Organizations lost $2.7 billion to Internet-enabled theft, fraud and exploitation in 2018, with business e-mail compromise scams resulting in the highest of these financial losses, according to the FBI’s Internet Crime Complaint Center (IC3).
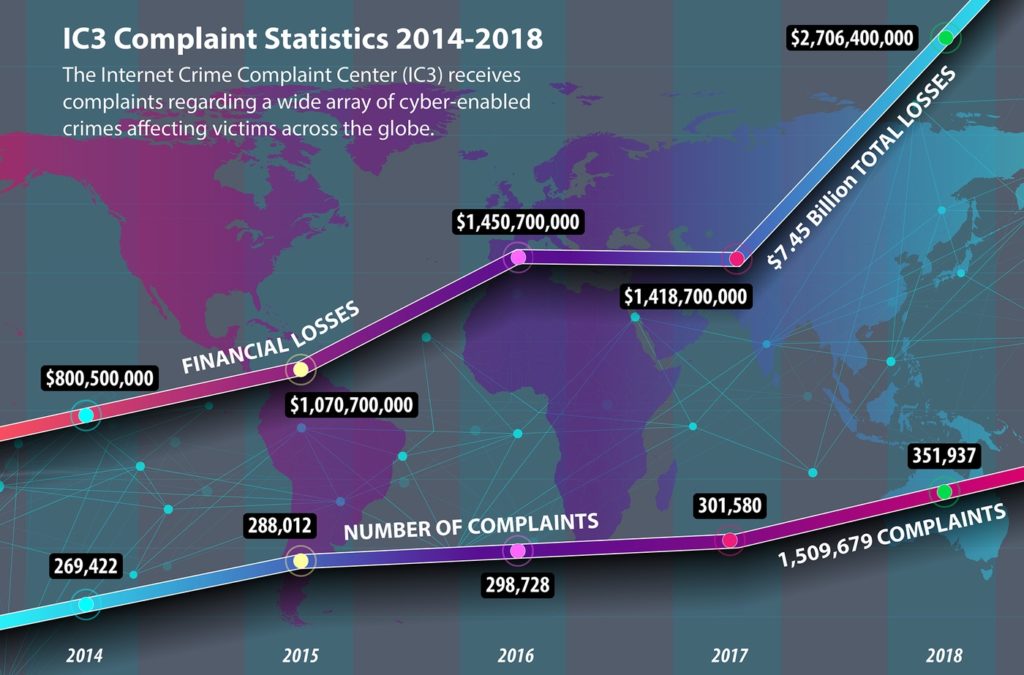
IC3 published its fifth 2018 Internet Crime Report this week, and the news was not good. The annual report detailed a steady uptick in complaints about cybercrime and a whopping $7.45 billion in cumulative losses since the center began tracking and reporting these complaints in 2014.
IC3 works with the public to track Internet-facilitated criminal activity and then reports those findings to the FBI. In 2018, IC3 received a total of 351,936 complaints, about 50,000 more than the year before. The complaints have been climbing steadily every year despite increased security awareness and an ever-growing number of cybersecurity tools on the market to protect against Internet-based criminal activity.
Report: Bad Bots sent One in Five Web Requests in 2018
The findings suggest that organizations and individuals aren’t protecting their data and systems as well as they could be given the solutions available to them, said Adam Laub, senior vice president of product management for STEALTHbits Technologies, who compared cybersecurity protections to driver safety.
“As the findings demonstrate, there are a wide variety of ways in which cyber crimes are committed–from sophisticated technical techniques to attackers preying on the misplaced trust of unsuspecting victims,” he said.
Easier said than done
That may sound easy, but it’s not. The latest IC3 report shows a diversity of Internet-related crimes that are claiming victims, with some taking a higher toll than others.
In 2018, business e-mail compromise scams were a top threat along with confidence/romance fraud, in which scammers set up trust relationships with someone and then exploit that to steal sensitive data. Non-payment and non-delivery scams were another major problem. In those scams, a person or business ships goods to someone in an Internet transaction and does not receive payment, or pays for something that is then never delivered, according to the report.
Extortion of money or property through intimidation or threats, and personal data breaches that expose sensitive, exploitable information were the most prevalent crime types that victims reported to the IC3 in 2018.
The range in types of attacks and their increased sophistication makes it difficult to defend against them, Willy Leichter, vice president of marketing for application security firm Virsec, told Security Ledger.
Podcast Episode 132: NERC issues a Big Fine – does it matter?
“Part of the problem is that we’re always playing wack-a-mole, trying to find the sources of attacks which are constantly shifting and changing,” he said. “The fact is that chasing threats and finding attributions rarely accomplishes the desired results.”
Now for some good news
The report did shed new light on positive outcomes in 2018 through a new service that helps victims who were defrauded by Internet crime. Last year the IC3 established a Recovery Asset Team (RAT) to act as a liaison between the FBI and financial institutions to recover funds for victims who made transfers to domestic accounts under fraudulent pretenses.
The report shows that of the $2.57 million lost in 1,061 incidents RAT handled in 2018, $1.93 million, or 75 percent, of funds were recovered for victims affected.
The IC3’s work also has produced a number of successful investigations that resulted in bad actors being identified and arrested or their actions thwarted, according to the report.
Three areas in particular in which the agency has made inroads to halt Internet-based criminal campaigns include payroll diversion, in which phishing campaigns are used to gain access to payroll log-in credentials; tech support fraud, in which bad actors attempt to gain access to a user’s device by offering help to solve a technical problem; and extortion.
Long road ahead
Despite these wins, however, security experts overall believe organizations users have a long way to go to stop such Internet-facilitated crimes that require FBI intervention from happening in the first place.
“This is going to be an endless game of cat and mouse,” said Byron Rashed, vice president of marketing, at network cybersecurity firm Centripetal Networks. “One side will gain advantage over the other and then vice versa.”
Rashed has a pessimistic view of the average Internet users’s ability to protect against sophisticated and organized cyber crimes.
“Although cybersecurity awareness has increased in Internet users, most don’t even know the basics or what to look for to identify threats or possible threats–phishing, basic security in open networks, malware, etc.,” he said. “Many either still don’t have endpoint protection, or they fail to keep it updated against the most current threats.”
George Wrenn, CEO of risk-management firm CyberSaint Security, echoed Rashed’s sentiment, but said it’s not only users who remain unprotected, but also businesses who should have a stronger security posture.
“I think that although there has been increased awareness, there have been so many point solutions, that integrating security risk, compliance, best practices into a security program–especially one that relates to business objectives–has been difficult,” he said. “Without a truly integrated and measured program with clear communication, it is difficult to manage the increasing amount of activity regardless of security teams’ awareness of it.”


Pingback: New IoT Security Regulations on Tap in U.S., U.K. | Raymond Tec
Pingback: Do Cities deserve Federal Disaster Aid after Cyber Attacks? | Raymond Tec