BitDefender has identified a new fast-spreading IoT botnet called Hide and Seek that has the potential to perform information theft for espionage or extortion.
Bitdefender security researchers have spotted a fast-spreading, shape-shifting new botnet that can hack IoT devices and potentially perform widespread information theft for espionage or extortion, they said Wednesday.
Bitdefender’s IoT honeypot system intercepted the botnet—dubbed Hide and Seek (HNS)—after detecting attempted dictionary attacks attempting to guess credentials on exposed Telnet services, Bitdefender senior e-threat analyst Bogdan Botezatu revealed in a blog post on Wednesday. The post contains detailed examples of how HNS behaves. That is a similar approach to the one used by the Mirai IoT botnet.
The botnet was named “Hide and Seek: because researchers first identified it on Jan. 10 and then watched as it faded away, re-emerging on Jan. 20 “in a significantly improved form,” he said.
While IoT botnets have been around for years and mainly used for DDoS attacks, IoT botnets that have appeared in recent years like Mirai, Reaper and Hajime show the increasing sophistication of and risk from these bots.
HNS also is evidence of this, Botezatu warned. “The discoveries made during the investigation of the Hide and Seek bot reveal greater levels of complexity and novel capabilities such as information theft–potentially suitable for espionage or extortion,” he wrote. “It is also worth noting that the botnet is undergoing constant redesign and rapid expansion.”
HNS also is like Hajime in that it has a decentralized, peer-to-peer (P2P) architecture—only the second known IoT botnet date to have such a structure. However while Hajime’s P2P functionality was based on the BitTorrent protocol, HNS’ is custom-made, according to BitDefender.
The bot features a UDP communication mechanism that opens a random port on the victim, and adds firewall rules to allow inbound traffic for the port. It then listens for connections on the open port and only accepts specific commands, which Botezatu outlined in his blog post.
“Our initial look at the sample revealed an elliptic curve key inside the file that is used to authenticate the command, which updates the memory zone where configuration settings are stored, to prevent infiltration or poisoning attempts against the botnet,” he wrote.
The first samples of the bot identified on Jan. 10 revolved around IP cameras manufactured by a Korean company, Botezatu said.
“These devices seemed to play a major role in the botnet as, out of the 12 IP addresses hardcoded in the sample, 10 used to belong to Focus H&S devices,” he wrote. The new version of the bot that remerged 10 days later dropped the hardcoded IPs.
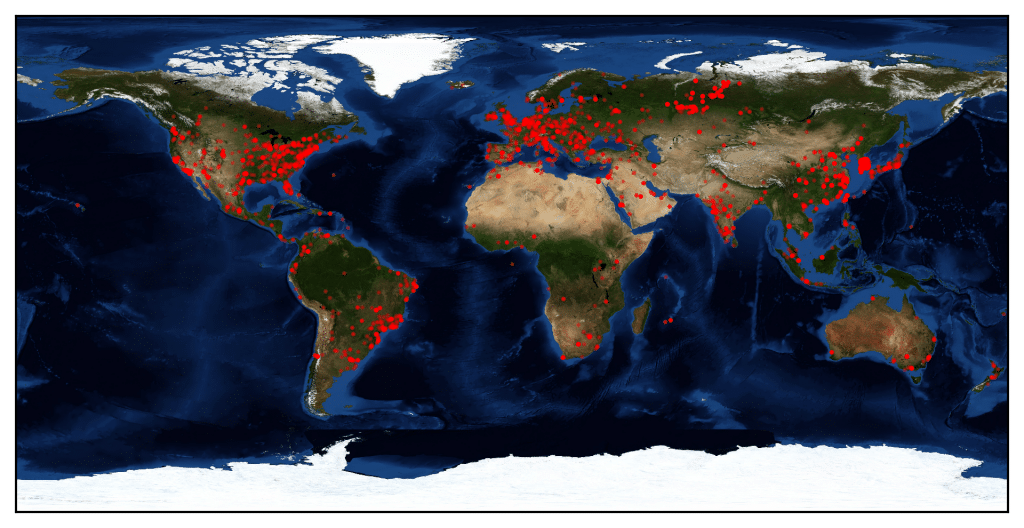
At the time of Botezatu’s blog post, the HNS bot—which started as a 12-device network—had spread to 14,000 devices geographically worldwide in multiple continents, including North America, South America, Europe, Asia, Africa and Australia.
The bot works by using a worm-like spreading mechanism that randomly generates a list of IP addresses to get potential targets. It then initiates a raw socket SYN connection to each host in the list and continues communication with those that answer the request on specific destination ports, such 23 2323, 80, 8080 etc.
Once the bot establishes a connection, it looks for a specific banner (i.e., “buildroot login:”) presented by the victim, Botezatu said. If it gets this login banner, it attempts to log in with a set of predefined credentials. If that fails, the botnet attempts a dictionary attack using a hardcoded list of administrative user names and passwords.
“Once a session is established with a new victim, the sample will run through a ‘state machine’ to properly identify the target device and select the most suitable compromise method,” he wrote.
For example, if the victim has the same LAN as the bot, the bot sets up TFTP server to allow the victim to download the sample from the bot, Botezatu explained. If the victim is located on the Internet, the bot will attempt a specific remote payload delivery method to get the victim to download and run the malware sample.
The exploitation techniques the HNS bot uses are preconfigured and located in a memory location that it digitally signs to prevent tampering, Botezatu said. This list can be updated remotely and propagated among infected hosts.
Some good news for devices affected is that like other IoT bots, HNS can’t achieve persistence, so rebooting cleans the compromised device. Still, its ability to spread and redesign itself rapidly is yet another warning for designers of IoT systems, proving again that the next-level security demands of the new interconnected-device paradigm are nowhere close to being met.

Pingback: Episode 82: the skinny on the Autosploit IoT hacking tool and a GDPR update from the front lines | The Security Ledger
Pingback: Black Box Device Research reveals Pitiful State of Internet of Things Security | The Security Ledger
I have noticed you don’t monetize your site, don’t waste your traffic,
you can earn extra bucks every month because you’ve got high quality content.
If you want to know how to make extra $$$, search for:
Ercannou’s essential adsense alternative