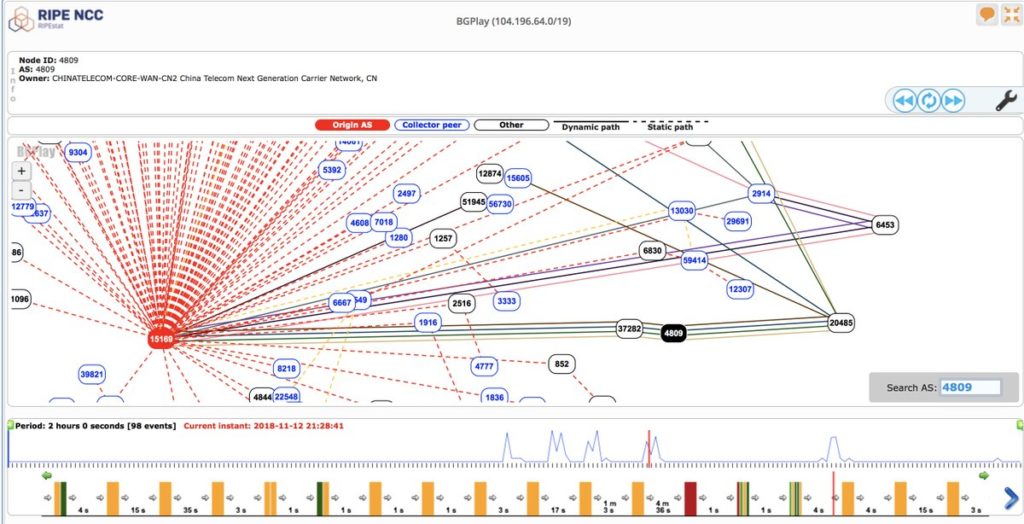
A small Nigerian Internet service provider (ISP) hijacked traffic meant for Google data centers on Monday, re-routing local traffic through China and Russia and making some hosted services temporarily unavailable for users.
news
Podcast Episode 115: Joe Grand on Unicorn Spotting and Bloomberg’s Supply Chain Story
In this week’s episode (#115), noted hardware enthusiast and hacker Joe Grand (aka “Kingpin”) told reporters from Bloomberg that finding an in-the-wild supply chain hack implanting malicious hardware on motherboards was akin to witnessing “a unicorn jumping over a rainbow.” They went with their story about just such an attack anyway. Joe joins us in the Security Ledger studios to talk about whether Bloomberg got it right. Also, Adam Meyers of Crowdstrike comes into the studio to talk about the U.S. Department of Justice indictment of seven Russian nationals. Adam talks about the hacks behind the charges and what comes next.
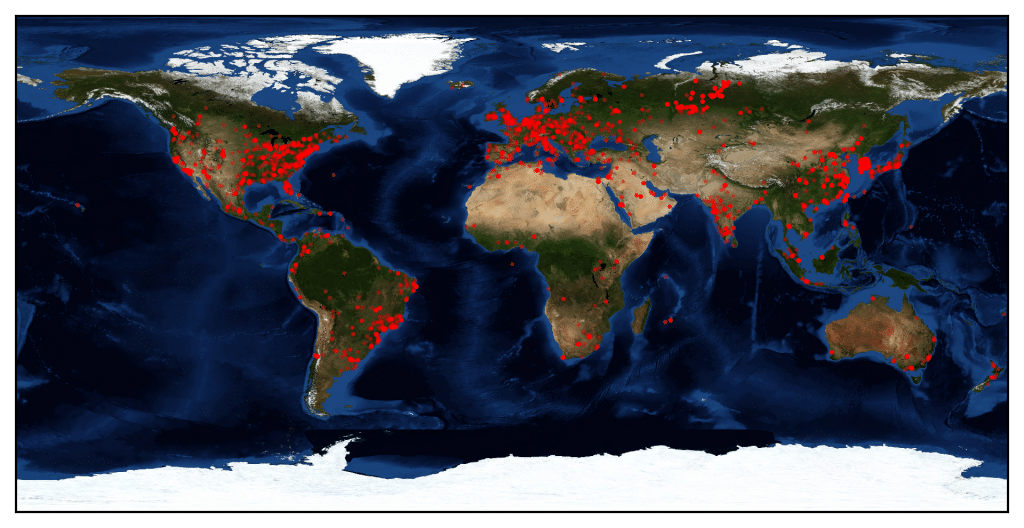
New Rapidly-Spreading Hide and Seek IoT Botnet Identified by Bitdefender
BitDefender has identified a new fast-spreading IoT botnet called Hide and Seek that has the potential to perform information theft for espionage or extortion.
Intel: Don’t Install Faulty Spectre, Meltdown Patches
In-brief: Intel has warned users not to install patches it released for the Spectre and Meltdown vulnerabilities in its processors, asking them to wait until it issues new software, which it’s working on now. Finding out your device has vulnerabilities is bad enough, but finding out the patched issued to fix them are “complete and utter garbage,” according to Linux creator Linus Torvalds, is even worse. This is what faced users of devices with Intel processors on Monday when Intel warned them not to install the patches the company already had released for the Spectre and Meltdown vulnerabilities. In a blog post, Navin Shenoy, Intel’s executive vice president and general manager of the Data Center Group, said the company had identified the root cause of a frequent-reboot problem that was affecting customers who’d installed its patches for these vulnerabilities. In the meantime, don’t install the patches nor tell customers or […]
WeChat set to become China’s official electronic ID | Security Affairs
Officials in the Nansha District of Guangzhou, China plan to allow citizens to use the WeChat social networking application as a form of official identification for access government and private sector services, Security Affairs reports.