Podcast: Play in new window | Download (Duration: 37:07 — 42.5MB) | Embed
In this week’s episode of the Security Ledger Podcast (#109): what lurks in the dark recesses of online information operations? How about a secret “US Freedom Army” linked to Russia? Dave Aitel of Cyxtera joins us to talk about it. Also: hacking critical infrastructure isn’t just for nation states anymore. Cybereason joins us to talk about its recent report on cyber criminals hacking into industrial control systems.
Psst! Want to join the Freedom Army?
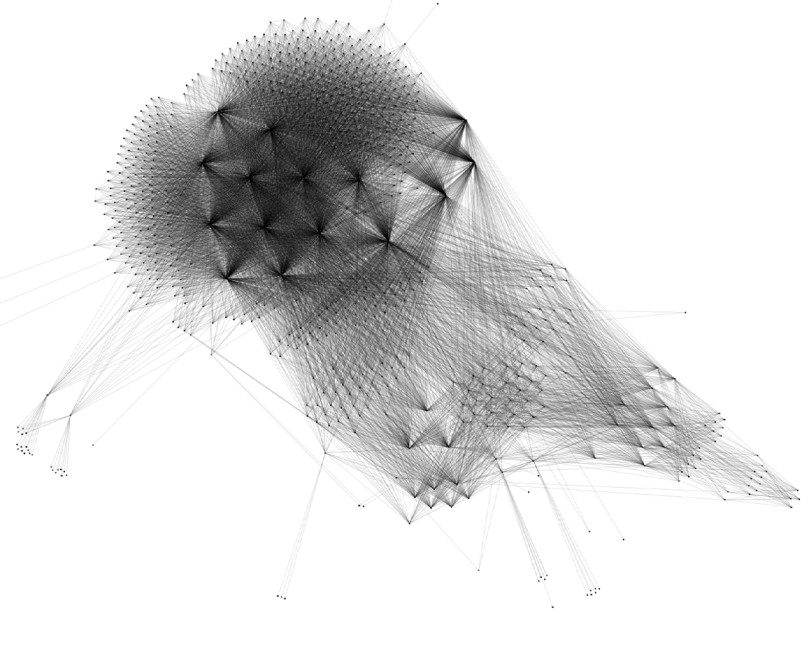
In the wake of the 2016 Presidential election, studying social media activity has gone from a niche obsession for a few social scientists to something akin to a national security priority. New analyses of the activity of twitter bots and networks of fake social media profile now pop up frequently, and just as frequently garner mainstream media attention.
But what is hiding out there among the online influence campaigns? You might be surprised, says Dave Aitel, the Chief Technical Security Officer of the Threat Management and Analytics Division of the firm Cyxtera. Dave recently completed an analysis of Twitter bot data. Among the revelations: many efforts to organize real world gatherings. Those include the “US Freedom Army,” a quasi military organization promoted via Twitter and other social media to U.S. survivalist groups.
[You might also be interested in: U.S. sanctions Russian companies, individuals over cyber attacks]
As frightening as that sounds, Aitel is skeptical of both social networks’ efforts to clamp down on bots and other false accounts and efforts to understand the scope of the online bot problem. Platforms like Twitter still have a financial incentive to keep bots and front accounts active. Until the economics of such networks change to penalize traffic from false and automated accounts, Aitel believes, it is unlikely we’ll see progress in reducing the number of bots.
“In order to get rid of (information operations) we have to find a way to penalize Twitter for having bots, financially, because right now they’re incentive-ized to encourage bots,” – David Aitel, Cyxtera.
Aitel cautions the growing ranks of researchers trying to understand online influence campaigns. The sheer volume and diversity in online disinformation and influence campaigns make it easy to misunderstand the shape of online activities or, even worse, engaging in what Aitel described as “auto ethnography.” Check out our full conversation in this week’s podcast.
Critical infrastructure hacks: not just for nation states anymore
When the firm Cybereason set up a honeypot network designed to look just like a functioning industrial control system environment, they were expecting to attract a few flies. What they weren’t expecting was a swarm of online attackers, including one who managed to compromise the network and then offer it up for sale on a cyber criminal bulletin board.
But Ross Rustici, Cyber Reason’s Senior Director of Intelligence Services says that we shouldn’t be surprised that rank and file cyber criminals have taken an interest in critical infrastructure systems.
[You might also like: FBI, DHS warn Russian Dragonfly Group Still Targeting US Critical Infrastructure]
Rustici says that, while these attackers aren’t as stealthy and sophisticated as nation-state actors, they hardly script kiddies, either. Rather, they knew what kind of system they had compromised and how to move and operate within it. Their interest in critical infrastructure systems may be a worrying sign – suggesting that profit motivated attackers and attacks may be in the cards for critical infrastructure operators.

Pingback: Podcast Ep. 109: Unpacking The Freedom Army & Other Online Info Ops - Secure Signal NYC