In this episode of the podcast (#186) we do a deep dive on the new IoT cyber security rating system from Underwriters’ Lab. We talk with experts from GE about the process they used to obtain UL certification for a range of smart home appliances, managing device security over the decades and how a cyber security rating system may influence consumers’ behavior.
Internet of Things
Episode 184: Project BioMed – The Fight to Repair Medical Devices
In this episode of the podcast (#184) Kyle Wiens of iFixit joins us to talk about Project BioMed: an international, crowd-sourced effort to expedite repair of medical devices by making service and repair manuals available online. In our second segment, we speak with Jonathan Krones, one of an army of volunteer engineers, archivists and librarians who took on the task of cataloguing medical device repair information.
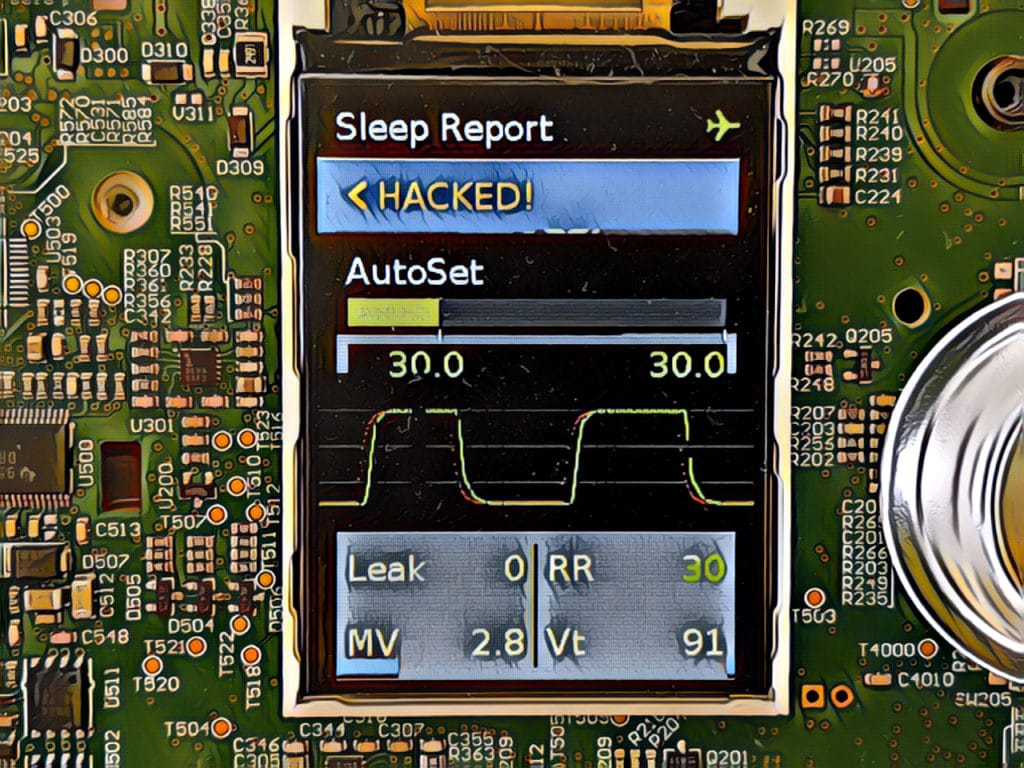
Episode 182: Hackers take Medical Devices ‘off label’ to Save Lives
In this episode of the podcast (#182) Trammell Hudson of Lower Layer Labs talks to us about Project Airbreak, his recent work to jailbreak a CPAP machines and how an NSA hacking tool helped make this inexpensive equipment usable as a makeshift respirator.
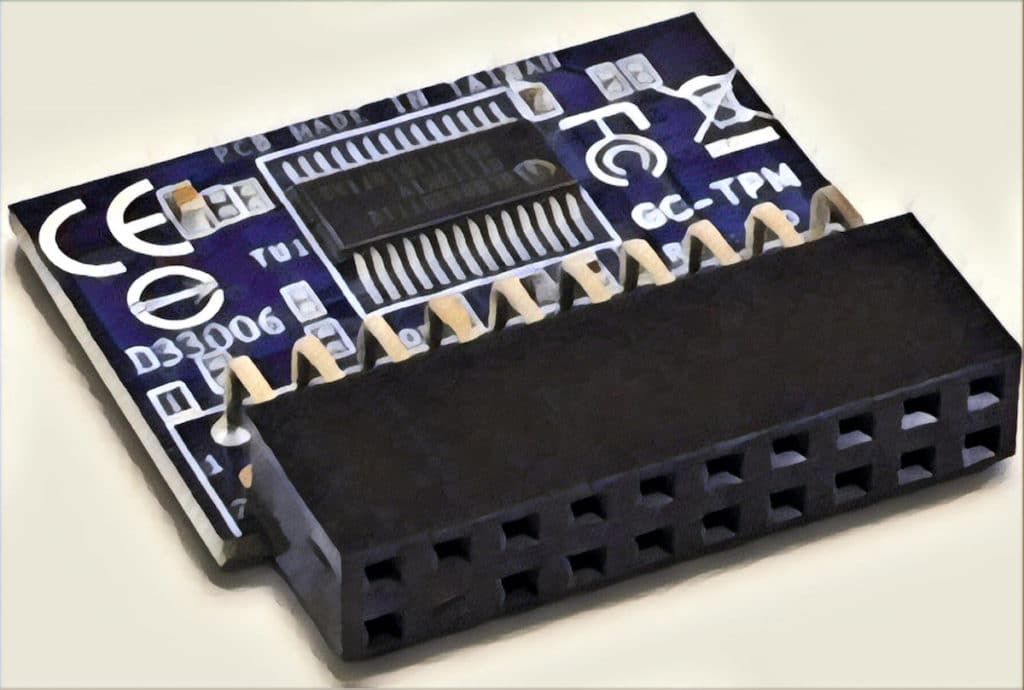
Spotlight Podcast: Building Resilience into the IoT with Rob Spiger
In this Spotlight edition of the Security Ledger Podcast, sponsored by Trusted Computing Group*: we’re joined by Rob Spiger, a principal security strategist at Microsoft and co-chair of the cyber resilient technologies working group at Trusted Computing Group. Rob talks to us about efforts to make more resilient connected devices and how the advent of the Internet of Things is changing TCG’s approach to building cyber resilient systems.
Spotlight Podcast: Two Decades On, Trusted Computing Group tackles IoT Insecurity
In this spotlight edition of the podcast, sponsored by Trusted Computing Group* Steve Hanna joins us to talk about TCG’s 20th anniversary and how the group is tooling up to confront the challenge of securing billions of Internet of Things devices.