President Trump’s decision to exit from the Iran nuclear deal doesn’t bode well for U.S. cybersecurity and likely will spur cyber attacks on a number of U.S. industries from the Islamic State, a new report from Recorded Future has found.
On Tuesday, Trump said the United States would not renew the waivers on sanctions against Iran and instead impose additional economic penalties. This combination basically means the U.S. will withdrawal from the 2015 Joint Comprehensive Plan of Action (JCPOA), more commonly known as the “Iran nuclear deal.” Experts on Iran’s cyber program say that sets the stage for confrontation.
Since 2009, Iran has responded to events that will have a negative economic impact on the country with cyber attacks against those who provoke them. In the United States they have previously targeted several specific industries–banks and financial services, government, critical infrastructure and oil and energy–using a network of contractors and universities to conduct state-sponsored cyber operations. Experts fear that the country may respond online – and in a more reckless fashion than before.
[You might also be interested in “China caught pushing Vulnerability Reporting Delays down the Memory Hole“]
“We believe that contractor selection for this response may favor speed and skill over trust and loyalty, resulting in the use of new or unproven contractors,” Levi Gundert, one of the writers of the report for Recorded Future, told Security Ledger. “New or unproven contractor’s actions could result in a destructive attack with potentially wider impact than originally envisioned by the Iranian government.”
Recorded Future said that a reactive response to the new U.S. sanctions may mean the country turns to less trusted contractors with questionable loyalties and ideologies to mount attacks quickly. This could make the scope and scale of the attacks all that more destructive because even the Islamic Republic may not be able to control them after they’ve started, the report found.

Recorded Future’s report–co-written by Gundert, Sanil Chohan and Greg Lesnewich–shines unprecedented light on the structure of Iranian contractors working for the Islamic Republic to accomplish offensive cyber campaigns. The bulk of the report is based on interviews conducted by Insikt Group with a former Iranian hacker with first-hand knowledge of the information who was living in Iran when he started one of country’s first security forums.
“Operation Ababil in 2012 saw the Iranian government authorize DoS attacks on America’s largest financial services companies as a response to the sanctions” – Recorded Future Insikt Group
The security intelligence firm leveraged third-party metadata and open source intelligence (OSINT) techniques using a variety of tools to facilitate the remainder of the research, with technical analysis regarding organizations and institutes in Iran’s offensive cyber program based on data collected from March 1 to April 30, 2018.
A track record of successful attacks
Iran already has successfully executed several known major cyber attacks against the United States, with two notable ones occurring in 2012 and 2014. The first targeted banks and crippled a number of online banking sites before they recovered. The second added critical infrastructure to Iran’s target in addition to dozens of banks, compromising the Bowman Avenue Dam in Rye, New York, and costing the banks millions of dollars in lost business.
[Also read: “Iran Taps Chafer APT Group amid Civil Aviation Crisis“]
While Russia and China get most of the attention as nations targeting the United States in global cyber warfare, Iran has become a threat in its own right in the past decade. In fact, five years ago, Iran joined the ranks of those countries as a leading source of distributed denial of service (DDoS) attacks.
“Iran’s offensive capabilities are not on par with Russia or China, but they have proven themselves highly capable of causing damage and they should not be underestimated,” Gundert said.
In 2009, Iran officially began a cyber operations program, which it used in the 2012 cyberattack against the United States. This attack was in response to several financial sanctions imposed by President Obama. In the campaign–dubbed Operation Ababil–the Iranian government authorized DoS attacks on America’s largest financial services companies as an immediate response to the sanctions, according to the Insikt Group’s hacker source.
“A quick response was top priority, so time and planning were forgone luxuries for the Iranian government,” according to the report. “Instead, the Iranian government opted for speed and the most capable actors, regardless of demonstrated ideology.”
In 2014, Iran launched another retaliatory attack on U.S. businesses, this time targeting the network of the Sands Las Vegas Corporation. This attack was in response to Sands’ CEO Cheldon Adelson publicly suggesting that the United States should attack Iran with an atomic weapon. Again, Iran acted quickly with little preparation or thought on which contractors to use in the attack.
Rapid response, less control
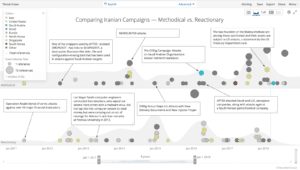
The impulsiveness of these attacks is in contrast to malware already identified by security researchers that Iran has developed to extract data from strategic intelligence targets such as U.S. military contractors, Middle East energy companies and university research networks, according to the report.
Typically, Iran uses a tiered approach in its cyber operations program, according to the report. An ideologically and politically trusted group of middle managers take intelligence priorities and turn them into segmented cyber tasks that the government then bids out to multiple contractors. The system creates a competitive scenario for the more than 50 contractors vying for the jobs, pitting them against each other for influence with the Iranian government, according to Insikt Group’s source.
When pursuing these so-called “quick-turn cyber operations” in reaction to specific events, however, the Iranian government “will weigh religious and political reliability against offensive skills,” a decision that gives the Islamic Republic less control over the outcome of the attack, according to Recorded Future.
Preparation for imminent attacks
Given Trump’s action on the Iran nuclear deal, U.S. businesses in the previously mentioned sectors–banks and financial services, government departments, critical infrastructure providers, and oil and energy–should expect attacks in the next several months, if not faster, according to the report.
Insikt Group already analyzed Internet traffic relating to various institutes affiliated with the Iranian cyber ecosystem beginning March 1 for two months, observing suspicious activity. However, it’s unclear whether this activity was related to preparation for the U.S. announcement and forthcoming attacks, according to the report.
No matter, Western businesses should continue to closely monitor geopolitical events initiated by the United States or Europe that affect Iran and know that attacks could result from any political action against the Islamic State, experts advised.
“We believe American businesses should be aware of Iran’s history and the likely response that these economic sanctions will trigger,” Gundert said. “Specifically, the financial services and energy industries should be preparing for the Iranian government’s response.”
Western commercial threat intelligence programs also should track emerging tactics, techniques and procedures on the Iran’s prominent security and hacking team Ashiyane, specifically, to determine the efficacy of existing security controls, Recorded Future advised.


Iran has tremendously grown in the cyber domain since past 5 years. Keeping in mind the past events, they have enough capability to carry out successful attacks. Iran will be successful if they hit the private sector companies. The US government should take proactive approach and disrupt Iran’s program before an attack is launched.
Pingback: DHS announces New Cybersecurity Strategy | The Security Ledger