The federal government charged two Iranian men for orchestrating a nearly three-year-long international hacking and extortion scheme that deployed ransomware which to date has caused more than $30 million in losses to its victims, which include hospitals, municipalities and public institutions.
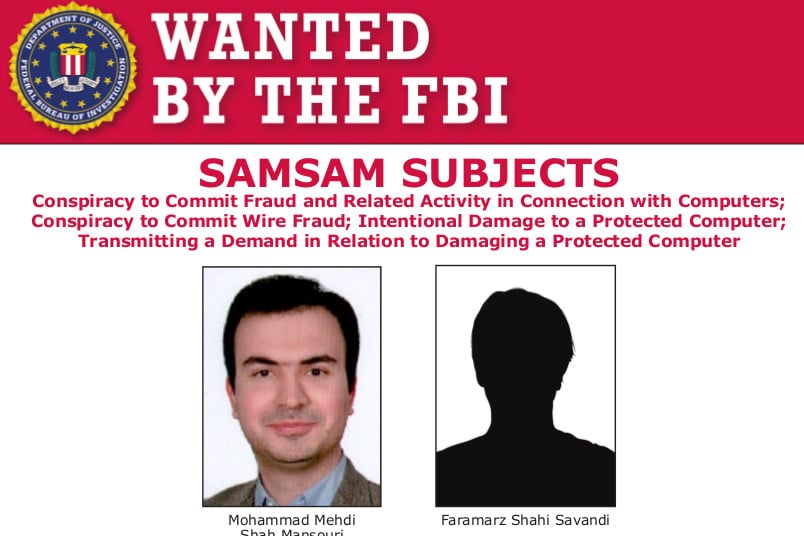
A federal grand jury in New Jersey has indicted Faramarz Shahi Savandi, 34, and Mohammad Mehdi Shah Mansouri, 27, both of Iran, on six charges for creating malware, known as “SamSam Ransomware,” and then deploying it on victims’ computers to demand Bitcoin payments beginning in December 2015. So far, the pair have collected $6 million in ransom payments, with the last known attack occurring on Sept. 25 of this year.
An indictment filed in the United States District Court, District of New Jersey outlines a long and damning list of charges and evidence against the two, who are alleged to have created the ransomware and enacted the scheme from inside Iran, targeting numerous organizations across 10 U.S. states and Canada. It also demonstrates how Iran is rising as a significant cyber-criminal threat in its own right alongside more widely recognized and known threats from China and Russia, officials said.
“The allegations in the indictment unsealed today—the first of its kind—outline an Iran-based international computer hacking and extortion scheme that engaged in 21st-century digital blackmail,” Assistant Attorney General Brian Benczkowski said in a statement, adding that the indictment also shows the federal government’s commitment to cracking down on state-sponsored cyber crime.
“As today’s charges demonstrate, the Criminal Division and its law enforcement partners will relentlessly pursue cybercriminals who harm American citizens, businesses and institutions, regardless of where those criminals may reside,” he said.
Elaborate and sophisticated ransomware attacks
Ransomware is one of the oldest forms of malware used by cyber-actors to extort money from victims, but lately researchers have found it’s going out of fashion, replaced by cyber crimes like crypto-jacking that give hackers a steady stream of income rather than a one-shot boost.
Indeed, Kaspersky researchers said earlier this year they saw a 30 percent year-over-year drop in ransomware from 2016 to 2017, evidence they said proved that authors of this type of malware appear to be losing interest.
Savani and Mansouri apparently didn’t get the memo. They created the first version of SamSam in December 2015 and later updated it in June and October 2017 as they continued their ransomware campaign, according to the federal indictment.
The methods the Savandi and Mansouri used in their scheme show sophistication, proving the attack was well-thought out, well-planned, and that these two know their way around contemporary methods hackers typically use to deliver malware and conduct such nefarious activity with success.
Savani and Mansouri used Tor--a computer network designed to facilitate anonymous communication over the Internet and known widely to be used by cyber criminals–to keep their activities quiet, according to the indictment. They also efficiently conducted their actions across overseas networks, using Iran-based Bitcoin exchanges to extort money from victims thousands of miles away.
Evidence also shows the pair did extensive research to select and target potential victims, identifying network vulnerabilities to infiltrate targeted computer systems, and doing reconnaissance on a network sometimes for weeks before deploying SamSam on a system. However, as the campaign wore on, the time between reconnaissance and deployment would lessen, with Savani and Mansouri deploying SamSam within hours of getting into a system, according to the indictment.
Like most successful cyber criminals, Savandi and Mansouri also disguised their attacks to appear like legitimate network activity and conducted it outside of regular business hours, when companies would be less likely to notice irregular network activity and take steps to block and/or mitigate attacks, according to the indictment. These methods served to cripple regular business operations of victims of their attacks, investigators said.
Multiple charges, multiple victims
Specifically, Savandi and Mansouri face six counts of federal crimes for their activities: one count of conspiracy to commit wire fraud; one count of conspiracy to commit fraud and related activity in connection with computers; two substantive counts of intentional damage to a protected computer; and two substantive counts of transmitting a demand in relation to damaging a protected computer, according to the indictment.
The indictment also reveals 11 of the more than 200 victims affected by SamSam. Government agencies and other public-run institutions affected included the City of Atlanta; the City of Newark, New Jersey; the Port of San Diego, California; the Colorado Department of Transportation; the University of Calgary.
Six health care-related entities also are named as victims in the indictment: Hollywood Presbyterian Medical Center in Los Angeles; Kansas Heart Hospital in Wichita; Laboratory Corporation of America Holdings, commonly known as LabCorp; MedStar Health; Nebraska Orthopedic Hospital now known as OrthoNebraska Hospital; and Allscripts Healthcare Solutions Inc. out of Chicago.
Several U.S. government agencies cooperated on the investigation, including the FBI, the Justice Department and the State of New Jersey–as well as authorities in Canada and the United Kingdom. Specifically, the FBI’s Newark Field Office investigated the case, while Senior Counsel William Hall Jr. of the Criminal Division’s Computer Crime and Intellectual Property Section and Assistant U.S. Attorney and Chief of the Cybercrimes Unit Justin Herring of the District of New Jersey are prosecuting the case.
“This indictment demonstrates the FBI’s continuous commitment to unmasking malicious actors behind the world’s most egregious cyberattacks,” said FBI Executive Assistant Director Amy Hess. “By calling out those who threaten American systems, we expose criminals who hide behind their computer and launch attacks that threaten our public safety and national security.”
