In this episode of the podcast, host Paul Roberts speaks with Colin O’Flynn, CTO and founder of the firm NewAE about his work to patch shoddy software on his home’s electric oven – and the bigger questions about owners rights to fix, tinker with or replace the software that powers their connected stuff.
encryption
Spotlight: ShardSecure on Protecting Data At Rest Without Encryption
Host Paul Roberts speaks with Marc Blackmer of ShardSecure about that company’s new approach to protecting data at rest, which relies on fragmenting and scattering data to make it impossible to steal.
Spotlight Podcast: Dr. Zulfikar Ramzan on RSA’s Next Act: Security Start-Up
Thirty eight years after it was founded, RSA Security is embarking on what may be its most challenging journey yet: cybersecurity startup. In this Spotlight podcast we’re joined by RSA CTO Zulfikar Ramzan about the company’s path forward as an independent company.
How NIST Is Securing The Quantum Era
Quantum computers powerful enough to break the strongest classical encryption are at least a decade away, but the time to develop quantum safe encryption is now. In this opinion piece, Thomas Pöppelmann, a Senior Staff Engineer, Security Architecture and Cryptography Research at Infineon Technologies talks about the steps NIST and companies like Infineon are taking to make that happen.
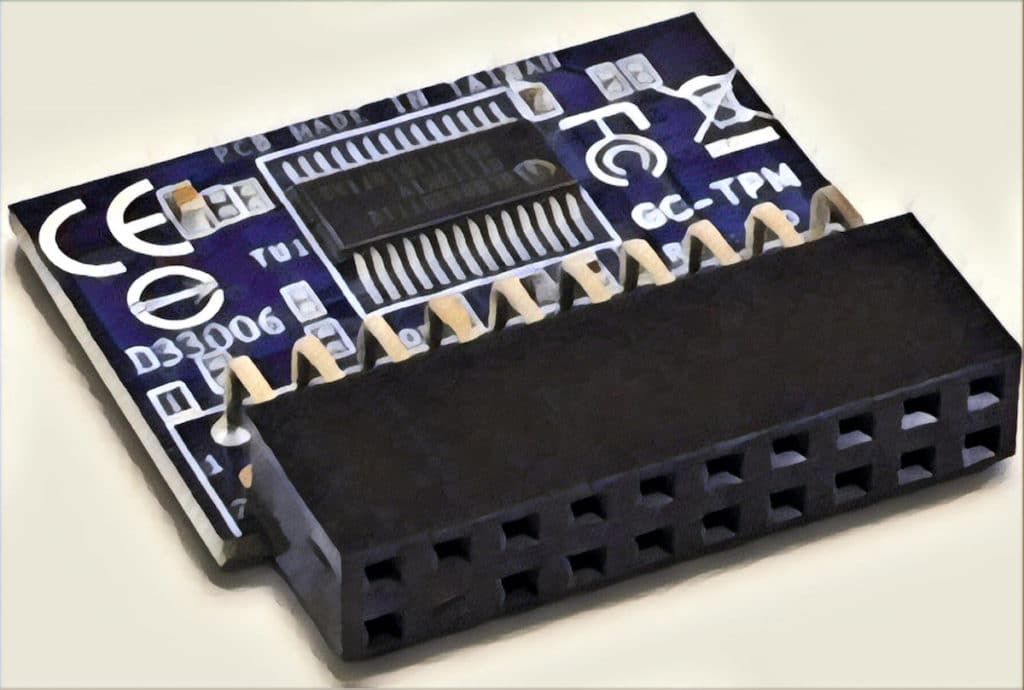
Spotlight Podcast: Two Decades On, Trusted Computing Group tackles IoT Insecurity
In this spotlight edition of the podcast, sponsored by Trusted Computing Group* Steve Hanna joins us to talk about TCG’s 20th anniversary and how the group is tooling up to confront the challenge of securing billions of Internet of Things devices.