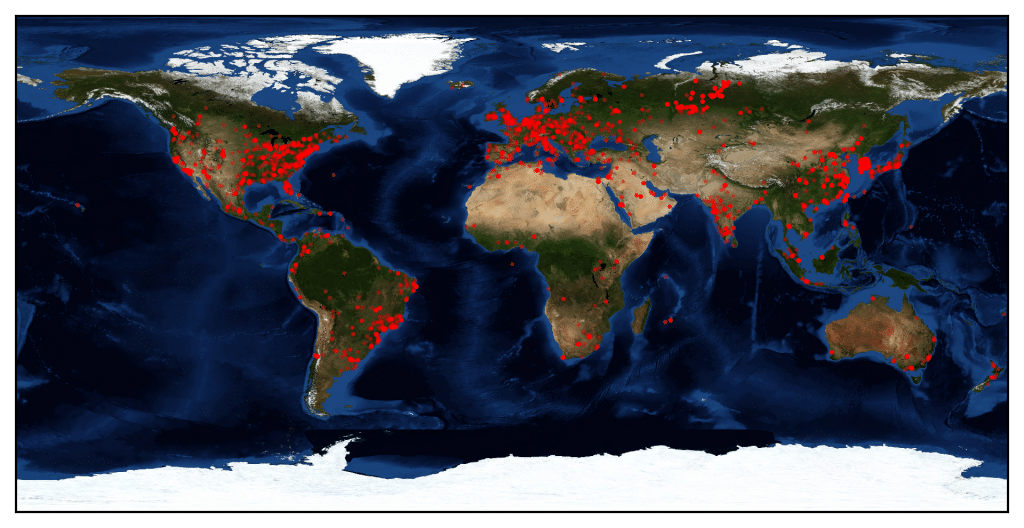
Microsoft’s worm-friendly Bluekeep flaw affects medical devices and other Internet of Things endpoints, security experts are warning.
Tag: IOT
Report: Companies Still Grappling with IoT Security
Data breaches relating to unsecured Internet of Things devices have jumped by more than 10 percent since 2017, suggesting security efforts aren’t keeping pace with the growth of the Internet of Things, a new study finds.
Report: IoT Still Wildly Insecure as New ‘Credential Compromise’ Threat Emerges
The new year isn’t bringing good news about Internet of Things security, as a new report sheds light on a flaw that allows bad actors to take unauthorized control of applications used by the IoT devices.
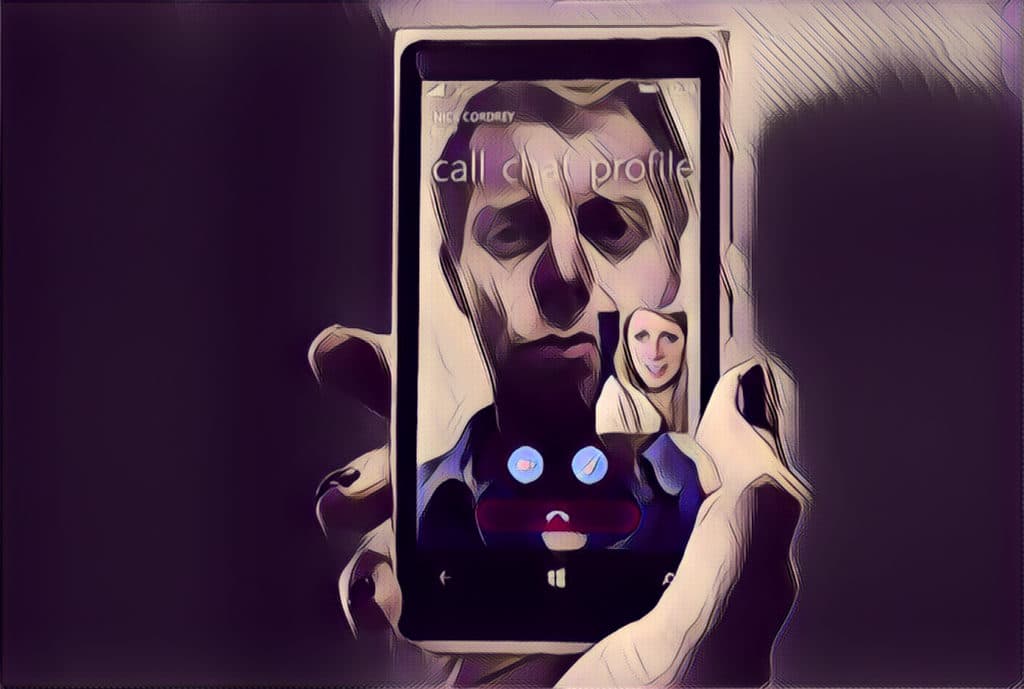
Single Photo uniquely identifies Smartphone that took it
Technology developed by researchers at the State University of New York can create a smartphone “fingerprint” from a single photo captured by the device. The technology may clear the way for a new identity verification system that can secure online transactions or protect smartphone owners from identity theft.
New Rapidly-Spreading Hide and Seek IoT Botnet Identified by Bitdefender
BitDefender has identified a new fast-spreading IoT botnet called Hide and Seek that has the potential to perform information theft for espionage or extortion.