Podcast: Play in new window | Download (Duration: 43:34 — 49.9MB) | Embed
In this episode of the Security Ledger podcast (#121): the Librarian of Congress gave a big boost to right to repair advocates in late October when she granted exemptions provisions of the Digital Millennium Copyright Act covering repair of most electronic devices. We talk to US PIRG’s Right to Repair campaign coordinator Nathan Proctor about the ruling and what it means for efforts to pass state level right to repair laws. Also: President Trump signed a major overhaul of the Department of Homeland Security’s cyber security operation into law last week. Jamil Jaffer of the firm IronNet joins us to talk about what it will mean for U.S. cyber readiness and about the need for more international coordination on cyber threats.
DMCA: Hacked by Librarian
One of the strangest rituals in modern American life comes every third year, when the obscure Librarian of Congress finds him or herself thrust into the center of an always-roiling controversy over software piracy, software protection and consumer advocacy. That’s because it is the Librarian’s responsibility to issue exemptions to copy protections enshrined in the 1998 Digital Millennium Copyright Act. With the stroke of a pen, the Librarian can wave rules preventing owners from circumventing digital rights management (DRM) protections covering everything from software to movies and music. As DRM has been used to constrain use of more and more software-driven “stuff,” the Librarian of Congress and her exemptions have become a set piece in the technology culture wars.

So it was on October 25th, when the Librarian handed down the latest list of exemptions (PDF) -the first since 2015. She renewed existing exemptions, including those for “jailbreaking” smart phones and for “motorized land vehicles” including tractors and other farm equipment. Going further, the Librarian of Congress created a broad exemption for “jailbreaking” computer programs for the purposes of repair. That exemption includes smart vehicles, appliances, computers, toys, and other Internet of Things devices.
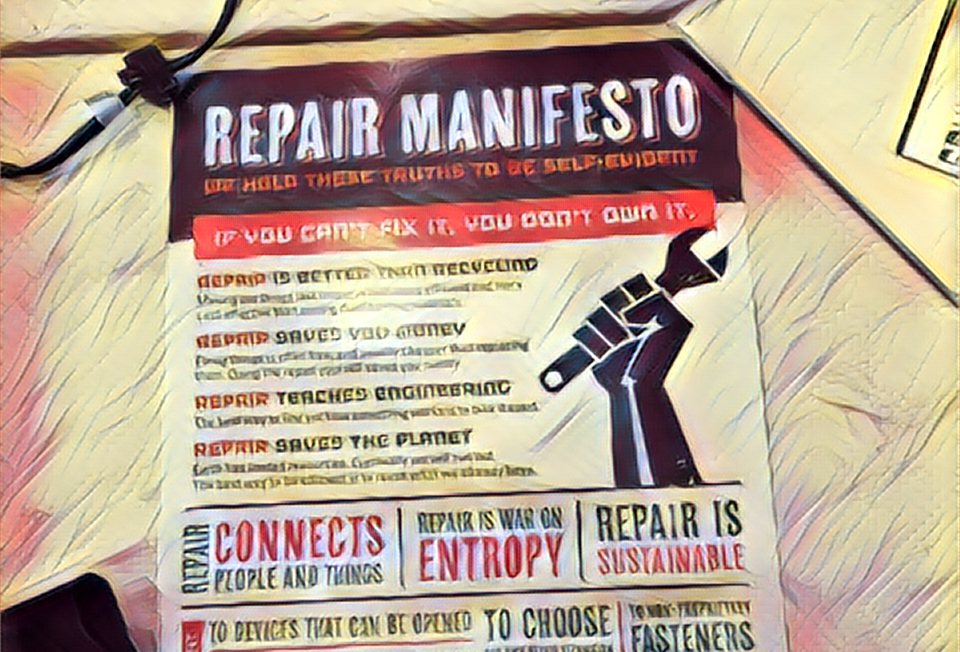
Media outlets trumpeted the ruling as a big win for right to repair advocates. But was it? Our first guest this week, Nathan Proctor, heads up the US Public Interest Research Group (PIRG)’s right to repair campaign. In this Security Ledger interview, Proctor notes that having the right to defeat DRM is different from actually being able to do it. He and I talk about how the long arm of the DMCA now stretches deep into our economy, depriving owners and consumers of the right to modify and repair a wide range of devices. We discuss the ongoing effort to pass right to repair laws in 19 states and how the Librarian of Congress’s ruling may play into the national conversation about the right to repair.
Is the world ready for a cyber NATO?
In our second segment this week: U.S. President Donald Trump signed bi-partisan legislation last week that shook up the Department of Homeland Security. The new legislation consolidates DHS’s role as the U.S. government’s main agency for managing cyber security and creates a new, independent branch dedicated to cyber security: the Cybersecurity and Infrastructure Security Agency (CISA). The bill was hailed as a much needed reform that will consolidate both offensive and defensive cyber capabilities under one roof and hasten U.S. government response to critical threats and incidents, like the hacking of the Office of Personnel Management (OPM).
But will the reorganization really have the desired effect on the security of U.S. government agencies and the broader U.S. economy? Our guest in the second segment of our podcast, Jamil Jaffer of the firm IronNet, has his doubts. While the DHS re-org may make that agency more effective, Jaffer told me, there needs to be much more and much closer coordination between private and public sector organizations on cyber security. Jaffer said that cooperation and information sharing – along the lines of international alliances like NATO – are the best mechanism for fighting borderless and stealthy cyber threats. Furthermore, national governments, including the U.S. government, have to be much more willing to climb into the trenches with leading corporations and private sector firms that are being targeted by attackers.
Check out our whole conversation in the second half of the show!