A new joint FBI-DHS report dishes the dirt on recent sophisticated attacks targeting the US energy grid and critical infrastructure, saying third party firms and web sites to gain access to energy and other critical infrastructure networks. It also names a sophisticated hacking group believed to be linked to the government of Russia.
Energetic Bear
The Big Dark: Motive, not Means, is what holds back a Crippling Grid Hack
In-brief: A crippling cyber attack that could damage and destroy equipment needed to keep the lights on in major US cities is already possible. The only thing that’s lacking is a motive to carry out such an attack, according to our guest on this week’s podcast: Joe Weiss, a Managing Partner at Applied Control Solutions, LLC and a persistent, if lonely, voice calling for an overhaul of cyber security for the U.S. electric grid.
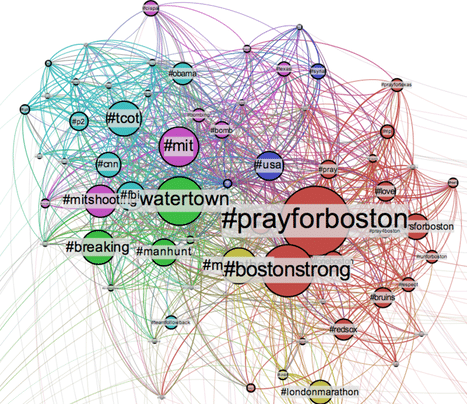
Podcast: Facebook Makes a Stand. But can Fake News be stopped?
In-brief: Facebook on Thursday unveiled a new initiative to stamp out disinformation and ‘fake news,’ but University of Washington researcher Kate Starbird, who is studying online ‘counter narratives’ says that conspiracy theories and ‘truthers’ may be here to stay.
Industrial Control Vendors Identified In Dragonfly Attack
Two of the three vendors who were victims of a targeted malware attack dubbed ‘Dragonfly’ by the security firm Symantec have been identified by industrial control system security experts. Writing on Tuesday, Dale Peterson of the firm Digitalbond identified the vendors as MB Connect Line, a German maker of industrial routers and remote access appliances and eWon, a Belgian firm that makes virtual private network (VPN) software that is used to access industrial control devices like programmable logic controllers. Peterson has also identified the third vendor, identified by F-Secure as a Swiss company, but told The Security Ledger that he cannot share the name of that firm. The three firms, which serve customers in industry, including owners of critical infrastructure, were the subject of a warning from the Department of Homeland Security. DHS’s ICS CERT, the Industrial Control Systems Computer Emergency Response Team, said it was alerted to compromises of the vendors’ by researchers […]