Microsoft’s products are still a leading source of exploitable security vulnerabilities used by hackers, according to a report by the firm Recorded Future.
Eighty percent of the top exploited security vulnerabilities targeted the Microsoft platform in 2018, as researchers advise companies that haven’t already done so to abandon Microsoft’s Internet Explorer web browser.
2018 marked the second year in the row that the technology giant’s products were foremost in the cross-hairs of bad actors, according to a new report by Recorded Future. In the last year, eight of the top 10 exploited vulnerabilities targeted Microsoft, with the other two targeting Adobe and Google Android, respectively, according to the report by Recorded Future sales engineer Kathleen Kuczma. In 2017, seven of the top 10 exploits targeted Microsoft, a shift from the previous two years, when Adobe was the top target.
Report: Small, Stealthy Groups Behind Worst Cybercrimes
Internet Explorer…come on down!
2018’s No. 1 exploited vulnerability was an IE vulnerability nicknamed “Double Kill,” more formally known as CVE-2018-8174. Double Kill appeared in four exploit kits–RIG, Fallout, KaiXin, and Magnitude–some of which were used to spread the malware Trickbot through phishing attacks, according to the report.
CVE-2016-0189–another Internet Explorer (IE) bug and the top vulnerability in 2016 ranked second in 2017. It was still was knocking around in 2018 through an association with five different exploit kits, researchers found.
Researchers advised organizations to consider ditching Internet Explorer and other browsers in favor of Google Chrome, as well as to be wary of any website still using Flash Player–which is becoming less common but still exists as an Internet technology.
“As Adobe winds down development of its Flash Player, which used to have a number of zero-day vulnerabilities that were often included in exploit kits, cyber criminals have resorted to exploiting Microsoft–another ubiquitous piece of software that is used by one out of every seven people,” Kuczma said. “Cyber criminals target the software that has the largest potential of reward and scope of targets, which makes Microsoft, for now, an easier target.”
Silver Linings Run Book
Despite the bad news for Microsoft, the report overall had some good news in terms of vulnerabilities themselves. The number of exploits kits continued a downward trend that started a few years ago, decreasing 50 percent in 2018 with only five exploit kits versus 10 in 2017, researchers found. Researchers cited shifts to more secure browsers and specific victim targeting as two reasons for the drop in exploits, among others.
Moreover, similarly to 2017’s report, only a few vulnerabilities from past reports made it to the top-10 list last year. 2017’s top exploited vulnerability–a Microsoft Office exploit, CVE-2017-0199–moved to fifth place, mainly because of its continued inclusion in the widely used ThreadKit exploit package.
Still even as exploit kits declined, the number of vulnerabilities every year continues to grow, Kuczma told Security Ledger. She said the report reinforces the importance of popular software developers staying vigilant in patching and monitoring for exploited vulnerabilities in the wild.
“Now more than ever, companies are looking and publishing vulnerabilities in an effort to stymie targeting activity and are employing more bounty hunters to find these gaps,” she said.
Recorded Future uses a list of 167 exploit kits as one of the parameters in their current vulnerability report. It also expanded its research this year to include Remote Access Trojans (RATs) in its determination of the top exploited vulnerabilities–in part because of their increase in usage due to their role as multipurpose malware, researchers said.
The No. 2 vulnerability of 2018 also was the only Adobe Flash Player exploit on the list–CVE-2018-4878. Researchers also found it in multiple exploit kits, but most notably Fallout, which was used to distribute GandCrab ransomware and can be purchased for about $300 a week and $1,100 a month on the dark web.
