Security reporter Brian Krebs has an intriguing post from Sunday that suggests a link between the massive breach at Target Stores in late 2013 and the recently alleged compromise of systems at home improvement giant Home Depot.

Home Depot has yet to acknowledge any theft of customer data from its computer systems. However, according to Krebs, an unnamed “source close to the Home Depot investigation” told him that an analysis of compromised computers at Home Depot revealed that some of the store’s registers were infected with a new variant of BlackPOS, a malicious software program designed to run on Windows-based point of sale (or POS) systems and steal card data when cards are swiped.
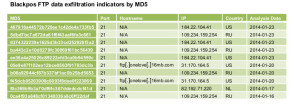
BlackPOS was found on point-of-sale systems at Target last year. In March, the security firm Arbor Networks issued a report that cited BlackPOS as one of a number of point of sale system malware families that cyber criminal groups were using heavily: generating new variants on an almost daily basis. Arbor researchers also documented specialized hacking tools for PoS systems, including software to ‘brute force’ compromise PoS terminals.
Krebs reported last week that cards apparently stolen from Home Depot shoppers were turning up for sale on Rescator[dot]cc, an online cybercrime shop that sells stolen credit card information. The same site offered millions of cards stolen in the Target attack for sale. In recent days, new ‘dumps’ of stolen credit card numbers were published using the brand “American Sanctions” – an apparent jab at U.S. sanctions against Russia for its actions in Eastern Ukraine.
According to Krebs, clues buried within this newer version of BlackPOS support the theory put forth by multiple banks that the Home Depot breach may involve compromised store transactions going back at least several months.
Read more via Home Depot Hit By Same Malware as Target — Krebs on Security.

