing valuable intelligence on homes and offices, argues Yotam Gutman of the firm Securithings in this industry perspective.