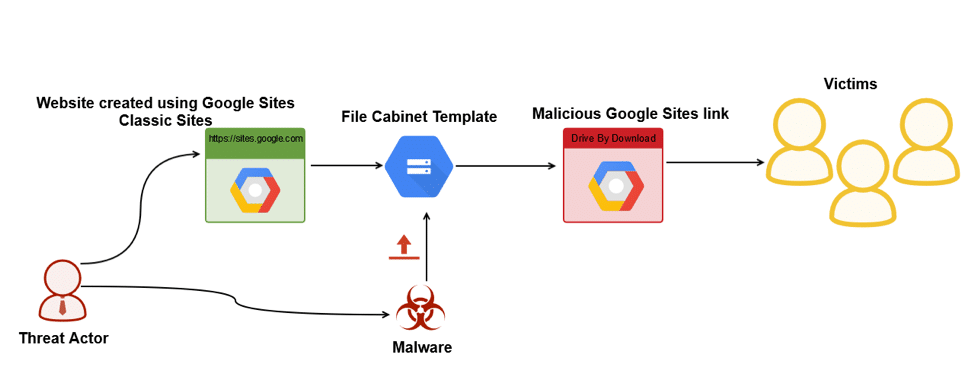
New malware, LoadPCBanker, is leveraging Google’s Sites to spread via drive-by download attacks, according to a new report. Companies are advised to block uploads and downloads from the service.
Researchers have identified “drive-by” malware that exploits Google Sites, using the service’s File Cabinet to deliver malicious code that can steal victims’ data and observe their online behavior.
The malware–called “LoadPCBanker”–has apparently been around since early 2014 but has only recently discovered by cloud security firm Netskope, which published a report detailing the malware Tuesday. At this time, researchers said it is targeting users in Brazil.
“We called this a drive-by attack, because the user was linked directly to a file download–not a website where they had to click on a link or presented with a dialog that warned them a file would be downloaded,” Raymond Canzanese, an architect at Netskope, told Security Ledger.
Podcast Episode 116: Cryptojacking and MikroTik’s Bad-Feeling Feel Good Patch Story
Researchers traced the malware back to early 2014 using in-house systems, sample repositories, and the Netskope Threat Intelligence Framework. However, LoadPCBanker’s use of Google Sites appears new in a wave of attacks researchers discovered that started in February of this year, they said.
These new attacks are particularly dangerous because of Google’s trust relationships with so many Web users, Canzanese said.
“Users generally put implicit trust in Google, which makes them more likely to download files and click on links hosted within their services,” he said.
Moreover, while other Google services such as Gmail have protections in place to block malicious file uploads, Google Sites File Cabinet does not, which makes the service exploitable by LoadPCBanker, researchers said.
An inside job
LoadPCBanker works by using classic Google Sites to create a website, then uploads the malicious code using the Google Sites file-cabinet template, according to Netskope. After, it sends the resulting URL to potential targets.
Devices’ UPnP Service Emerges as Key Threat to Home IoT Networks
“The victim receives an e-mail with some text about a reservation confirmation with a link to the file on Google Sites,” Canzanese said. “If they click on the link, a file is downloaded that is an executable with an icon and a name that makes it look like a PDF file. Once they click on the executable, the malware is installed and runs silently in the background.”
After system infection, LoadPCBanker can collect screenshots, clipboard data and keystrokes of victims, using an SQL channel to exfiltrate them, researchers said.
“If the attacker gets access to critical personally identifiable information (PII) like passwords, online activity and credentials, these could be used directly or sold on the black market,” Canzanese said.
Brazilian online banking a target
Researchers believe LoadPCBanker is targeting Brazil for a number of reasons, one of which is as an advanced emerging economy with the ninth largest GDP in the world, they said.
Brazil also is the largest national economy in Latin America and was an early adopter of online banking technology, with a high concentration of automated teller machines per capita.
However, the country’s law enforcement has a “weak posture” on identifying and responding to cyber crime, making it an easy target for cyber criminals, according to Netskope. Indeed, threat actors targeting Brazillian users historically are among the prominent contributors in the cybercrime ecosystem that uses banking malware, researchers said.
Netskope’s analysis observed threat actors using LoadPCBanker in particular to maintain surveillance of a specific set of 20 compromised machines by capturing screenshots of activity on those machines, researchers said.
“We derived this because we noticed a lot of infected machine responses, but only a few were being actively surveilled,” researchers wrote in the report.
Know your domain
To avoid falling victim to LoadPCBanker, Netskope recommends that enterprises not using Google Sites for hosting and downloading files create a policy to generically block all uploads and downloads from the service.
“They can also block external SQL connections to prevent it from being used as an exfiltration channel,” Canzanese said.
Common sense as well as simple education and awareness of frequently used sites and online services also will go a long way, Canzanese said. Users should always check the domain of a link before clicking on it, and know the domains they use frequently when logging into sensitive services, he said.
“Warn users to avoid executing any file unless they are very sure that they are benign,” Canzanese said. “For e-mailed links, make sure they come from users you know and that the contents were expected.”
Netskope also recommends that users to avoid executing any file unless they are certain that they are benign, even if the file is delivered from a legitimate-appearing Google sites.


