Last week, home broadband router maker ASUS was the latest vendor to issue an emergency patch for a critical vulnerability in its products. This, after proof-of-concept exploit code was released for the so-called “Inforsvr” vulnerability that affects several ASUS home routers. That vulnerability -if left unpatched – would allow anyone with access to a home- or small business network that used an ASUS broadband router to, essentially, commandeer the device. The “infosvr” feature is typically used for device discovery by the ASUS Wireless Router Device Discovery Utility, but the service also allowed unauthenticated users to execute commands through it using the “root” permissions, according to researcher Friedrich Postelstorfer, who created a proof of concept exploit for the security hole and released it on January 4. The exploit code finally prompted a patch from ASUS on January 13. The company had spent months analyzing the issue and working on a fix. Patch aside, it has been a worrying month for the […]
reverse engineering
Unpatchable USB Malware Now Open Source | WIRED
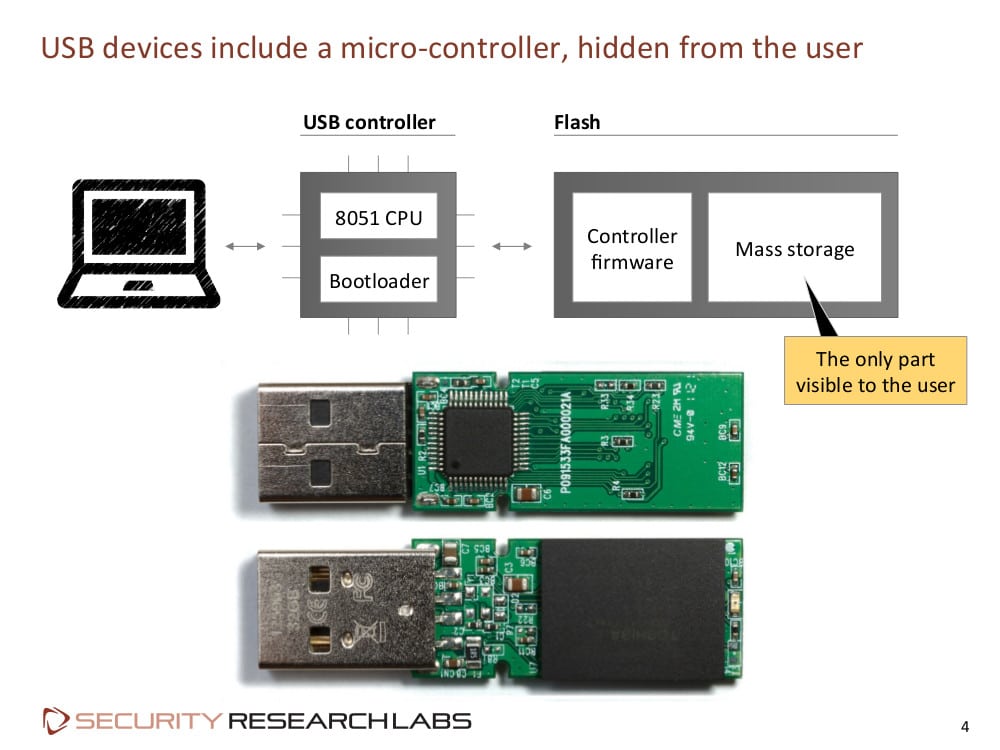
Andy Greenberg over at Wired has an interesting piece of news coming out of last week’s Derbycon hacker conference in Louisville, Kentucky. According to Greenberg and Wired, researchers Adam Caudill and Brandon Wilson showed off their own version of Karsten Nohl and Jakob Lell’s BadUSB malware, and that they’d released the code on Github. Their presentation raises the stakes for USB manufacturers to fix the BadUSB problem or leave hundreds of millions of users vulnerable, Greenberg writes. At a presentation at the Black Hat Briefings in August, Nohl and Lell, both of Security Research Labs (SRLabs), showed how the controller chips inside common USB devices can be reprogrammed, allowing USB peripherals to impersonate other kinds of devices. Among other things, Nohl demonstrated how a BadUSB infected device could emulate a USB keyboard, issuing commands to a connected machine using the permissions of the logged-in user. Alternatively, an infected USB could spoof a […]
Remote Car Hacks Depend On The Internal Design, Say Researchers
When purchasing your next car, you face many options. You want a good price, but also good gas mileage and perhaps an entertainment system for the kids in back. But for Dr. Charlie Miller, Twitter, and Chris Valasek, director of vehicle security research at I/OActive, the main criteria is whether or not the car is a likely candidate to be hacked. In particular they said they were interested