In-brief: A British researcher who became a hero after he stopped the WannaCry ransomware from spreading globally has been apprehended in Nevada and charged with distributing the Kronos banking trojan in the U.S. between July 2014 and July 2015.
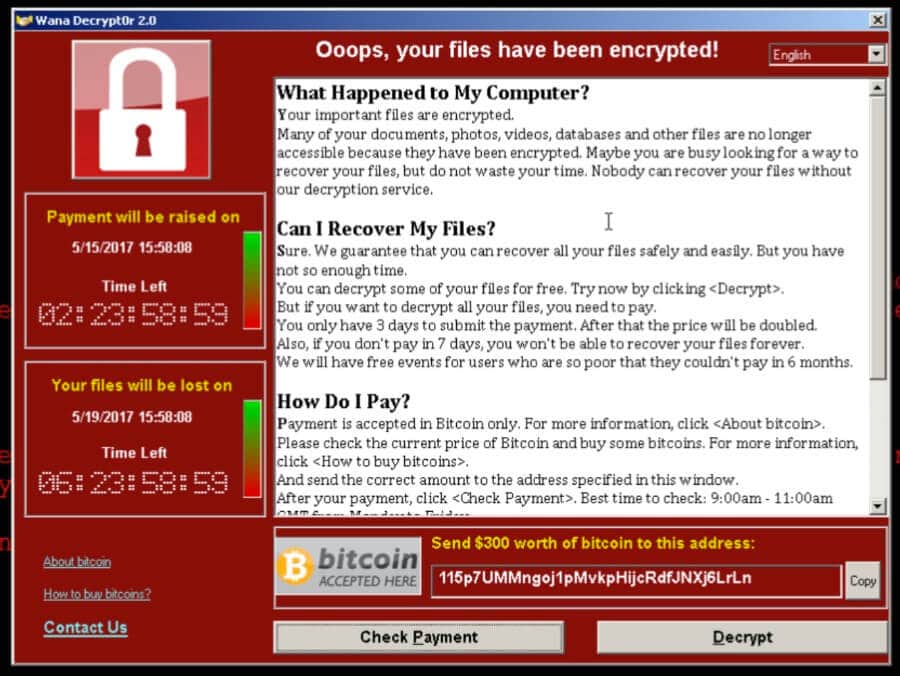
Wanna Cryptor
The WannaCry Missing: Federal Systems, Consumers
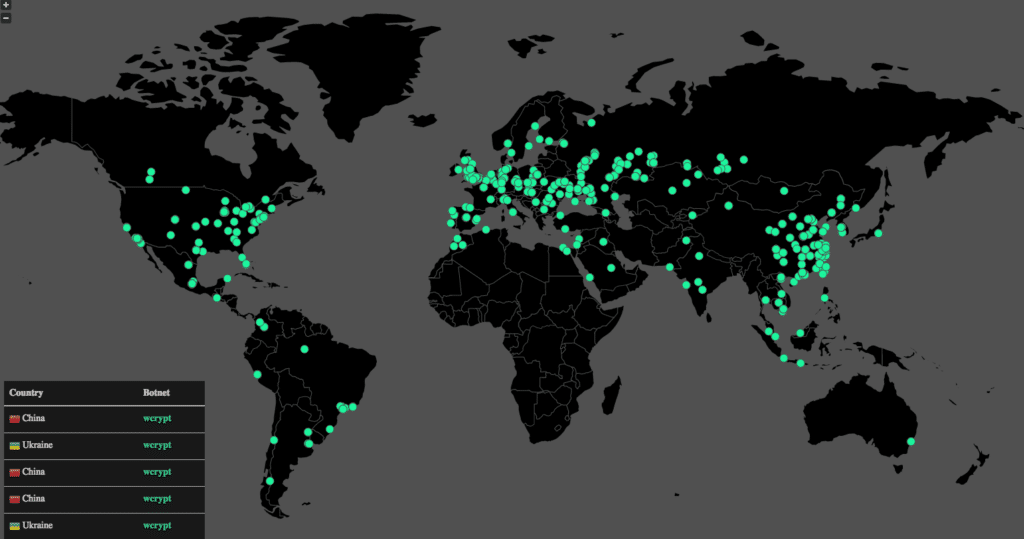
In-brief: One week after the WannaCry ransomware knocked out hospitals in the UK and subway fare systems in Germany, the malware is as notable for who it didn’t affect for who it did. Among those spared WannaCry’s wrath: federal IT systems in the U.S. as well as consumers. But why?
WannaCry: What’s in a name? Confusion | Digital Guardian
In-brief: focusing on WannaCry, the ransomware delivered in last week’s attacks, misses the point. Organizations weren’t done in by the shoddy malware, but by a class-A offensive cyber weapon known as EternalBlue. Editor’s Note: this blog is cross posted from Digital Guardian’s Data Insider blog.
Podcast: WannaCry: It’s The Exploits, Stupid and Parsing The Cyber Executive Order
In-brief: We speak with Sean Dillon of the firm RiskSense, who helped reverse engineer DoublePulsar and EternalBlue, the Windows exploit tools used to help spread the WannaCry ransomware. We also chat with John Dickson of The Denim Group about the impact of President Trump’s Cyber Executive Order.
Updated: Fatal Flaw Slows WannaCry Ransomware Spread, but Threats Remain
In-brief: A fatal flaw in its design slowed the spread of WannaCry, a virulent ransomware program that has infected more than 100,000 organizations and individuals globally.