Though they are some of the oldest cyber attacks, Distributed Denial of Service (DDoS) attacks show no signs of going away, with an increase in the number, scope and sophistication of DDoS attacks in the past year, according to a recent report by cloud-delivery platform provider Akamai Technology.
hosting
Past and Future Risks Bedevil Security on Internet of Things
In-brief: Efforts to secure the Internet of Things will be challenged both by a backlog of old software and hardware, and by the rapid pace of technology evolution, experts warned at the recent Security of Things Forum in Cambridge, MA.
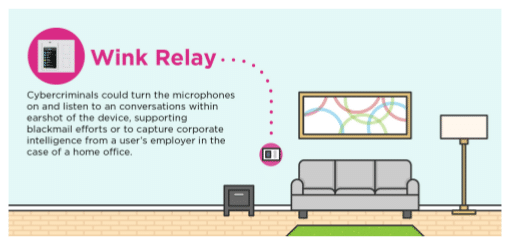
Research: IoT Hubs Expose Connected Homes to Hackers
In-brief: A study of common connected home gateways finds lax security that could expose consumers to snooping or even malicious attacks, according to the application security firm Veracode.
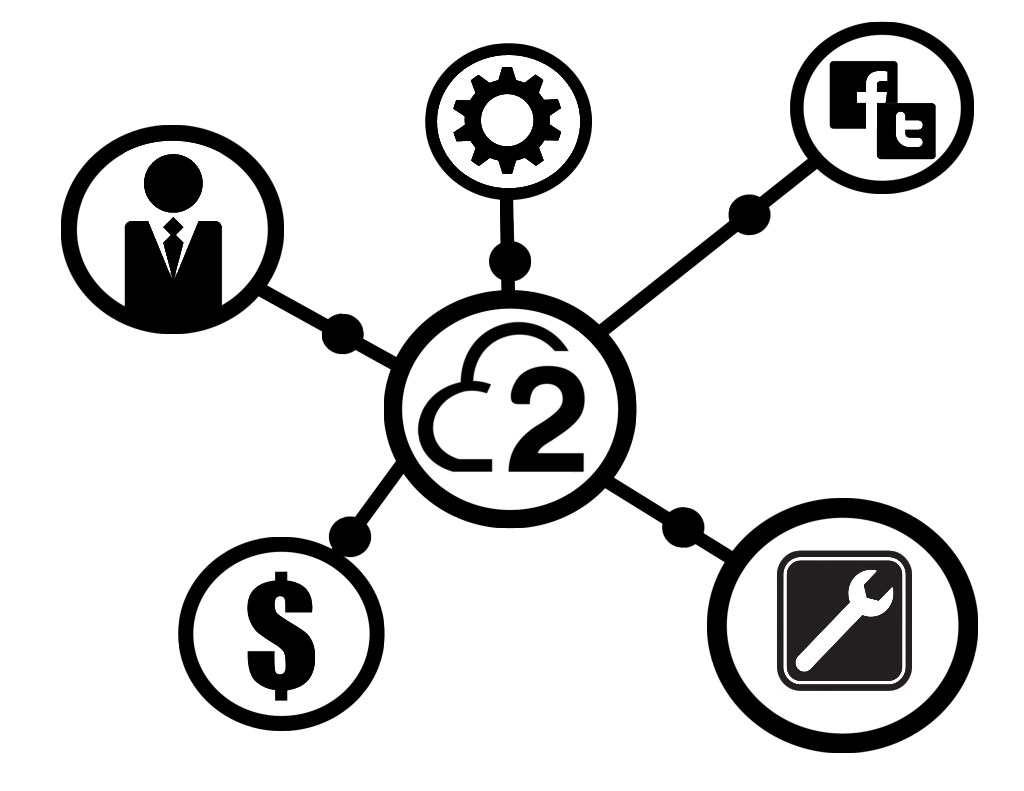
Amazon’s Springs for IoT Telemetry Startup 2lemetry
In-brief: 2lemetry, a Denver, Colorado-based startup that manages data from Internet connected devices said last week that it had been acquired by cloud giant Amazon.com.
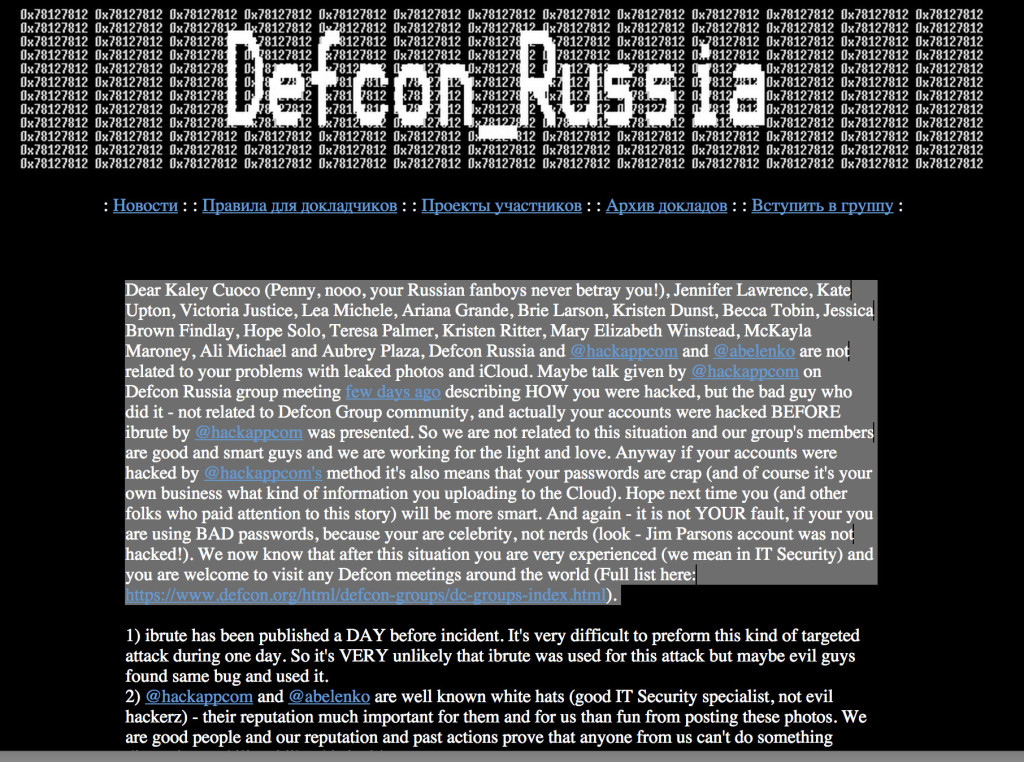
Hack Tool Authors Deny Link To Celeb Photo Leaks
With some of Hollywood’s biggest stars issuing statements on Monday condemning the leak of personal photographs online, attention has turned to identifying the source of the leaks. But more than 24 hours after the photos appeared, there are more questions than answers about its source. Early attention has focused on an automated tool that exploited an apparent vulnerability in Apple’s FindMyiPhone feature. But by Monday, there were denials from the makers of that tool that it played any role in the massive privacy breach that saw photos of A-list celebrities like Jennifer Lawrence, Kate Upton and others leaked online. Within hours of the photos’ appearance on the image sharing site 4chan, attention shifted to the cause of the leak and the coincidence of the leaked photos with the publication of iBrute, a simple tool available on GitHub in recent days. According to this published report by Owen Williams over at TheNextWeb, the […]