
In-brief: Internet of Things devices are making their way onto enterprise networks, though technology professionals entrusted with managing those networks often do not realize it, a new survey finds.
Internet of Things devices are making their way onto enterprise networks, though technology professionals entrusted with managing those networks often do not realize it.
A survey of more than 350 information technology (IT) and networking professionals about the kinds of devices deployed on their network revealed that surveyed firms had an average of 9 devices deployed that fall under the “Internet of Things” umbrella. Still, organizations don’t consider them to be IoT endpoints and often lack tools and policies to monitor and secure the devices, according to ForeScout Technologies, a security firm that sponsored the survey.
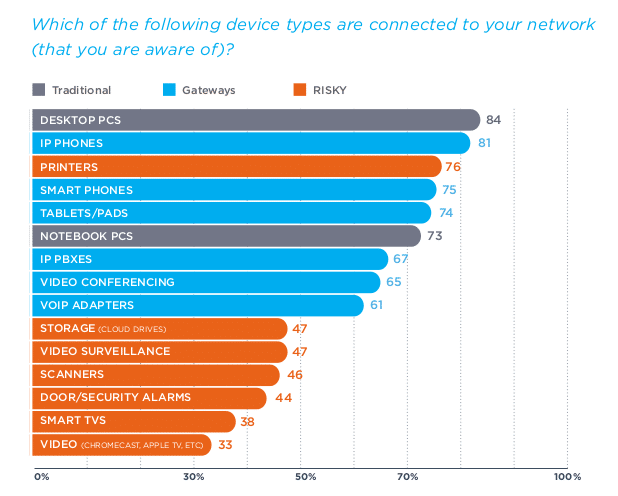
On average, respondents had at least nine out of 27 different types of IoT devices, including smart television sets, networked printers and scanners, video surveillance cameras and connected door and badging systems. That number was consistent across respondents – even those who claimed to have no IoT devices when initially asked.
Thirty percent of respondents said that their company failed to have a specific solution in place to secure IoT devices, and more than a quarter of those surveyed said they did not know if they have security policies on their devices.
Fragmentation within enterprise IT groups that separates operations from IT and the information security group is part of the problem of identifying and managing Internet of Things technologies, said Rob Greer, the Senior Vice President of Products at ForeScout.
Audio-visual systems, IP-based telephony, physical access systems and the like are often managed and provisioned by different groups than desktops, laptops and network access, he said. That kind of organizational obstacle can make it difficult for firms to wrap their arms around all the devices deployed in their IT environment.
Greer notes that there have already been high-profile security incidents that have exploited that gap. Among them: the hack of Target Stores point of sale network, which proceeded from a compromise of a third party firm that managed HVAC (environmental) systems in the company’s headquarters. “These systems are intelligent and are used for the purpose of automation, but nobody is really looking at them for vulnerabilities,” he said.
While the hype around “Internet of Things” as a buzz word may die down, Greer thinks the trends that have already been identified, including the transition to a more diverse and distributed endpoint environment, is inexorable.
As a result, organizations will need to invest in tools that both tell them what is connecting to their networks and what the “hygene of devices” is, he said. That, in turn, will require enterprises and other organizations to take more ownership of decisions affecting both IT and operations.
“There’s a lot of decentralized decisions made about different device types,” Greer said. “At big companies you tend to trust your HVAC vendor or your switch vendor,” he said. “We need to train people to ask more questions like ‘who owns that?'”
Beyond asking questions, companies also have to develop baselines for the behavior of a wider range of devices – from networked printers on down – to be able to spot when a device may have been compromised or be acting strangely. “Once you know what you have, you have to understand what normal is,” he said.
