My oldest daughter had a “cyber” question for me the other day. That’s pretty unusual.
Here it is: she attended college in Maine and recently graduated. When she read last week that Maine’s government issued a notice that data for around 1.3 million Mainers was stolen as part of rolling attacks on the MOVEIT file transfer app, she was concerned. After all: Maine’s entire population is a bit over 1.3 million people, so the odds are that her data was exposed in this incident, right? Her question to me: “Dad: what should I do?”
What should you do? Pull your hair and scream? Throw your hands to the sky and plead “Why??!!” Slam your fist on the table and shout “I’m mad as hell, and I’m not going to take it anymore!!?” (A Boomer film reference my daughter almost certainly won’t get.)
If you’re interested in learning more about application security and secure design, check out my conversation with Chris Hughes, President at Aquia, CSO at Endor Labs, & Cyber Innovation Fellow at CISA and Saša Zdjelar, Chief Trust Officer, ReversingLabs in this webinar discussion.
Of course, the “credited” answer to this question isn’t much better than these existential laments. I told her that she should register for a credit monitoring service that would notify her if someone was trying to use her personal information to open new accounts or lines of credit, or if it turned up in cybercriminal forums.
Remember the Maine (Breach)
Maine is just the latest organization breached by hackers exploiting a vulnerability in the MOVEit file transfer application by Progress Software. Since May, more than 2,500 private- and public sector organizations have been attacked, including British Airways, the BBC, Colorado’s Department of Health Care Policy and Financing and the New York Public Schools, according to the firm EMISoft.
Based on a public notice published by the State of Maine, the exposed data almost all came from one of two state agencies: the Maine Department of Health and Human Services and the Maine Department of Education. Financial information like bank accounts or credit card numbers probably wasn’t part of the attackers’ haul.
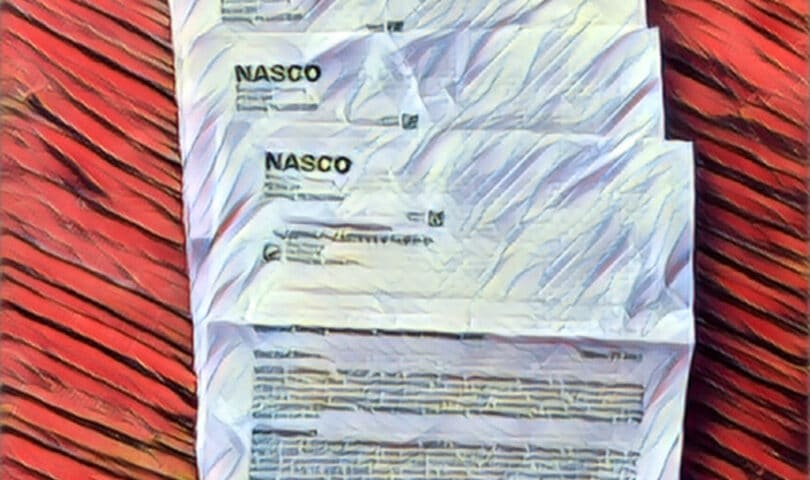
Private firms that get breached often offer their affected customers complimentary credit monitoring services as a (feeble) form of compensation. Maine -as far as I can tell – didn’t even offer that to its residents. As it turns out, however, my daughter was already entitled to free credit monitoring services via Experian – along with the rest of us. That, courtesy of NASCO, a claims administration provider to the health insurer Blue Cross Blue Shield of Massachusetts.
Like the State of Maine, NASCO also got hacked via the MOVEit vulnerability in May, 2023. The data affected in that attack: Our names, demographic information (address, phone number) email addresses, medical ID numbers, provider names, medical purchases and more.
With the offer of free credit monitoring from NASCO, I took the opportunity to get my daughters signed up for the service, offered via Experian. (My wife and I already subscribed, taking advantage of an offer from an earlier, unrelated data breach). I advised my daughters to plug in their personal information, including credit card- and bank account numbers so that they would be notified should that data turn up in a breach or otherwise be targeted.
It was a sad little right of passage for us: a sober acknowledgement of one grim reality of modern life: the utter lack of online security and safety.
Stolen data? Get used to it, kid.
My other piece of advice to my daughters? Get used to it.
Such is the reality for young people coming of age today in the application security shanty town that is the 21st century U.S. economy. Like the shanty towns that have sprung up in developing nations over the last century, the application ecosystem that has sprung up over the last three decades is sprawling, unregulated, ad-hoc and prone to shocking breakdowns and failures.
As there is in the physical world, there’s a cost to be paid for that lack of quality in the online sphere. These days, the end result of a lack of software “building codes,” for software consumers, is misery: an epidemic of hacks and data heists with consequences that ripple across individual lives, communities and our society.
Those failures in our application ecosystem lurk around every corner. The LockBit gang last week published 40GB of sensitive data from airplane maker and defense contractor Boeing after the company failed to pay a ransom to get access to their data back. In Ohio, a ransomware attack on Huber Heights, Ohio, revealed that many of its core city functions were shut down due to a ransomware outbreak. That’s just the latest of a string of ransomware attacks on communities across the U.S. in recent years including major cities like Oakland, California, New Orleans, Louisiana, Tulsa Oklahoma and Atlanta, Georgia.
Normalized Deviance
In a speech at Carnegie Mellon University, CISA Director Jen Easterly spoke of this as the “normalization of deviance” – including the fact that “technology products are released to market with dozens, hundreds, or thousands of defects, when such poor construction would be unacceptable in any other critical field.”
Director Easterly pointed out that the burden of this normalization falls on consumers “who are often least aware of the threat and least capable of protecting themselves.” And, indeed, at a personal level, those stamped envelopes in the mail expressing “deep regret” over a “regrettable” cybersecurity breach that exposed their sensitive information have become so common that we’re numb to them.
It doesn’t need to be that way. As with building codes, we as a society have the tools of change and transformation in our hands. Slowly (very slowly) the federal government is starting to wake up to that reality. CISA, the Cybersecurity and Infrastructure Security Agency, for example, recently published guidelines urging software makers to embrace “secure by design” principles and practices. Director Easterly has advocated the formation of “sustainable cybersecurity practices” that put consumer safety front and center “in all phases of the technology product lifecycle.”
As it stands, however, these guidelines and calls for change are little more than a polite ask. Neither CISA nor most other government agencies including the FTC, SEC or DHS have the legal tools to compel software makers to follow secure design, development or deployment principles. The application shanty town, in other words, continues to grow. Future generations, it is clear, will continue to pay the price.

Pingback: November 17 | cybersecurity update