In this episode of The Security Ledger Podcast (#255) host Paul Roberts interviews Niels Provos of Lacework about his mission to use EDM to teach people about cybersecurity.
Episode 205 – Google’s Camille Stewart: InfoSec’s Lack of Diversity is a Cyber Risk
In this interview, Camille Stewart, Google’s Head of Security Policy for Google Play and Android explains how understanding how systemic racism influences cyber security is integral to protecting the American people and defending the country from cyber adversaries.
Drive-By Malware Uses Google Sites for Drive by Download Attacks
New malware, LoadPCBanker, is leveraging Google’s Sites to spread via drive-by download attacks, according to a new report. Companies are advised to block uploads and downloads from the service.
Podcast Episode 135: The Future of Passwords with Google Account Security Chief Guemmy Kim
In this week’s episode (#135): we continue our series on the future of Passwords as we are joined by Guemmy Kim, a group product manager at Google in charge of that company’s account security initiatives.
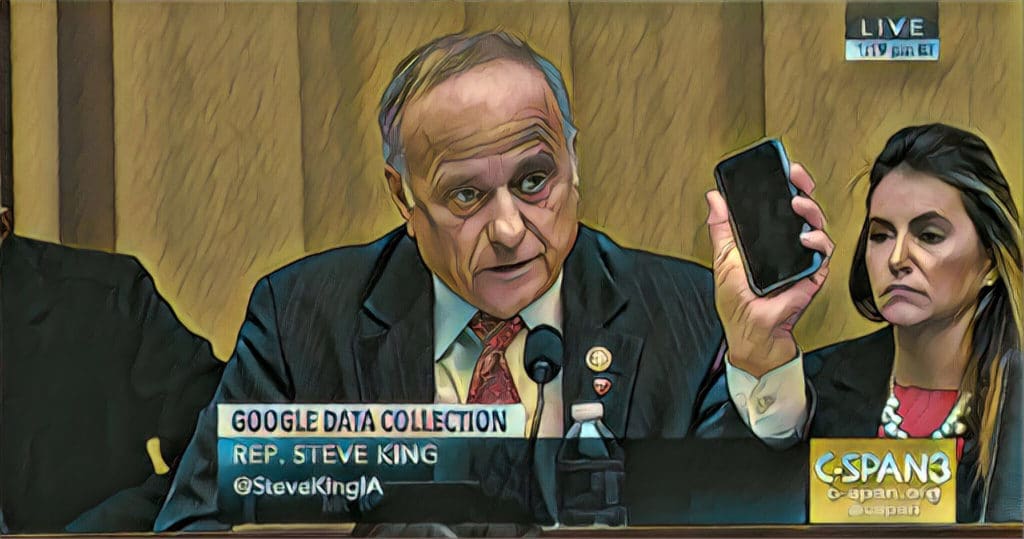
Waiting for Federal Data Privacy Reform? Don’t Hold Your Breath.
Despite a litany of high-profile data breaches, federal action on data privacy is unlikely to go anywhere in 2019 as partisanship and lack of technology literacy complicate Congressional action.