In this Spotlight Podcast, host Paul Roberts talks with Chris Walcutt, the CSO of DirectDefense about the rising cyber threats facing operational technology (OT) and how organizations that manage OT – including critical infrastructure owners can best manage increased cyber risks to OT environments.
critical infrastructure
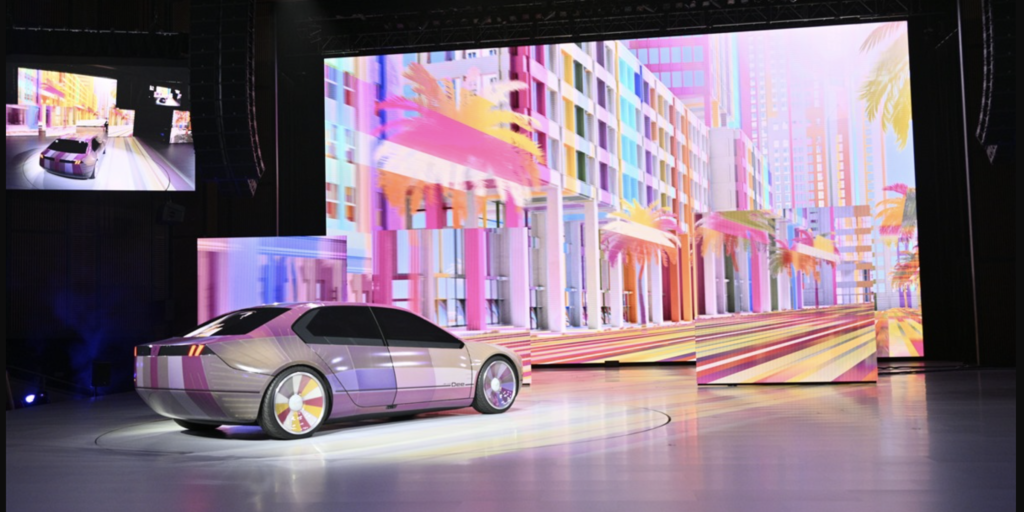
New Report Finds Auto Cyber Is A Dumpster Fire
Automakers swear that the security of their connected vehicles is their top priority. So how come researchers just found dozens of software flaws that could give hackers access to millions of cars?
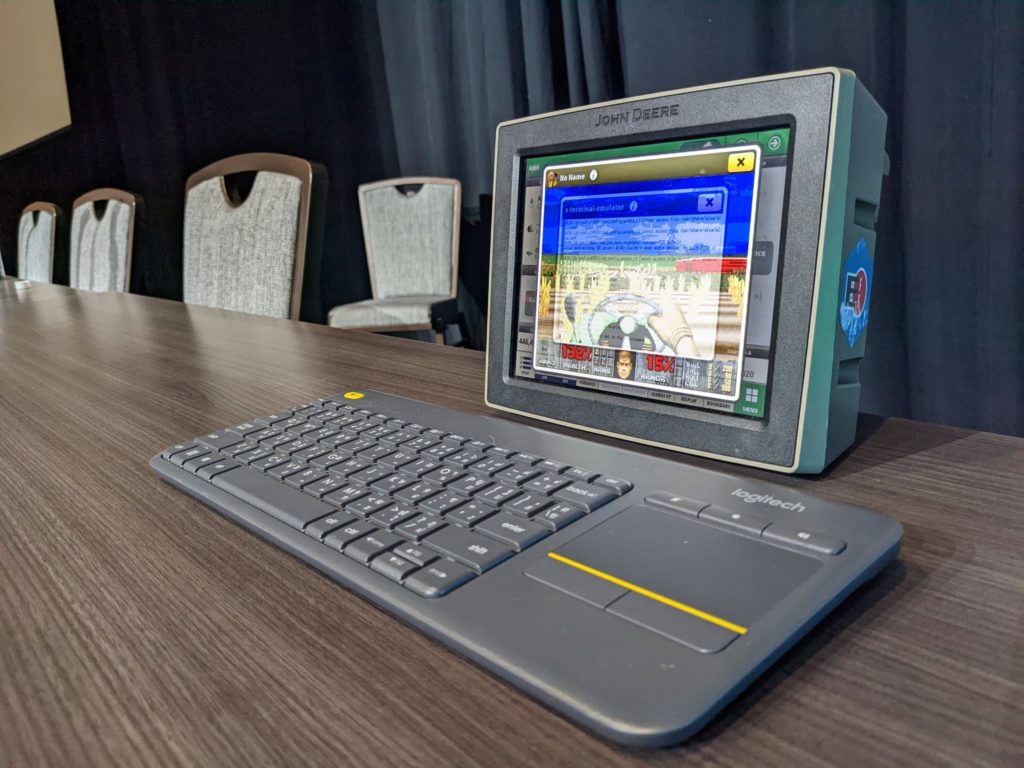
UPDATE DEF CON DOOM Patrol: Deere Jailbreak Raises Questions on Security, Competition
A researcher presented the results of a year-long effort to reverse engineer John Deere hardware to run a version of the DOOM first person shooter. He also discovered a number of security flaws along the way.
Episode 240: As Stakes Grow, Cyber Policy Needs to “Shift Right”?
In this episode of the podcast (#240) Lauren Zabierek, the Executive Director for the Cyber Project at the Belfer Center at Harvard’s Kennedy School joins us to talk about the need for a re-think of national cybersecurity preparedness, as major hacks like the attack on Colonial Pipeline put the focus on resilience and public safety.
Cyber Attack Halts Production at Ag Equipment Maker AGCO Fendt
A cyber attack has disrupted the operations of AGCO/Fendt, a major manufacturer of agricultural equipment, the company has acknowledged.