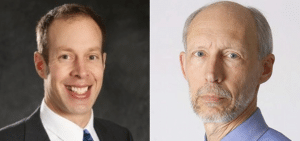
In this industry perspective, Dan Lyon and Taylor Armerding of the firm Synopsys discuss the impact of the FDA’s new Medical Device Safety Action Plan, which promises to improve the cyber security of medical devices…eventually.
The federal Food and Drug Administration’s (FDA) recently released Medical Device Safety Action Plan (PDF) begins with a declaration that would seem to put it and most of the cyber security industry in parallel universes.
![]()
According to the agency, “In recent years FDA, manufacturers, and healthcare entities have made tremendous strides to improve the cybersecurity of medical devices.” It does add the caveat that “all stakeholders, including FDA, must strive to keep pace with emerging threats and vulnerabilities.”
But in the other universe – the one we live in- cyber security experts say that whatever strides have been made are not “tremendous” and that the security of medical devices hasn’t kept pace with evolving threats.” The phrase “critical condition” keeps coming up.
[Read: DHS announces New Cybersecurity Strategy]
Consider the report last June to multiple congressional committees by the Health Care Industry Cyber Security Task Force: “Report on Improving Cybersecurity in the Health Care Industry” (PDF). That report concluded that the entire healthcare sector was plagued by a “severe lack of cybersecurity talent” and the widespread, continued use of legacy devices that were never intended to be connected to the internet.
Medical device security: a fail with many fathers
Limited financial resources, the use of legacy technology, a lack of understanding of the risks cyber threats pose, and limited education and awareness programs for health care professionals all combine to exacerbate the threat that cyber attacks pose to healthcare environments, the Task Force concluded.
It adds that “health care cybersecurity is a key public health concern that needs immediate and aggressive attention.” And then there was a report published a year ago by Ponemon titled “Medical Device Security: An Industry Under Attack and Unprepared to Defend,” (PDF) which noted that only 17% of device makers and 15% of healthcare delivery organizations (HDO) are taking significant steps to prevent attacks. Further, only 22% of HDOs say their organizations have an incident response plan in place in the event of an attack on vulnerable medical devices and 41% of device makers say such a plan is in place, Ponemon found.
With all that, will the FDA’s action plan move the needle on medical device security into the “fair” or even “good condition” category? Probably not.

Yes, the FDA’s proposals demonstrate an increasing awareness in both the public and private sectors that, as the report put it, “for the health care industry, cybersecurity issues are, at their heart, patient safety issues.” Ransomware attacks like the notorious WannaCry that temporarily slowed or took down major functioning at more than 80 hospitals in the United States, the U.K., and Canada a year ago have a way of getting the attention of doctors and hospital staff, since such attacks prevent healthcare providers from treating their patients.
That attention has informed the proposals in the FDA’s action plan, which Garrett Sipple, managing consultant at Synopsys Software Integrity Group (SIG), calls a “good step,” though he says nobody should expect federal regulations to fix completely, or even get control of, a “very complex problem.”
“The FDA has limited influence over the bigger picture,” he said. “You can’t just secure a product—you have to look at the entire system, including things done on the provider side.”
The proposals in the action plan, however, do line up with what most security experts have called security fundamentals—which would be an improvement. They include:
- Seeking congressional approval for increased premarket authority to require developers and manufacturers to “build capability to update and patch device security into a product’s design and to provide appropriate data regarding this capability to FDA.”
- Requiring as part of a premarket submission a software bill of materials (SBM) that would also be available to medical device customers and users.
- Updating premarket guidance to improve “protection against moderate risks (such as ransomware campaigns that could disrupt clinical operations and delay patient care) and major risks (such as exploiting a vulnerability that enables a remote, multi-patient, catastrophic attack).”
- Seeking authority to require device vendors to “coordinate disclosure of vulnerabilities as they are identified.”
- Exploring the creation of a CyberMed Safety (Expert) Analysis Board (CYMSAB), “a public-private partnership that would complement existing device vulnerability coordination and response mechanisms and serve as a resource for device makers and FDA.”
According to the report, the president’s proposed FY2019 budget includes funding to create a CYMSAB.
Larry Trowell, associate principal consultant at Synopsys SIG, said the software bill of materials in particular would be an improvement, since it would “remove a lot of the traditional black box approach that these types of devices have relied on for so long. Security that relies on attackers not having sufficient information on a system has been proven not to be a reliable method of protecting a device,” he said.
[Read: Report: Major attack on critical infrastructure expected due to increased risk from IoT]
But he wondered if the SBM would apply to updates as well, since it would provide “a level of validation that would ensure the correct measures have been taken that could be independently verified by whomsoever wished to.”
Quick fix on a long runway
Even if the plan is implemented quickly—and there is no set timeline for it—it will not be a quick fix for an industry where the life cycle for some devices can be as long as 10 to 20 years.
Sipple noted that patching a medical device is not a simple thing. “Even fixing one line of code is substantial for the amount of time it takes and the logistics of rolling it out,” he said. “There is the potential to introduce new problems when you mitigate one thing. And the amount of due diligence that you have to go through is significant.”
And Shawn Merdinger, an independent security researcher with a focus on healthcare, said the plan doesn’t cover all the bases—specifically the reality that government intelligence agencies stockpile vulnerabilities to use against criminals or hostile nation-states but sometimes fail to keep them secure.
That is not speculation—the United States has officially blamed North Korea for the use of a stolen National Security Agency (NSA) hacking tool to launch the WannaCry ransomware attack.
“The zinger question for the medical device industry is, how prepared are they for medical device exploits held by governments to get stolen and dumped on WikiLeaks or Pastebin?” he said. “And are medical device vendors willing to push for properly cleared health agency officials to have a seat at the VEP [Vulnerabilities Equities Process] table so patient safety is a consideration with U.S. government-held vulnerabilities for strategic cyber purposes?”
Overall, Sipple said, he thinks things are moving in the right direction. “The new things coming online are better,” he said. “All the big companies really are investing in it. They have huge groups of people working on it.”
He said healthcare institutions are becoming more demanding of vendors as well. “Mayo Clinic has integrated cyber security into their procurement process,” he said. “They require a pen [penetration] test. They understand that a lot of the devices are going to have problems, so they require a plan to fix things.”
In addition, “they are pushing back with tons of legal language” that puts liability on vendors for faults in products that cause bad outcomes.
“And the FDA has been more aggressive recently,” he said, noting that the agency forced St. Jude Medical last year to recall implantable cardioverter defibrillators (ICD) and cardiac resynchronization therapy defibrillators (CRT-D) owing to faulty batteries.
That was, of course, a safety, not cyber security, problem. But Sipple said that these days, vendors “will not get approval for a new device if they don’t have cyber security as part of it.”


Pingback: Episode 100: Estonia's Former CIO talks about engineering a secure electronic vote | The Security Ledger
Pingback: Podcast Episode 111: Click Here to Kill Everybody and CyberSN on Why Security Talent Walks | The Security Ledger