Cisco’s Matt Olney, the Director of Talos Threat Intelligence and Interdiction and Craig Williams, the Talos Director of Outreach about the case against
Sandworm
Second Ukraine Power Outage Linked to Russian Hackers
In-brief: A cyber attack in December was responsible for a power outage in Ukraine – almost a year to the day after a similar attack in 2015, new research shows.
Surprise: Branding a Bug is just as Hard as Branding Anything Else!
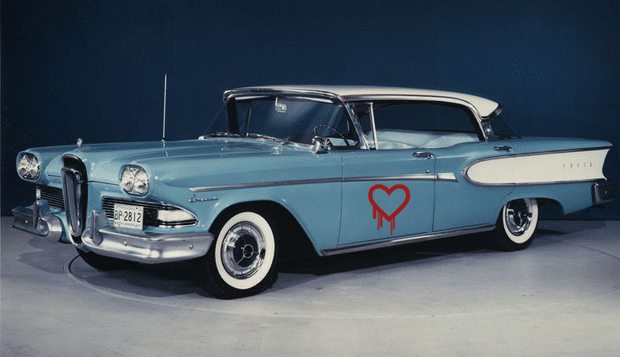
ZDNet’s @violetblue has a nice piece on the new fad for naming vulnerabilities – seen most recently with the OpenSSL Heartbleed vulnerability and the “Shellshock” vulnerability in Linux’s common BASH utility. As Blue notes, the desire to “brand” bugs “changes the way we talk about security” – in part by giving complex, technical flaws down a common referent. But does giving a bug a logo make it frivolous? As she notes: the penchant for naming vulnerabilities may stem not from a desire to trivialize them – but a very practical response to the need to keep track of so many security holes in software. Regardless, Heartbleed – and the marketing by the firm Codenomicon that surrounde it – was the bug that launched a thousand ships, including Shellshock, Sandworm, and more. Read more coverage of Heartbleed here. But, as with . As security research and incident response are becoming more lucrative, expect the masonry […]
Malware Campaign Against Industrial Systems Almost 3 Years Old
The U.S. Government’s Industrial Control System CERT (ICS-CERT) said on Thursday that a campaign targeting industrial control system (ICS) software began in January, 2012 and targeted industrial systems that were directly connected to the public Internet. ICS-CERT said in an alert published on Wednesday that “HMI” (or Human-Machine Interfaces) products from vendors including GE, Advantech/Broadwin and Siemens may have been infected with variants of the BlackEnergy malware since January, 2012. Infected firms were running versions of the GE’s Cimplicity, Advantech/Broadwin’s WebAccess or Siemens’ WinCC with what ICS-CERT called a “direct Internet connection.” In some cases, as with the GE Cimplicity attacks, hackers exploited a known vulnerability in the Cimplicity software to gain access. In others (as with WebAccess and WinCC) the method by which the software was compromised isn’t known, ICS-CERT said. CERT said it hasn’t documented any cases of control processes being modified by the malware. However, BlackEnergy is typically used […]