In-brief: Experts from two security firms are warning that a newly discovered piece of malware dubbed Crash Override is designed to shut down and even damage electrical substations and other components of the electrical grid.
BlackEnergy
Antivirus Players Vying for Industrial Control Systems Business
In-brief: news from incumbent endpoint protection firms Symantec and Kaspersky Lab that they are ramping up efforts to sell their wares into industrial control systems environments suggests that the death of anti virus may have been greatly exaggerated.
Banking Trojans Pose as SCADA Software to Infect Manufacturers
Dark Reading’s Kelly Higgins has a report about a discovery by a security researcher who has identified a worrying new trend: banking malware that is posing as legitimate ICS software updates and files in order to compromise systems that run manufacturing plants and other facilities. Higgins writes about research by Kyle Wilhoit, senior threat researcher with Trend Micro. Wilhoit claims to have found 13 different crimeware variants disguised as SCADA and industrial control system (ICS) software. The malware posed as human machine interface (HMI) products, including Siemens’ Simatic WinCC, GE’s Cimplicity, and as device drivers by Advantech. [Read more Security Ledger coverage of threats to SCADA and industrial control systems here.]The attacks appear to be coming from traditional cybercriminals rather than nation-state attackers. The motive, Wilhoit theorizes, is to make money, possibly by harvesting banking credentials or other financial information. Malicious software that can operate in industrial environments and critical infrastructure settings is an […]
In Cyberwar, US Grid is a Prime Target | CSMonitor.com
The Christian Science Monitor is running a story I wrote this week on the security of the electric grid. In the piece, I take a look at whether the electric industry is soft-pedaling cyber risk. From the piece: “For all the huffing and puffing in Washington D.C. policy circles about the hack of Sony Pictures being an act of “cyber war,” for security experts who have been working within the power sector, however, the dire warnings are not news. They would not have been news last year, or the year before. In fact, (NSA Chief Mike) Rogers’ dim assessment of the US power sector’s readiness to face and withstand a cyberattack has been shared and articulated within the power industry for seven years. “Why is it that the US power grid in 2014 is not better prepared to keep nation-state hackers at bay, or to withstand a critical cyberattack? Some of the […]
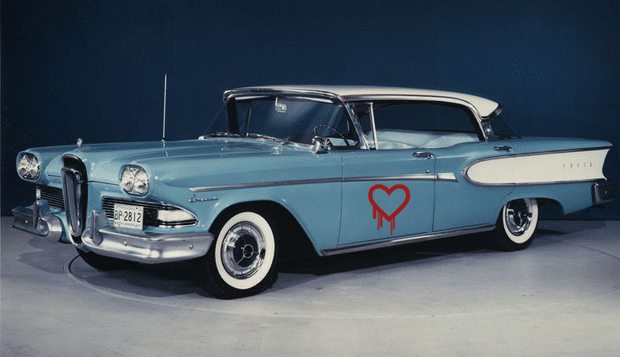
Surprise: Branding a Bug is just as Hard as Branding Anything Else!
ZDNet’s @violetblue has a nice piece on the new fad for naming vulnerabilities – seen most recently with the OpenSSL Heartbleed vulnerability and the “Shellshock” vulnerability in Linux’s common BASH utility. As Blue notes, the desire to “brand” bugs “changes the way we talk about security” – in part by giving complex, technical flaws down a common referent. But does giving a bug a logo make it frivolous? As she notes: the penchant for naming vulnerabilities may stem not from a desire to trivialize them – but a very practical response to the need to keep track of so many security holes in software. Regardless, Heartbleed – and the marketing by the firm Codenomicon that surrounde it – was the bug that launched a thousand ships, including Shellshock, Sandworm, and more. Read more coverage of Heartbleed here. But, as with . As security research and incident response are becoming more lucrative, expect the masonry […]