Software vulnerabilities in web sites operated by John Deere could allow a remote attacker to harvest information on the company’s customers including their names, physical addresses and the equipment they own. The revelation suggests the U.S. agriculture sector is woefully unprepared for disruptive cyber attacks, experts warn.
Tag: APT
Experts warn COVID-19 raises Stakes for Nation State Info-Ops Targeting US
The Covid-19 coronavirus may be novel, but security experts say that the cyber and disinformation strategies capitalizing on the crisis are not.
Episode 154: Richard Clarke on Defending the Fifth Domain
The Pentagon calls cyberspace “the fifth domain” of conflict. But what does that mean? And how do you defend a human-made space that’s everywhere and nowhere? In this episode of the podcast, Richard Clarke joins us to discuss his new book, The Fifth Domain: Defending Our Country, Our Companies, and Ourselves in the Age of Cyber Threats.
Ahead of Black Hat: Fear and Pessimism in Las Vegas
A survey of security professionals who have attended Black Hat reveals fears for From the 2020 Election, U.S. infrastructure
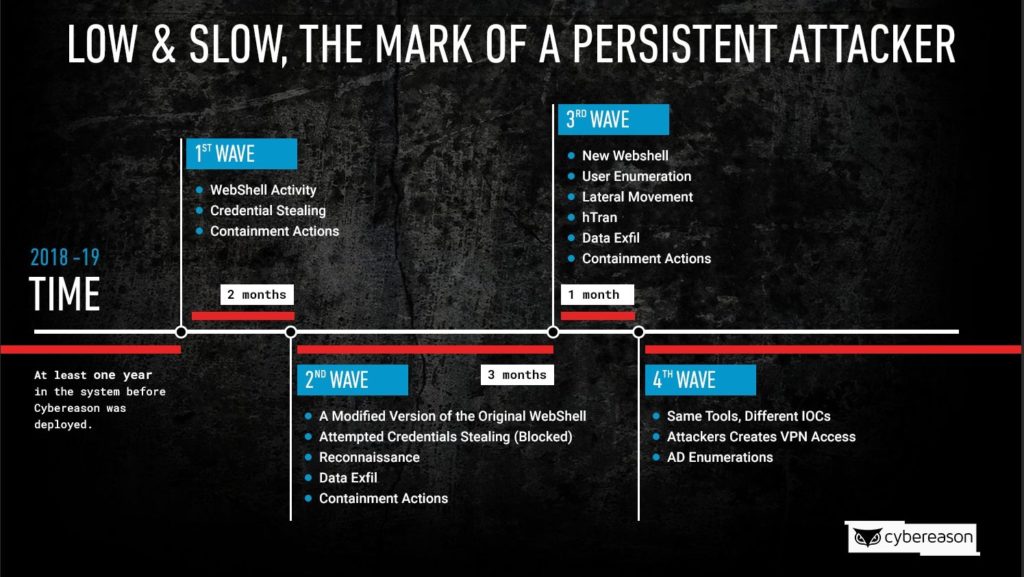
Firm Uncovers Major Cyber-Espionage Campaign Against Telcos
The security firm Cybereason has uncovered a persistent cyber espionage attack on telecommunications companies worldwide to steal data on high-profile users and then spy on them.