UPDATED: Damning Report Has AMD Investigating Critical Vulnerabilities in Ryzen, EPYC Chips
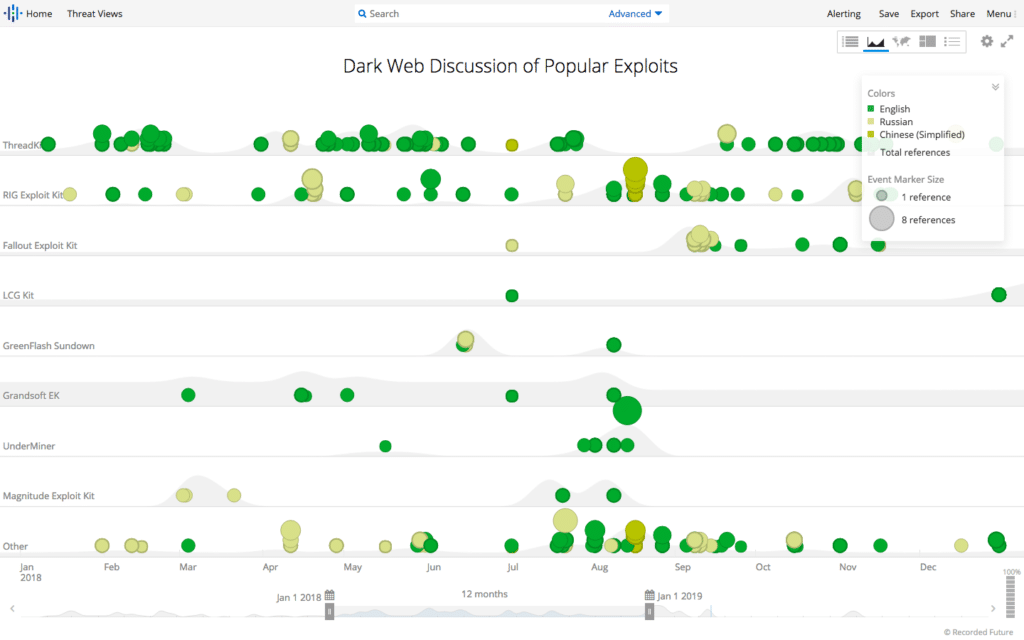
Indeed, researchers also used the dark web as a resource to discover which exploited vulnerabilities had the most traction with bad actors in 2018. Among exploit kits associated with the top vulnerabilities, ThreadKit–which included four of the top 10 vulnerabilities–was the most discussed on dark web sources in 2018, they found. The last update of this particular exploit kit was December 28 by a dark-web forum user called “mrbass,” who generously added an Adobe zero-day vulnerability to the kit, which was last selling for $400.
Still exploited after all these years
Recorded Future researchers also observed an exploit with a longer than usual useful life still at work in 2018. That would be the aforementioned IE bug CVE-2016-0189, which had the honor of making the list of top 10 exploited vulnerabilities three years in a row.
“We have seen only a few vulnerabilities remain in the top ten from year to year because either those vulnerabilities are successfully patched or the authors of the exploit kits containing those vulnerabilities are arrested,” Kuczma told us.
She cited the exploit’s lack of dependence on one version of IE–which gives it more reliability as a vulnerability as a reason for its staying power, as it affects IE 9 through 11–as a reason this particular exploited vulnerability has stuck around.
Bad actors have used this versatility, to incorporate the bug successfully into a variety of various exploit kits over the years, including five in 2018–Underminer, Magnitude, Grandsoft, KaiXin and RIG. The exploit also lacks a solid patch; restricting access to two common dynamic-linked library files, VBScript.dll and JScript.dll, are the only current workarounds, researchers said.
Other top 2018 vulnerabilities were notable because of their frequent appearance in different types of malware, researchers found. Two in particular-CVE-2017-11882 and CVE-2017-0199–were identified in 10 and eight pieces of malware, respectively. Both were used in Trillium’s Security Multisploit Tool, which included four of the top 10 vulnerabilities and was discussed at length on Hack Forums and Nulled Forum to positive acclaim, researchers found.
Expert advice: Take vulnerabilities seriously
Even with exploited vulnerability kits on an apparent decline, Recorded Future researchers advised organizations to maintain an awareness of known vulnerabilities on their systems, in particular the ones identified on the 2018 list as those most exploited.
“Official vulnerability databases, and even scanning tools, cannot arm organizations with one key metric: the overlap between the vulnerabilities in the systems you use and the ones that are being actively exploited by threat actors,” Kuczma wrote.
Recommendations for organizations running Microsoft as well as other targeted platforms include not only patching all of the vulnerabilities Recorded Future identified in its research, but also older vulnerabilities, which have an average shelf life of about seven years.







Pingback: Asus ShadowHammer suggests Supply Chain Hacks are the New Normal | Raymond Tec