In-brief: Experts on the security of the Internet of Things warned that lax security and privacy protections are rampant in connected home products, but consumers have no way of knowing whether the products they buy are easy targets for hackers.
whitelisting
Dusting For Malware’s Bloody Prints
Malicious software is nothing new. Computer viruses and worms have been around for decades, as have most other families of malware like remote access tools (RATs) and key loggers. But all our experience with malware hasn’t made the job of knowing when our organization has been hit by it any easier. In fact, recent news stories about breaches at Home Depot, Target, Staples and other organizations makes it clear that even sophisticated and wealthy corporations can easily overlook both the initial compromise and endemic malware infections – and at great cost. That may be why phrases like “dwell time” or “time to discovery” seem to pop up again and again in discussions of breach response. There’s no longer any shame in getting “popped.” The shame is in not knowing that it happened. Greg Hoglund says he has a fix for that latter problem. His new company, Outlier Security, isn’t “next generation […]
Cisco Updates ASA Security Appliance To Tackle Zero Day Malware
We’re used to writing about all the things that are changing in the security field: the onslaught of mobile devices and connected ‘stuff,’ the advent of ‘advanced’ and ‘persistent’ adversaries, the destruction of the network perimeter. But all this talk about change can obscure the fact that so much has not changed. Companies still maintain perimeters, after all, and they rely on nuts-and-bolts technologies to defend them. But these days, those products need to do more – especially in the area of ‘advanced threats’ that are likely to slip past traditional antivirus and IDS products. Enter Cisco Systems, which on Tuesday announced a new version of its ‘next generation firewall‘: the Cisco ASA (Adaptive Security Appliance) with FirePOWER Services. The appliance is the first to make full use of technology from Cisco’s acquisition of Sourcefire last year. Specifically, the latest ASA integrates Sourcefire’s Advanced Malware Protection (or AMP) technology, which gives the […]
Intel Promotes ‘Trustlets’ To Secure Embedded Devices
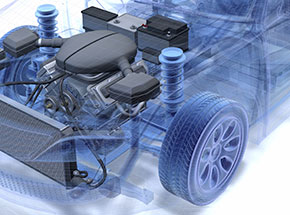
The integrity of data stored on- and transmitted between Internet-connected embedded devices is one of the biggest technical hurdles standing in the way of widespread adoption of Internet of Things technology. For one thing: embedded devices like wearable technology and “smart” infrastructure are often deployed on simple, inexpensive and resource constrained hardware. Unlike laptops or even smart phones, these are purpose-built devices that, by design, run for long periods in remote deployments, with extremely constrained features and low power consumption that is the result of limited processing power and memory. [Read Security Ledger’s coverage of connected vehicles.] Now Intel is promoting a platform that it says can bridge the gap and provide robust security features even for resource-constrained Internet of Things devices like wearables and connected vehicles. Back in April, the Intel Labs unveiled the results of joint research with Technische Universität Darmstadt in Germany. The researchers have developed a platform, dubbed TrustLite […]
Bit9 Defends Response To Hack, Promises More Details
The security firm Bit9 defended its response to a hack of its own network last week and promised to release more information to the public about what happened – just not quite yet. In a blog post dated Saturday, February 9, the company’s CTO, Harry Sverdlove, said that the company responded promptly to the attack and contacted customers as soon as it completed its own investigation of the hack, which allowed unknown assailants to sign malicious programs using a Bit9 code signing server. That malware was subsequently released on networks of Bit9 customers. Sverdlove said the company’s “first and foremost priority was to inform our customers quickly and directly,” and that the company did so “as soon as we understood and had mitigated the attack, and we were able to provide actionable advice.” The blog post by Sverdlove, just a day after a post by Bit9 CEO Patrick Morley that disclosed […]