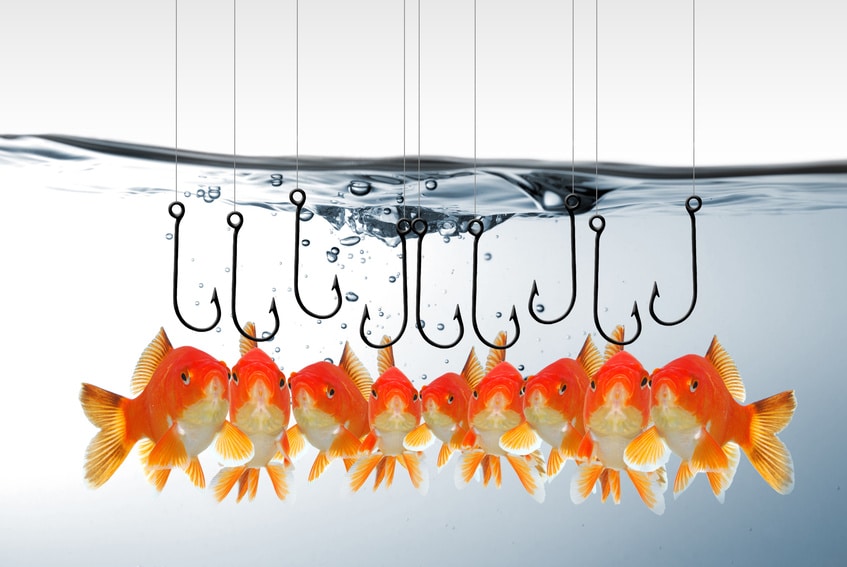
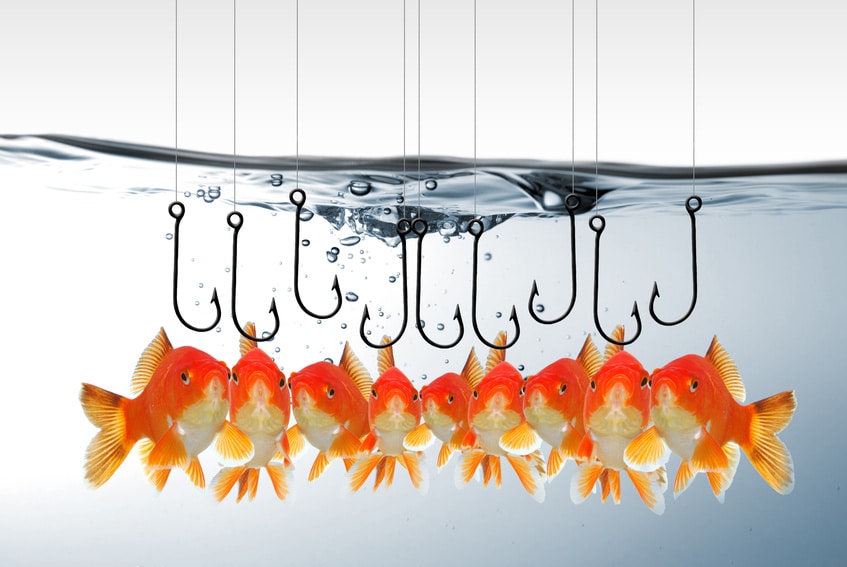
In-brief: Websense has uncovered a phishing scam that uses “urgent” e-mails from executives to fool employees into wiring money overseas.
Lots of studies have shown that assertiveness works in the professional sphere. It turns out to work pretty well for cyber criminals, also.
Websense Labs writes today about spear phishing attacks that rely on e-mail messages posing as urgent communications from senior officers to lower level employees. The messages demand that the employees wire funds to a destination account provided in the message.
The attack is low tech. First, the fraudsters register “typo squatting” domains that look like the target company’s domain, but are subtly different. They then set up e-mails at the typo squatted domain designed to mirror legitimate executive email accounts.
The attacks rely on the similarities of the domains and often extensive knowledge of key players within the company, creating e-mails that are highly convincing to recipients.
The other element of their attack is – simply – “obeisance,” Websense notes. “When the CEO or CFO tells you to do something, you do it.”
Emails sent to lower level employees from executives were brief and urgent (limiting the likelihood that the phishers would trip up on language). The message also demanded updates on the progress of the transfer, making the request seem more authentic.
A sample e-mail reads simply “Process a wire of (amount) to the attached account information.” It includes a presumed email thread with another executive regarding the transfer.
“In this instance, phishers were trying to play on the similarity of domains, but they also preyed on the eagerness of most employees to please,” Websense said.
Websense notes the similarities between the technique used in the latest phishing attack and the grain trading firm Scoular in June, 2014. That company was tricked into wiring some $17 million to a bank in China, with employees believing they were acting on the wishes of executives who had communicated through e-mail.
Websense said companies that fall for such scams often lack strong internal controls and FBI is still attempting to recover the $17 million lost in that case, which also involved legitimate employee names with fake email aliases.
For

Pingback: Angry Boss Phishing Emails Prompt Fraudulent Wire Transfers | I World New