in cars that would be more susceptible to remote hacking. Work done previously by Professor Stefan Savage along with graduate students from the University of Santa Barbara and the University of Washington used the Onboard Diagnostic port to control a car. Last year Miller and Valasek used internal wiring to gain control of their test cars. This year the pair said they wanted to take a step back and look at how cars in general communicate internally as a predictor of hacking […]
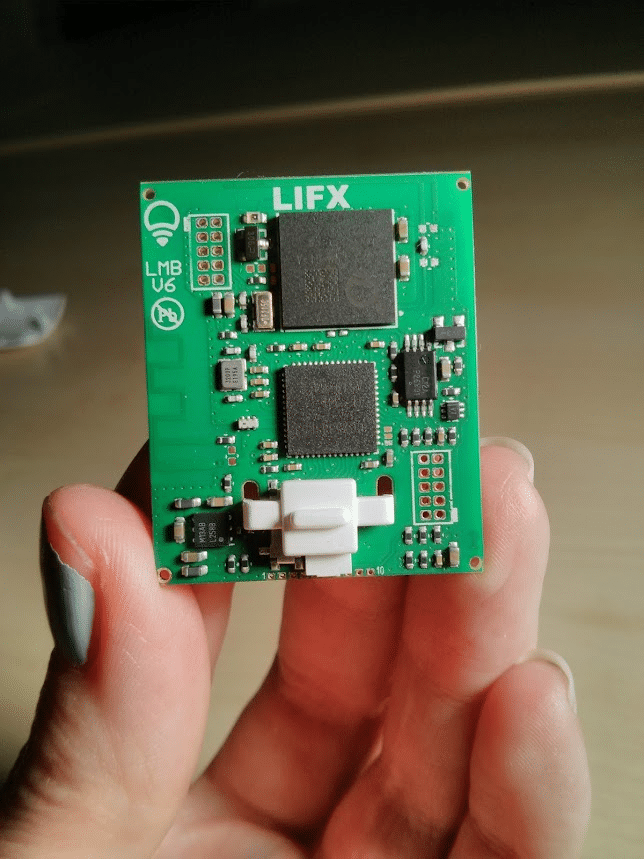
That LIFX Smart Lightbulb Hack Wasn’t Easy
If you’ve been following your Internet of Things security news, you probably read about the latest hack of a consumer-oriented ‘smart home’ device: Context Information Security’s analysis of security holes in LIFX-brand smart light bulbs. The top line on this is scary enough. As The Register reported: researchers at Context discovered that, by gaining access to a “master bulb” in LIFX deployments, they could control all connected lightbulbs and expose user network configurations. That’s scary – and recalls research on hacking Philips HUE light bulbs that was published last year. But read down in the Context research and you’ll realize that, while the LIFX technology wasn’t perfect, the job of hacking the technology wasn’t child’s play, either. LIFX connected its smart bulbs using a 6LoWPAN-based mesh network. The company made the mistake of transmitting most bulb-bulb communications in the clear, which made analyzing traffic sent between master- and slave bulbs easy. Context researchers found […]
Perverse Security Incentives Abound In Mobile App Space
Security problems abound in the mobile device space – and many of them have been well documented here and elsewhere. While mobile operating systems like Android and iOS are generally more secure than their desktop predecessors, mobile applications have become a major source of woe for mobile device owners and platform vendors. To date, many of the mobile malware outbreaks have come by way of loosely monitored mobile application stores (mostly in Eastern Europe and Russia). More recently, malicious mobile ad networks have also become a way to pull powerful mobile devices into botnets and other malicious online schemes. But my guests on the latest Security Ledger podcast point out that mobile application threats are poised to affect much more than just mobile phone owners. Jon Oberheide, the CTO of DUO Security and Zach Lanier, a researcher at DUO, note that mobile OS platforms like Android are making the leap […]