North Korean state-sponsored hacking group Lazarus is believed to be behind a recent crypto jacking attack on several banks with an unexpected twist–the use of a Trojan that tricked a company employee into downloading malware, according to Kaspersky Lab.
Kaspersky researchers made what they call the “unexpected discovery” while assisting with incident-response efforts to an attack on a cryptocurrency exchange, a type of attack for which threat actor Lazarus has become known.
However, the attack–which researchers dubbed “AppleJeus”–also was unique in that it used malware developed for MacOS, the first time researchers have identified the hacker group doing so, according to a post on the Kaspersky blog.
[Also read: Cisco Talos: VPNFilter malware capable of stealing data, infecting IoT endpoints]
“To ensure that the OS platform was not an obstacle to infecting targets, it seems the attackers went the extra mile and developed malware for other platforms, including for macOS,” according to the post. “A version for Linux is apparently coming soon, according to the website. It’s probably the first time we see this APT group using malware for macOS.”
The attack also saw Lazarus falling back–pun intended–on an old malware tool called Fallchill, which the group previously used and “recently switched back to,” according to the post. US-CERT and other security watchdogs have noted recent re-appearances of the malware.
In this case, an employee of an unidentified global bank unsuspectingly installed the malware on a company computer after downloading a third-party cryptocurrency trading application recommended over email, researchers said.
Duped into malware installation
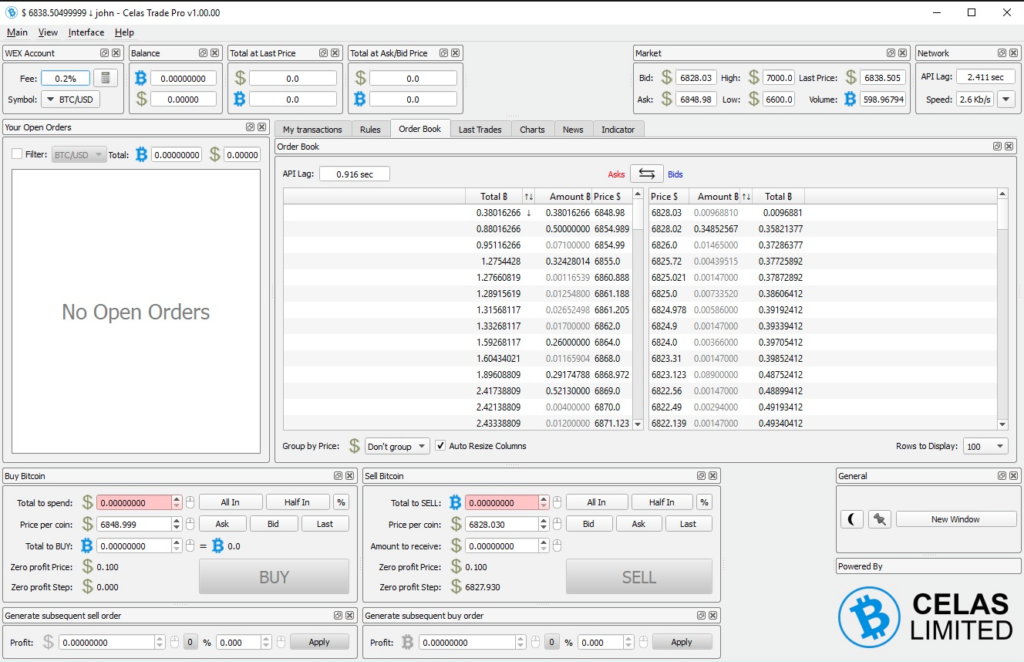
Attackers lured the employee with what appeared to be an update for legitimate software called Celas Trade Pro from Celas Limited which “showed no signs of malicious behavior and looked genuine,” according to Kaspersky.
By reconstructing the attack and tracing it back to its origin, researchers established that the installation of this program using a download link from an email infected a company computer with Fallchill, with the key fingerprint of the attack found rather unobtrusively at the end of the installation process, according to the post.
“At the end of the installation process, the installer immediately runs the Updater.exe module with the ‘CheckUpdate’ parameter,” according to the post. “This file looks like a regular tool and most likely will not arouse the suspicion of system administrators. After all, it even contains a valid digital signature, which belongs to the same vendor. But the devil is in the detail, as usual.”
That detail is that the main purpose of the Updater executable is to collect the victim’s host information and send it back to the server. In its investigation, Kaspersky discovered that the code writer developed this project under the codename “jeus,” which–along with the evidence that it’s Lazarus group’s first attack on Apple’s Mac platform–inspired researchers’ name for the incident.
Researchers discovered that the attack behaves more or less the same on both Windows and MacOS platforms, according to Kaspersky. “The fact that the Lazarus group has expanded its list of targeted operating systems should be a wake-up call for users of non-Windows platforms,” according to the post.
Foreshadowing of future attacks
Lazarus has been active in the financial sector for about the last 10 years, so a new attack that targets cryptocurrency comes as little surprise to anyone. Just last year the group was deemed responsible for a number of successful spear-phishing campaigns against South Korean cryptocurrency exchanges and Bitcoin and Monero mining outfits aimed at stealing funds to bankroll the regime of Kim Jong Un.
Its recent attack shows Lazarus has no signs of slowing down, and in fact is especially worrying for a couple of key reasons–its new OS target and its use of Celas software as a Trojan, according to Kaspersky.
The first shows Lazarus expanding its scope of platforms as developers and engineers themselves switch from Windows to MacOS, giving the hacking group an even wider attack surface.
“Apparently, in the chase after advanced users, software developers from supply chains and some high-profile targets, threat actors are forced to have macOS malware tools,” Kaspersky researchers said. “We believe that in the future Lazarus is going to support all platforms that software developers are using as a base platform, because compromising developers opens many doors at once.”
And while Kaspersky researchers can’t say for sure if Celas was compromised as part of the attack, the use of its cryptojacking application to lure someone into downloading malware shows Lazarus’ apparent interest in continuing to exploit the supply chain as a means of infection method, they said.
Researchers also issued a stern warning to businesses using third-party software–which it’s fair to say is the majority of them–not to automatically trust code running on their systems. For companies interested in running a tight security ship, you would think this would be no-brainer by now; however, it’s a method hackers continue to use to find success.
“Neither good-looking website, nor solid company profile, nor the digital certificates guarantee the absence of backdoors,” researchers wrote. “Trust has to be earned and proven.”


Pingback: Podcast Episode 116: Cryptojacking and MikroTik's Bad-Feeling Feel Good Patch Story | The Security Ledger