In this week’s Security Ledger Podcast (#88) we do a deep dive with researcher Vikram Thakur of the firm Symantec on “Dragonfly,” the Russian hacking group whose actions prompted the U.S. Department of Homeland Security and the FBI to issue a joint statement last week warning of intrusions into critical infrastructure in the US. Also: how do cyber criminals cash out all the loot they make from online scams? In our second segment we’ll talk to researcher Mike McGuire of the University of Surrey, who has been studying that question.
Symantec
Iran Taps Chafer APT Group amid Civil Aviation Crisis
Iran’s Chafer hacking group is targeting aviation repair and maintenance firms in an apparent effort to obtain information needed to shore up the safety of that country’s fleet of domestic aircraft, according to research by the firm Symantec.
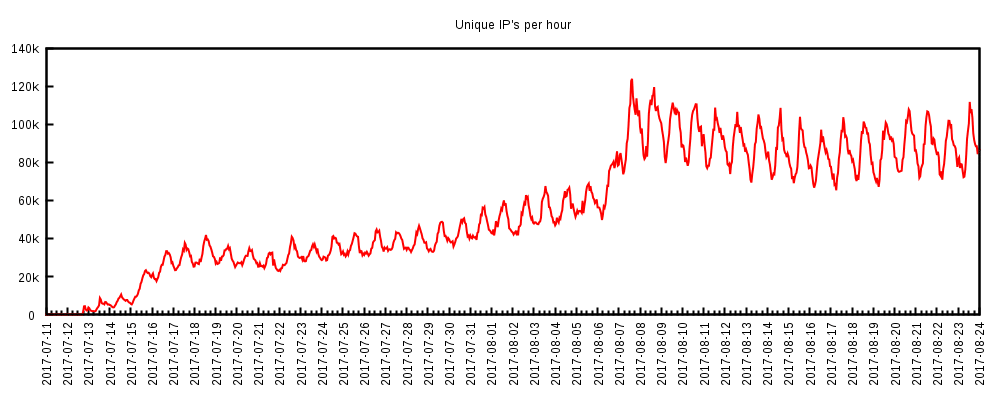
Mirai Victim Dyn Joins Team to Take Down Android Botnet WireX
In-brief: Managed DNS firm Dyn, a victim of the Mirai botnet, got its revenge: taking part in a coordinated takedown of WireX, a botnet of compromised Android devices, according to an announcement Monday.
Financial Malware, not Ransomware, drives most Cyber Crime
In-brief: data from the firm Symantec shows that financial malware targeting banks – not ransomware- is the most important and oft-used tool in the cyber criminal’s toolbox.
Leaked CIA Tools Linked to Known Cyber Espionage Group | Symantec
In-brief: We don’t know if the Vault 7 tools belonged to the CIA. We do know that they were used by a group Symantec dubbed Longhorn that possessed powerful zero day exploits, never attacked computers in the US and used code words taken from lyrics by 80s band The Police, so…