Researchers at the security firm CheckPoint are warning that code to attack a vulnerability in Huawei HG532 home routers has been leaked online and is linked to attacks by the Satori botnet.
Mirai
Research Finds Home Routers fill ranks of Fast Flux Botnets
Research from the firm Akamai finds cyber criminals are marrying vulnerable home routers to sophisticated “fast flux” command and control tools to create long-lived, cyber criminal infrastructure.
A Right to Repair the Internet of Things? Spear Phishing Detection and Nonstop Attacks on DVRs
In-brief: In the latest Security Ledger podcast we talk about pending right to repair laws and their impact on the Internet of Things. Also: Facebook’s Internet Defense Prize went to a better method for spear phishing detection. We talk to a member of the winning team. And, Johannes Ullrich of The Internet Storm Center joins us to talk about a study he did to measure the frequency of attacks on a common IoT device: digital video recorders.
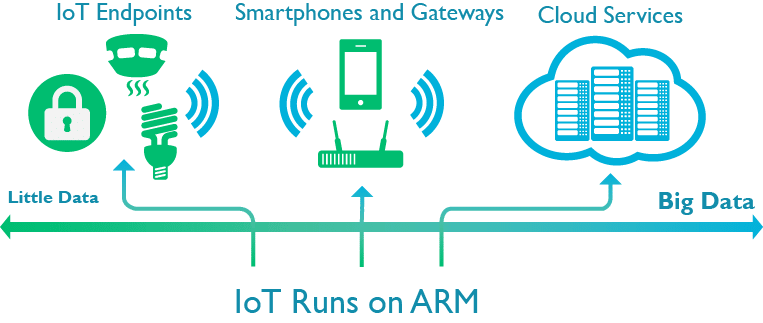
With an Eye on IoT Security ARM buys Simulity for $15m
In-brief: ARM’s purchase of Simulity adds the ability to do over the air updates to embedded SIM chips and highlights ARM’s efforts to build out security and management at IoT scale.
Identity at Scale: how the Internet of Things will Revolutionize Online Identity
In-brief: Far from ‘breaking’ the public key encryption (PKI) model, the Internet of Things is poised to turbocharge PKI adoption and revolutionize online identity, DigiCert CTO Dan Timpson writes.